The Misattribution of Laury[phoo]n Hill
Welcome to Memetic Warfare Weekly.
My name is Ari Ben Am, and I’m the founder of Telemetry Data Labs - a Telegram search engine and analytics platform available at Telemetryapp.io. I also do training, consulting and research so if you have any specific needs - feel free to reach out on LinkedIn.
China’s CVERC (Computer Virus Emergency Response Center) has published quite the report on “Volt Typoon” activity and their “unique”, let’s say, perspective on it. The original English Twitter post is available here, and an archived version of the English document here.
Interestingly, the CVERC only pops up every once in a while whenever it has some questionable reports about American activity. At its core, the CVERC is the central body for Chinese disinformation and influence on cyber activity, a phenomena which Dakota Cary has discussed in the past and I’ve commented on as well.
This post will be a bit long so I’ll TL:DR it here for you: The report claims that Volt Typhoon isn’t a Chinese government-affiliated hacking group, but rather a ransomware gang or cybercriminals.
The report reaches this claim by looking at 5 IP addresses that Typhoon Volt file hashes contact, and then makes the wild jump of stating that those IPs, which are cloud hosts, are tied to past cybercriminal activity and thus not related to China.
This is, unsurprisingly, incorrect for reasons that we’ll discuss below. On that note, let’s begin.
The report first came up when CVERC tweeted a link to it, alongside what appears to be an AI-generated image of boilerplate suits:
The report itself was also promoted heavily by Chinese state media outlets with the same narrative and keywords:
Leaving aside the questionable house of cards-esque styling and lighting choices, the thrust of the report is of interest.
This report is a great example of deflection: Volt Typhoon isn’t government-affiliated, it’s just a ransomware group/financially motivated group. Let’s take some time and look at the report.
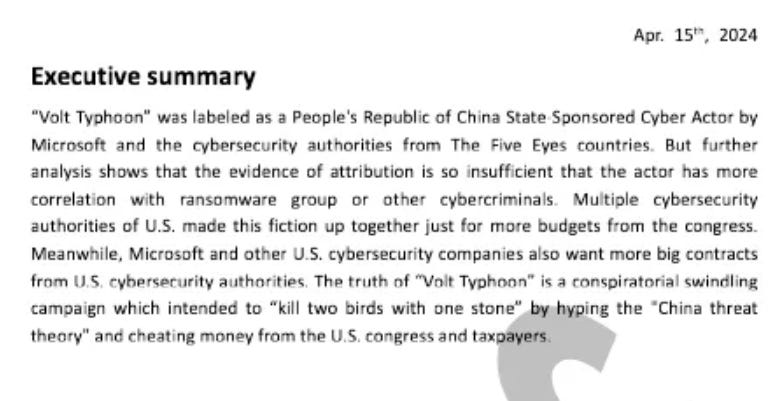
Firstly, credit where credit is due. The executive summary is short and to-the-point:
They’re really “cooking with gas”. Not only is the CVERC denying that Volt Typhoon is affiliated with the Chinese government, they then make some great counterclaims:
The attribution of Volt Typhoon is “insufficient” and that the group is in fact just a bunch of cybercriminals
Cybersecurity firms make up “fiction” for more “budgets” from Congress
The American narrative about Volt Typhoon is an information operation meant to amplify the “China Threat theory”
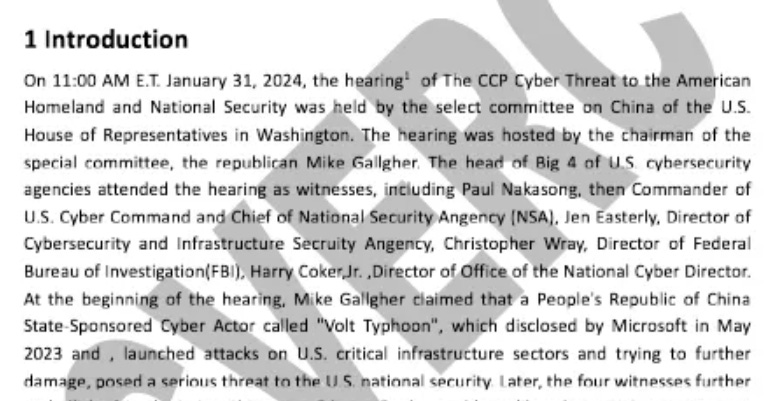
The level of professionalism in the report is wanting, to say the least. The opening paragraph after the executive summary is really typo-maxxing here, humorously misspelling Nakasone as Nakasong, Gallagher, Security, Agency and so on.
The grammar and style issues also, of course, abound. Strong start, to say the least. I’m not one to usually make fun of how non-native speakers speak and write in English, but in this case it’s warranted.
Let’s move on, and I’ll save you the overly long-winded explanation of LOTL and move on to the next paragraph of note:
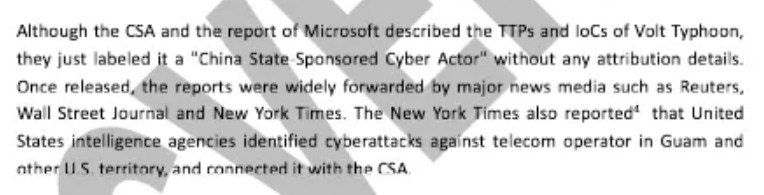
“They just [labeled] it a “China State-Sponsored Cyber Actor” without any attribution details”. Preach gurl! I too hate it when people don’t share sufficient technical indicators!
