Memetic Warfare Weekly: Tasteful Binary
Welcome to Memetic Warfare Weekly.
My name is Ari Ben Am, and I’m the founder of Telemetry Data Labs - a Telegram search engine and analytics platform available at Telemetryapp.io. I also do training, consulting and research so if you have any specific needs - feel free to reach out on LinkedIn.
Prior to beginning this week’s post, I’m announcing this casually here - I have an upcoming remote (accelerated) course planned for July 24-25 on investigating influence operations.
I usually do more in-person training for companies/organizations, but after receiving interest I figured why not see if there’s any interest in opening up spaces to the public for future courses. If there’re enough people interested, I’ll open an additional course - so if of interest, message me on LinkedIn or at ari@telemetryapp.io.
Note that this course is usually 4± days, and that I provide it in-person as well as remotely. Now that that’s out of the way, let’s start this week.
Remember how last week I said that, overall, there appears to be better basic OpSec practices for Iranian influence operations?
Well, while that still remains true, I’ve since spent more than several hours (I usually only get the chance to spend a few hours a week writing this blog) looking at Dofek and have come across at least one case of Arabic script being used for a file name. The script is mostly the same between Persian and Arabic, but the grammar here used is Arabic - Persian speakers, feel free to interject here and send me your opinions.
This is a similar slipup to past operations and not shocking to say the least, but having slipped up “only” once with a file name, or so it seems here, is still comparatively better than other operations.
Additionally, it appears that they’re backdating content as per the upload date in the WordPress folders for whatever reason.
This matches up with there being at least one page manager in Lebanon as shown last week, so it could be possible that the whole operation is outsourced to an Iranian proxy, run jointly, or alternatively isn’t Iranian. Any input on this one? Let me know at ari@telemetryapp.io.
Tasteful Binary
Microsoft’s MTAC published their recent threat report on East Asia available here with what I’d call “tasteful binary” on its front page. It’s well-done, as usual, and there’s more to it that I don’t cover below, so give it a read.
I’m not usually a stickler for definitions, but I would be curious to hear more about how Microsoft views the operation and its relations to China. Are we talking directly related, outsourced, tacitly encouraged? I imagine that Microsoft probably has some internal telemetry on this that they can’t share, but it’d be interesting to get some more insight specifically on this.
Later on this gets even more specific, with the report claiming that Storm-1376 is CCP-linked. More context would be great on this!
On another note, while I’m fine with each company having their own naming structure despite having made fun of it in the past, it’s definitely time to have MITRE or someone else begin independently tracking threat actors and giving us general, universally-relevant names. Personally I liked the previous Miburo designation of APMs but I’d settle for any shared name at this point.
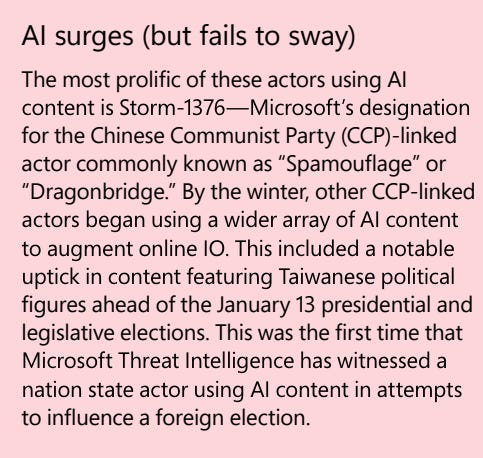
The section on generative AI pleasantly surprised me overall, finding and tracking the individual cases in which it was used. Examples that I didn’t come across myself in my very, very limited look at the elections also came up, such as AI-generated audio clips of Terry Gou and a forged letter:
The use of generative AI is noteworthy also in the context of how it, and other Chinese content, was seeded. The TAs in this case seeded on hacking forums, created forgeries and so on: this is a step up in terms of both general sophistication and also "impact” for lack of a better word. I also like the differentiation between amplified by/created and amplified by.