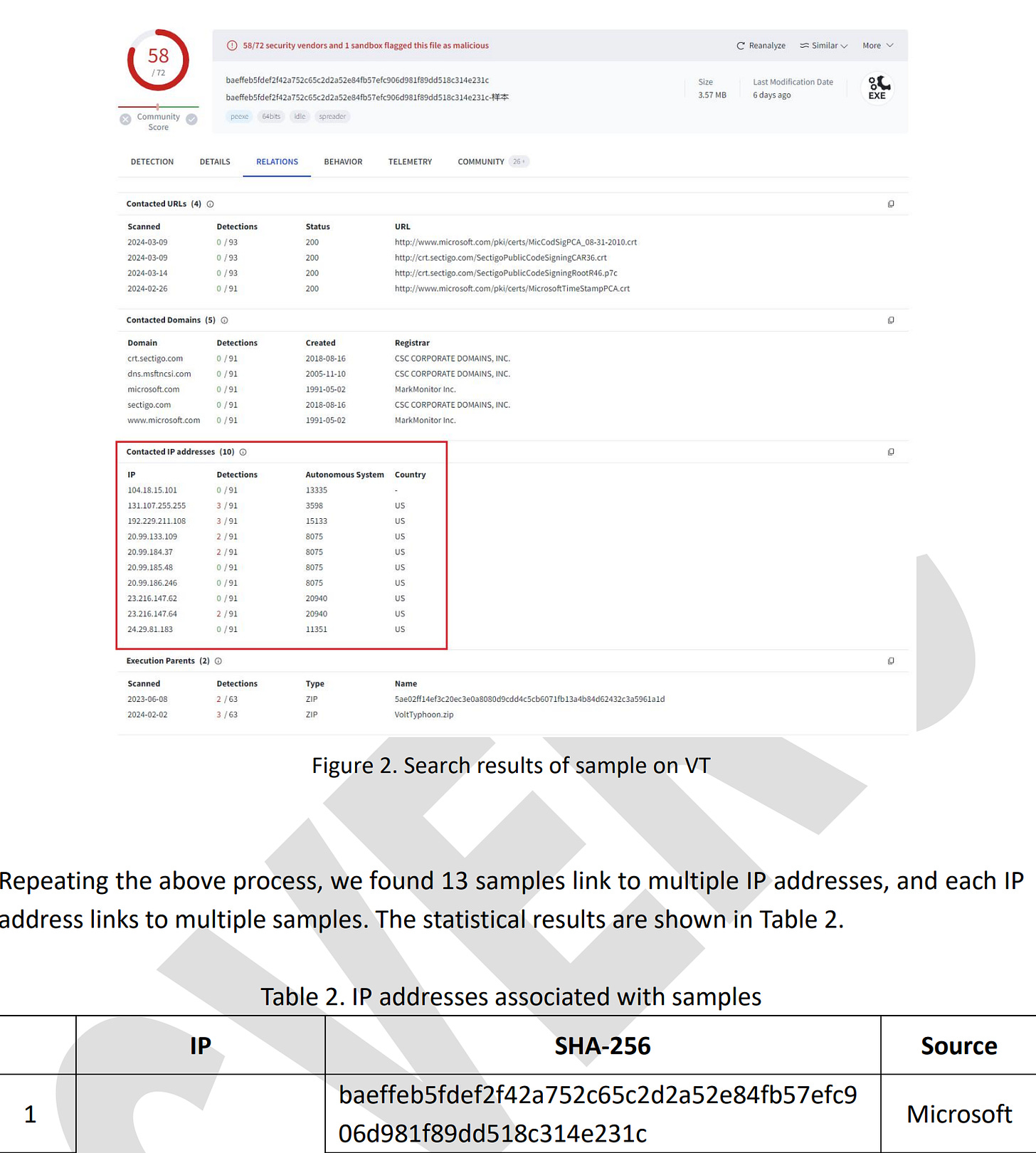
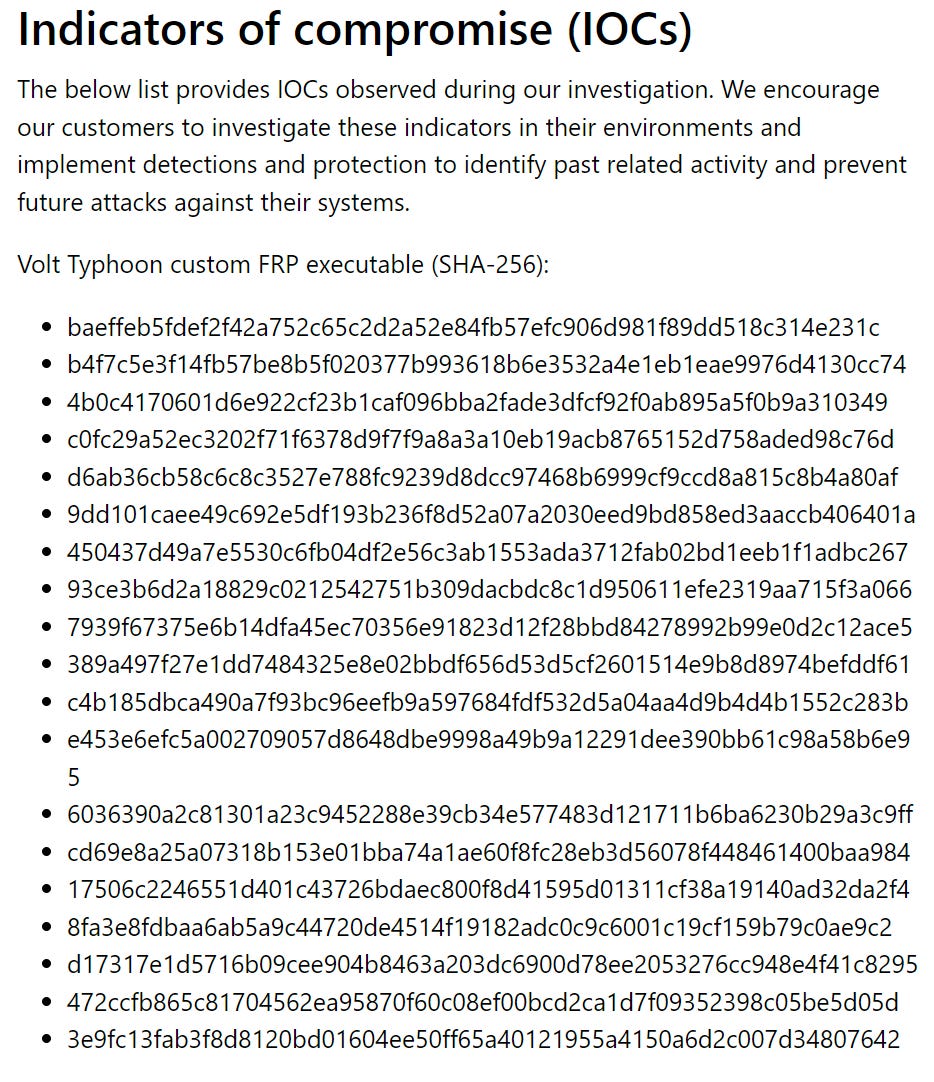
The report, having staked out its position, moves on to support the claim that the Volt Typhoon was misattributed by analyzing IoCs via what else but VirusTotal. The report thus begins with a screenshot of VirusTotal results for one of the file hashes affiliated with Volt Typhoon by Microsoft, shown to identify the IP addresses contacted by the file:
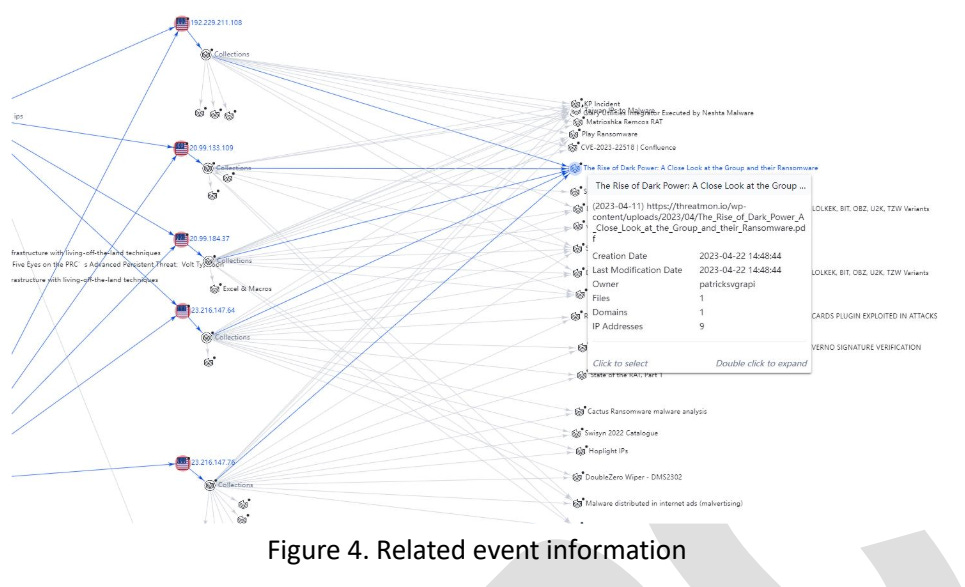
The report aggregates the hashes by the IP addresses that they contact, but only does so partially, providing only 5 IPs in total - see the below sample. The IPs provided are:
23.216.147[.]76
23.216.147[.]64
20.99.184[.]37
20.99.133[.]109
192.229.211[.]108
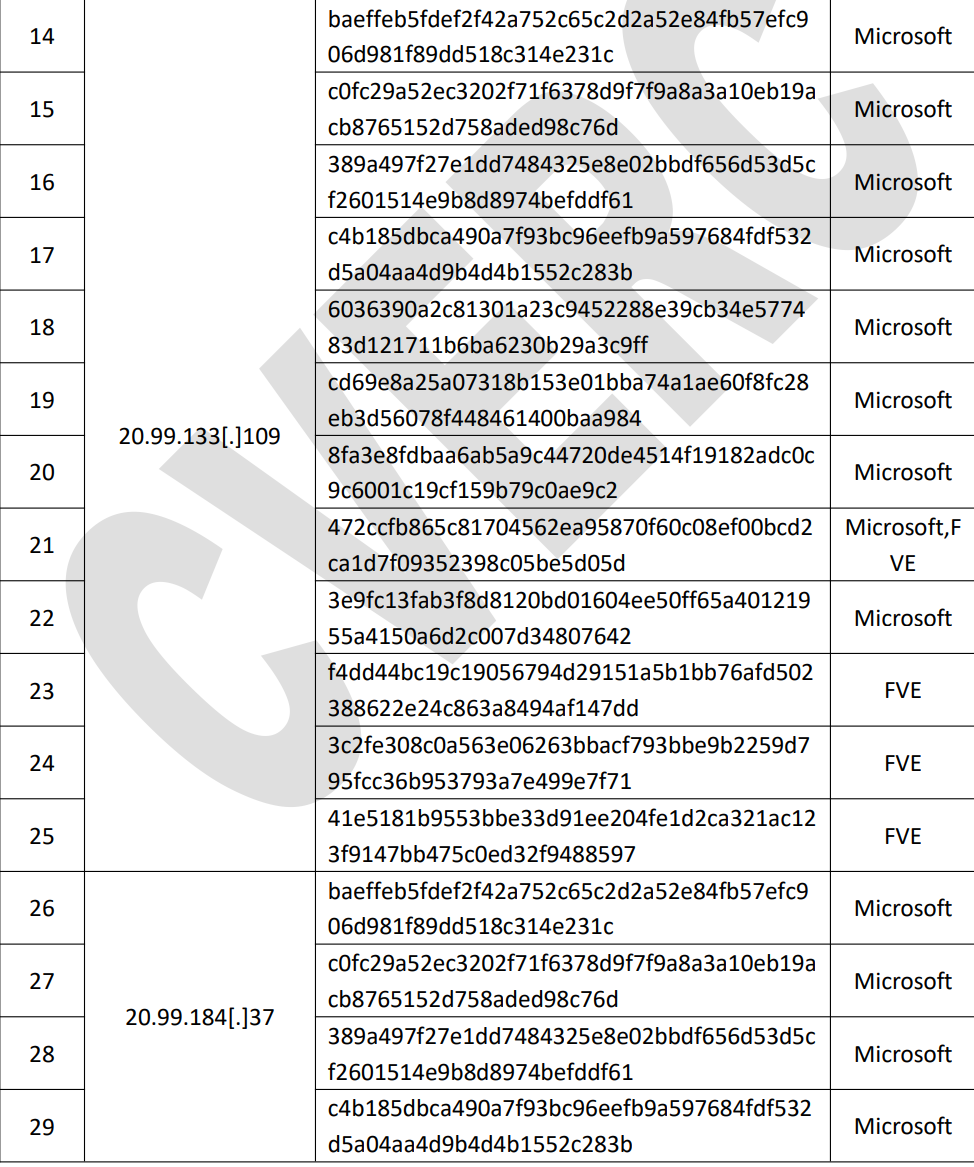
The report then looks at all of the file hashes shared by