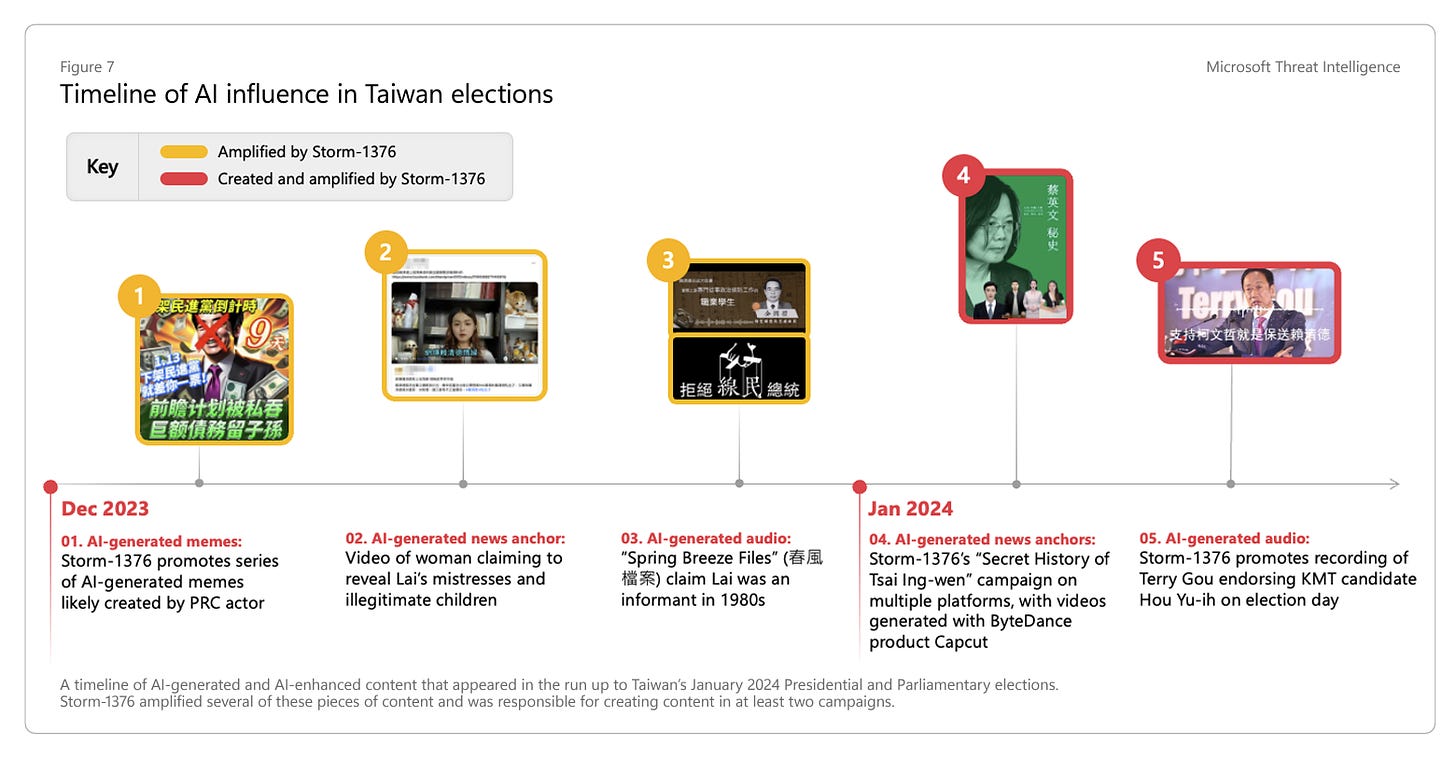
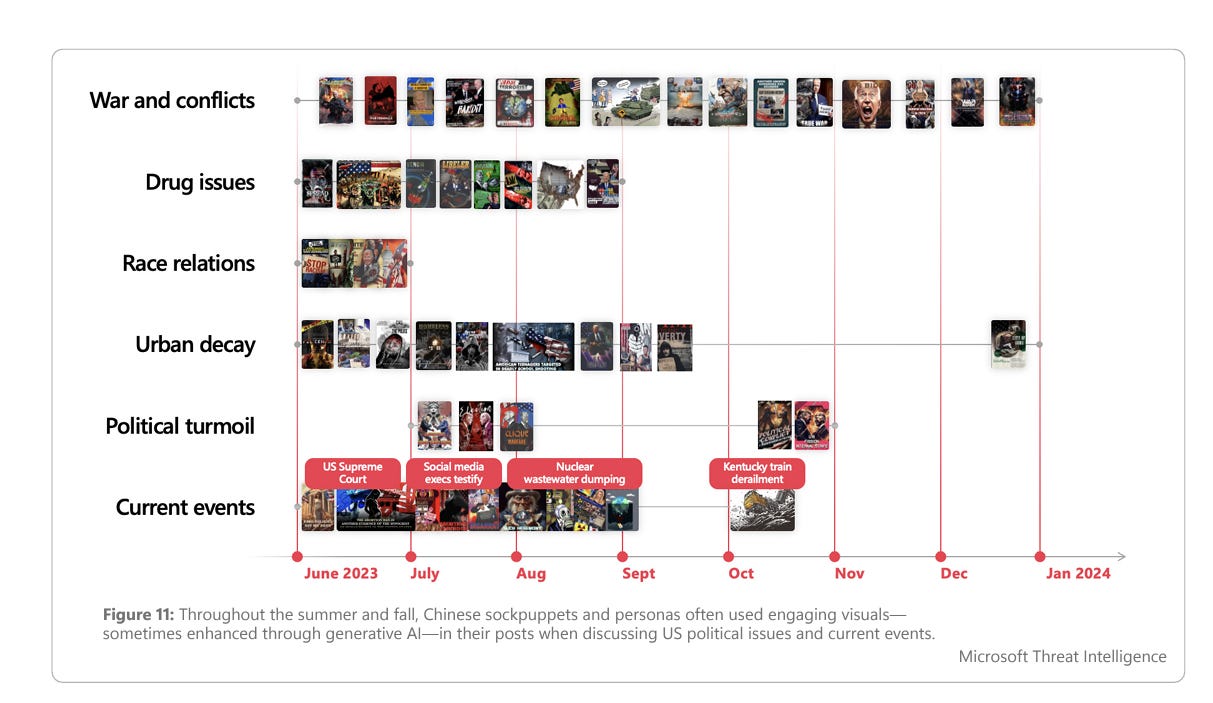
I don’t usually emphasize content analysis in networks but the below timeline with images is quite effective:
Microsoft it also appears is calling out Zhang Meifang here (original post available here).