Microsoft, available here, in order to see which malware samples contact which IP addresses.
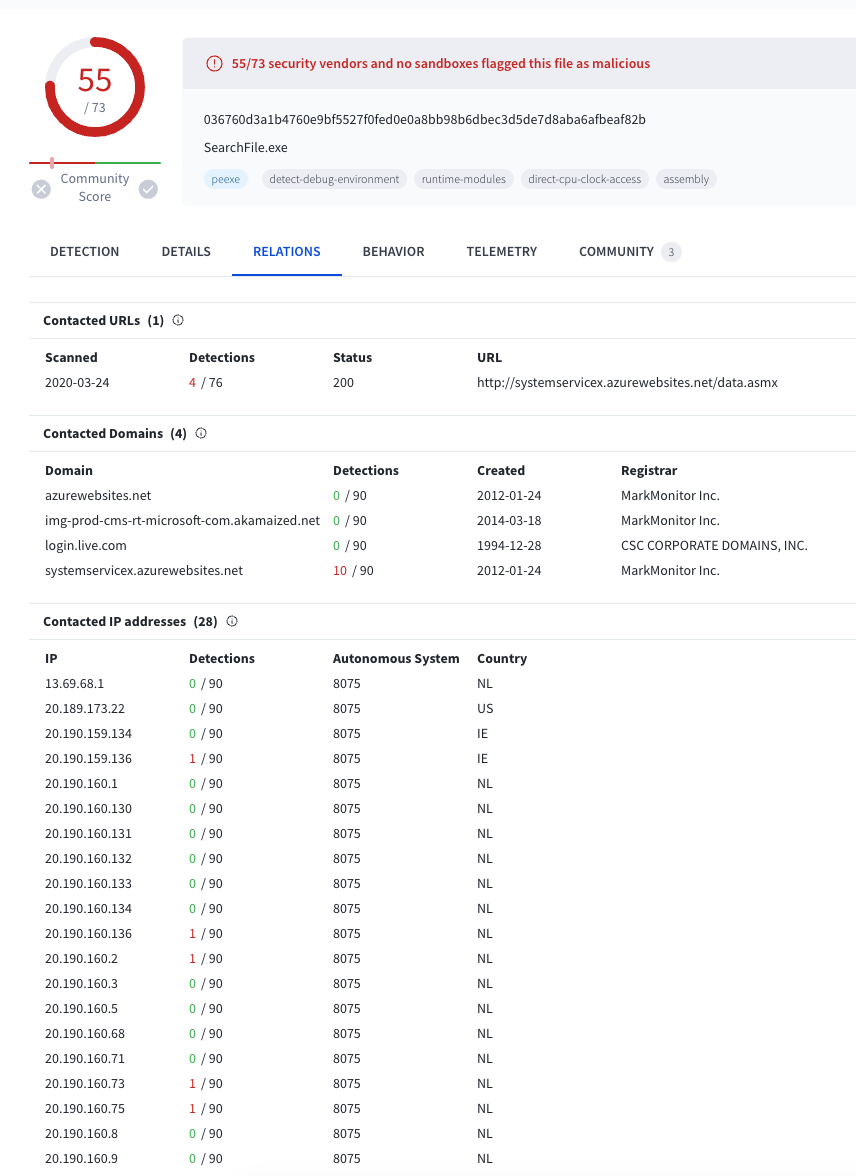
Looking at one of the files, “c0fc29a52ec3202f71f6378d9f7f9a8a3a10eb19acb8765152d758aded98c76d”, shows that it has contacted at least 16 IP addresses in the past, many of them being cloud hosting servers, with the majority being in the 20.190.159 range, an AS belonging to Microsoft Azure.
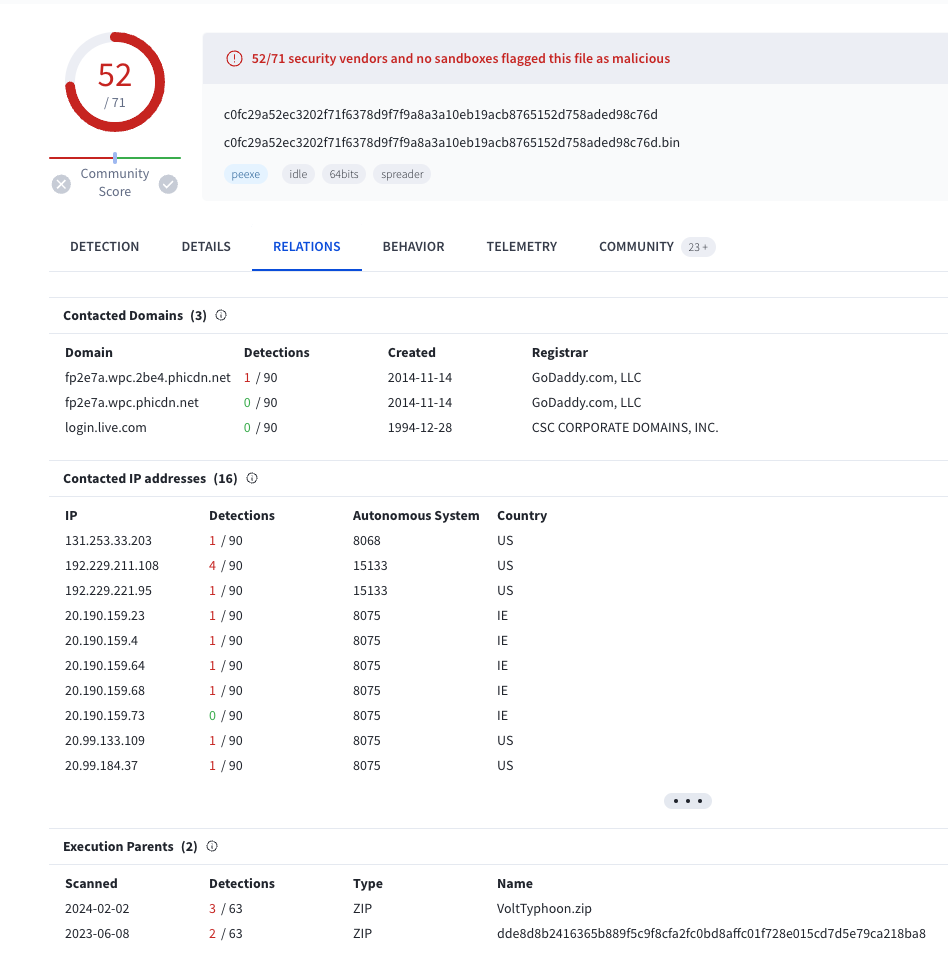
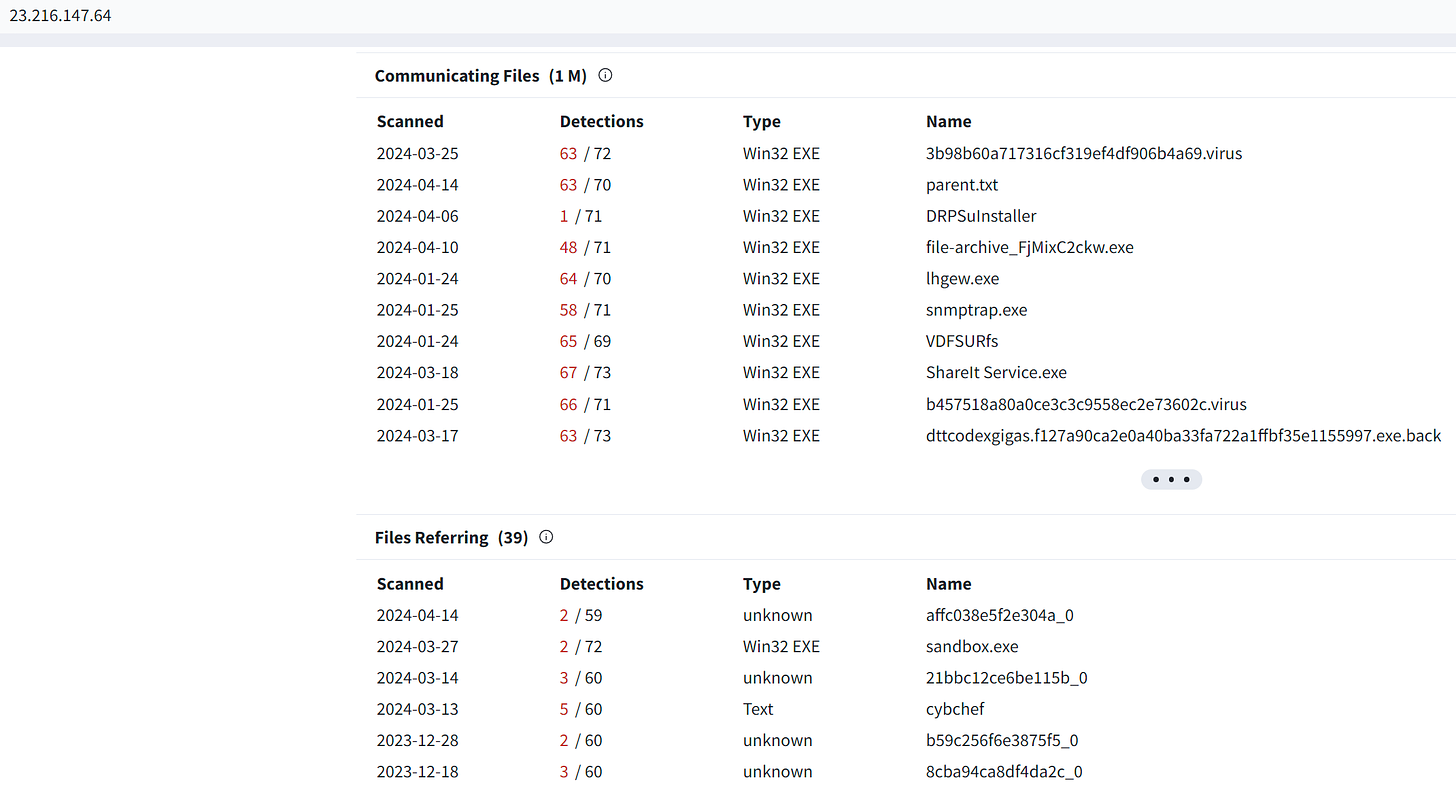
Looking at another one, this time an IP hosted by Edgecast, a CDN provider, we see that it has over 1m communicating files - no small number to say the least.