I was very happy to see an emphasis on local platforms, such as the emphasis placed on South Korean platforms, as this is something that is still more often than not lacking:
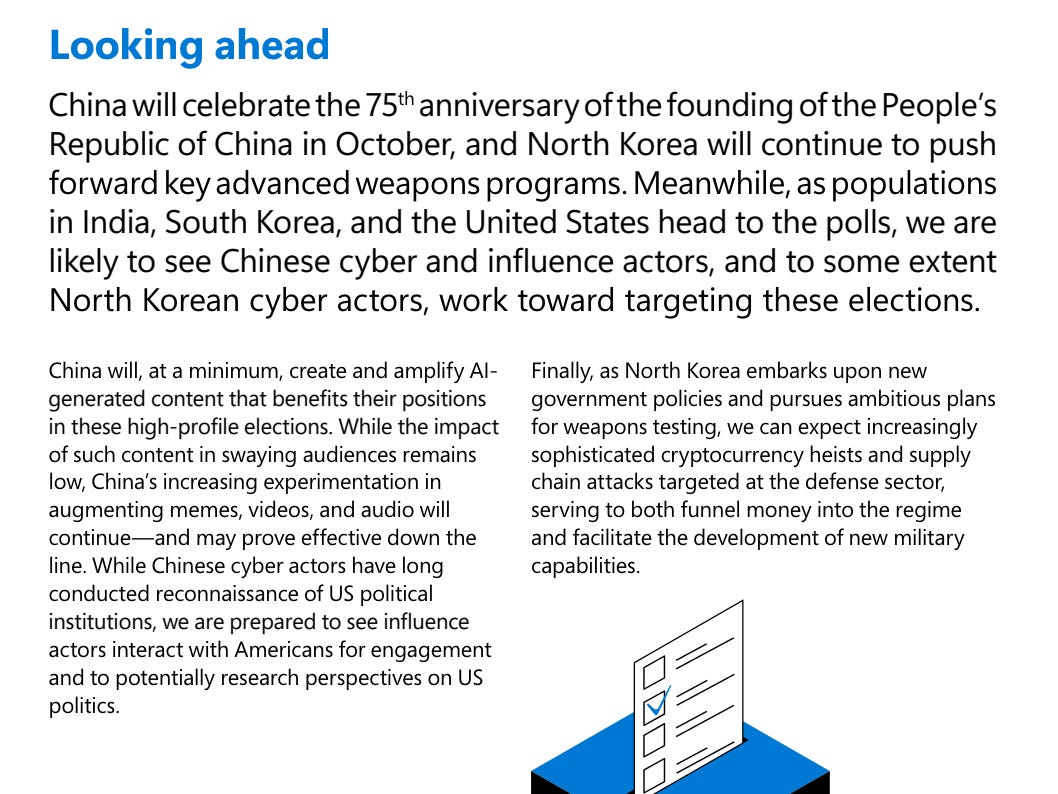
The predictions section acting as a conclusion to the report in my opinion is straightforward and on the money. I won’t comment on the NK section as frankly I don’t follow it at all
I’m personally not so sure that we’re going to see any activity “prove effective” in the near-term (gen-AI excluded) as threat actors truly have proven time and time again that they’re not capable of learning the basics, but there’s no question that deepfake audio/video now could probably fool a solid chunk of the American populace.
Procurement Enjoyer
OFAC announced some noteworthy sanctions the other day, available here.
Interesting to see sanctions for “cyber influence” in perhaps the broadest of terms. Abu Ubaida apparently was active not just in uploading videos but also in server procurement and domains (not necessarily the hardest of lifts when done in Iran).
Hamas is active in general propaganda/psyops (which they handled quite well in the initial few days of the war and beyond) as well as some cyber activity, but what does “cyber influence” mean here? Was he directly involved in operations beyond being the spokesman? A few additional sentences here could’ve been enlightening.
That’s it for this week!