To sum up, the report selectively looks at 5 IP addresses that communicated with malware samples in the above set, again, using the VirusTotal graph while excluding all of the other identified IPs AND also ignoring the massive scale of contacting files for some of them
. This greatly impacts the results, providing a smaller, selective dataset that makes it easier for the results to be manipulated below:
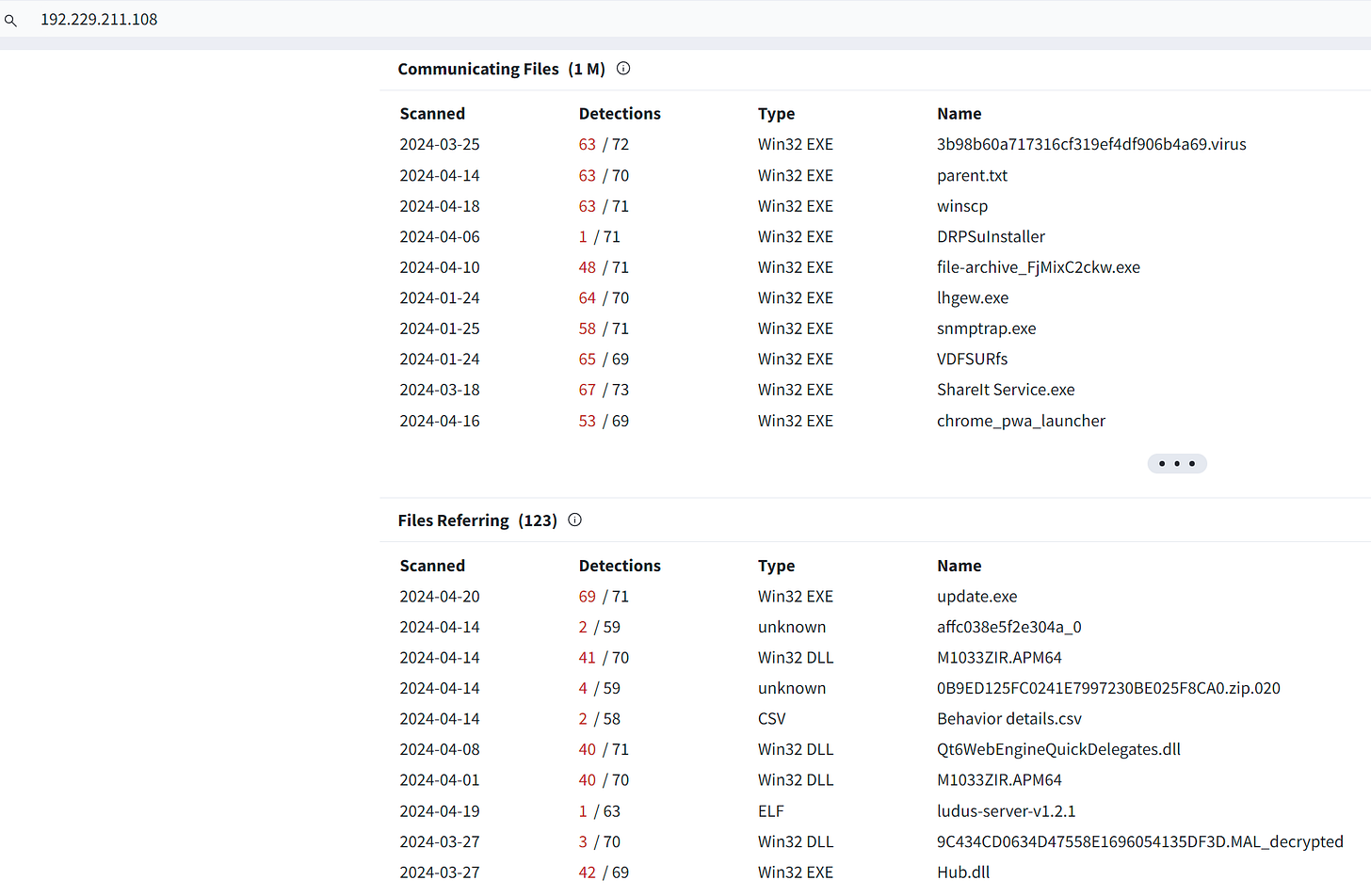
As shown above, the report chooses only to look at 5 of the IP addresses and sees that they’ve been affiliated with various attacks, but that the only one tying them together is the “Dark Power” ransomware group. As such, the report claims that this infrastructure is probably affiliated with Dark Power, or potentially other cybercrime groups.
What I don’t understand is why the report explicitly shows a greater number of IP addresses contacted than what they analyze. There’s no stated reason as to why some addresses are looked at, why others aren’t - I guess they assume no one actually checks what they write?
Let’s now take a look at those results. Note that there are multiple other affiliated criminal groups that have in some way contacted these IP addresses (which are Microsoft/Akamai owned as part of cloud infra).
So let’s summarize the CVERC’s claim so far:
The Volt Typhoon file hashes provided by Microsoft contact a number of IP addresses.
The CVERC report chooses to only look at 5 of the addresses, despite there being significantly more available.
These IPs have also been utilized by a number of threat actors in the past (as is expected from cloud infrastructure. This is not the first time that cloud infra has been exploited.)
Because these IP addresses have been utilized by past threat actors, and all have at one point apparently been utilized by Dark Power, it’s most logical that the Volt Typhoon files were created/used by a financially motivated threat actor, most likely Dark Power.
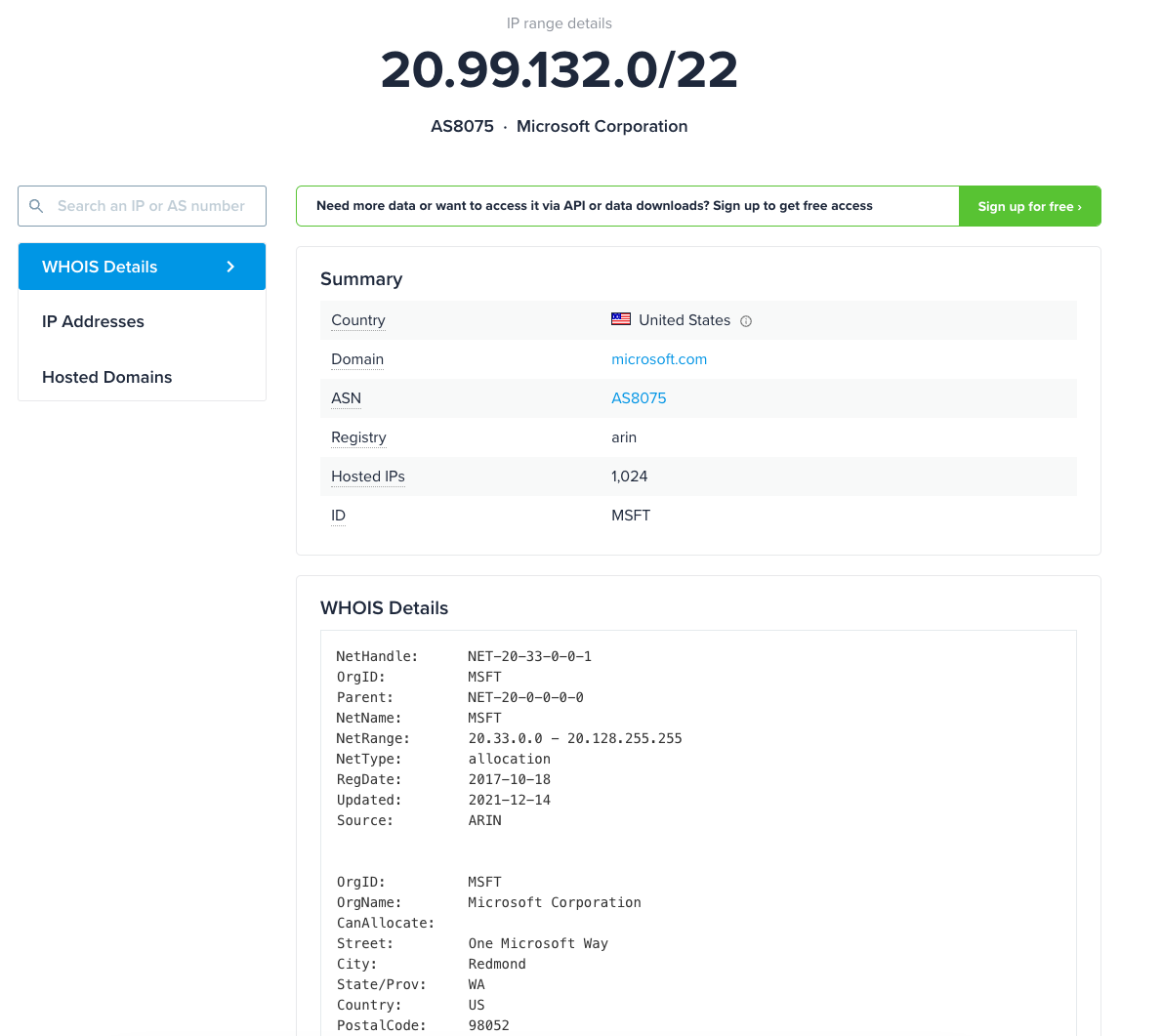
The report’s logic is very faulty, to say the least. Were these to be hosts set up in a proprietary fashion by a given threat actor, that’d be one thing, but we’re talking about shared cloud infrastructure here which is used by tons and tons of people and actors.
Cloud infrastructure at this scale can be and is utilized by many, many actors and threat actors. It’s quite feasible, to say the least, that state actors exploited Azure infrastructure for their attacks alongside tons of other threat actors and regular users.
Look at one of the IPs in the report - as per VT it communicates with over 1 million files and has 39 referring. This makes the CVERC claim far less convincing when you understand the context and that cloud infrastructure serves huge audiences:
I’m not just saying that though. There have been multiple cases of threat actors exploiting cloud and Azure infra from years past, see one Azure host exploited by threat actors below as an example:
So, it’s not at all to be unexpected that a malicious file contacts cloud infrastructure. Let’s confirm that the given IPs are in fact Microsoft cloud infrastructure:
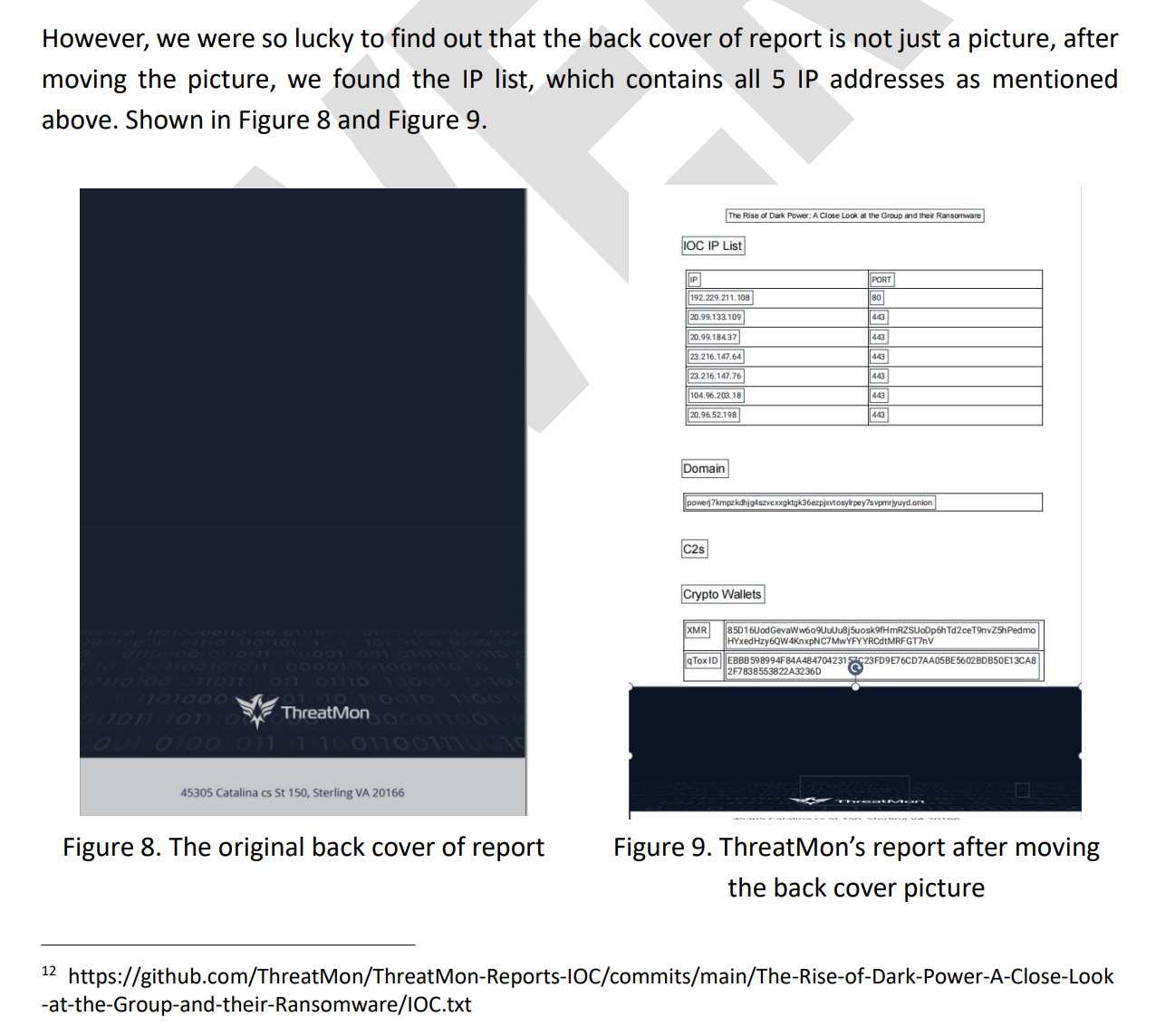
CVERC also tries to convince us that these IPs have appeared in a past threat report from ThreatMon on Dark Power, and thus that, in their professional opinion, it may well be Dark Power or any other ransomware gang.
At no point is there any reference to the true nature of these given IP addresses as cloud infra, their affiliation with tons of other threat actors, or even the nature of their contact with the file hashes.
The report then gets philosophical, and reminds us that everything happens for a reason:
What is the proposed reason then from CVERC? The first is political China-bashing, apparently.
The second is apparently the need for Microsoft and Lumen Technologies to justify their large orders from the US government by pushing them to publish reports denigrating China:
Funny stuff for sure. Following a rousing conclusion about the scourge of cybercrime, the report thanks Qihoo 360, without which apparently the Chinese government would be entirely bereft of anyone able to use VirusTotal.
It is now apparent that the US could strike at the heart of Chinese AV detection capabilities by simply preventing VirusTotal from operating with Chinese entities - who’d have thought.
Let’s take a look at social media activity. Crowdtangle were results were lacking, so I resorted to searching manually to see what’s up on Facebook and Twitter, for now.
Zhang Heqing is one of the most prominent sharers on Twitter, where it’s received surprisingly little artificial engagement, the original CVERC tweet has certainly not blown up.
The above CCTV video, shared by CCTV as well, introduces us to both CVERC engineers as well as a Qihoo analyst, which is interesting in of itself.
Some inauthentic accounts have shared it on Facebook, including one page, but overall - not promoted very heavily by inauthentic networks.
It has made it onto a far-left niche Italian site: chalk one up for CVERC!
The state media articles mentioned at the beginning, at least the ones I checked, weren’t amplified greatly also beyond a few cases here and there of inauthentic accounts.
To recap, this situation is reminiscent of past CVERC/Qihoo cases: shoddy to nonexistent or nonsensical technical analysis used to promote Chinese talking points, and in this case, presumable disinformation. That’s it for this week!