Welcome to Memetic Warfare Weekly.
My name is Ari Ben Am, and I’m the founder of Telemetry Data Labs - a Telegram search engine and analytics platform available at Telemetryapp.io. I also do training, consulting and research so if you have any specific needs - feel free to reach out on LinkedIn.
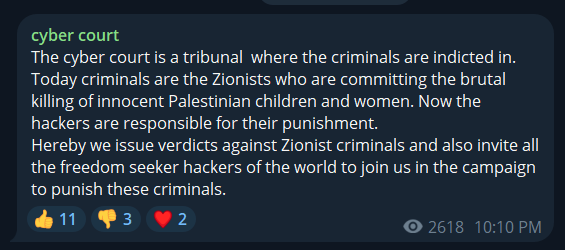
There’ve been some apparently significant leaks of Israeli government and corporate documents by various hacktivists as of late. Most interestingly, they’re being conducted under the auspices of the “Cyber Court”. See their raison d’etre below:
The group is active on this domain, Twitter and Telegram, and appears to serve as a clearing house for a motley assortment of hacktivist groups to post hacked content.
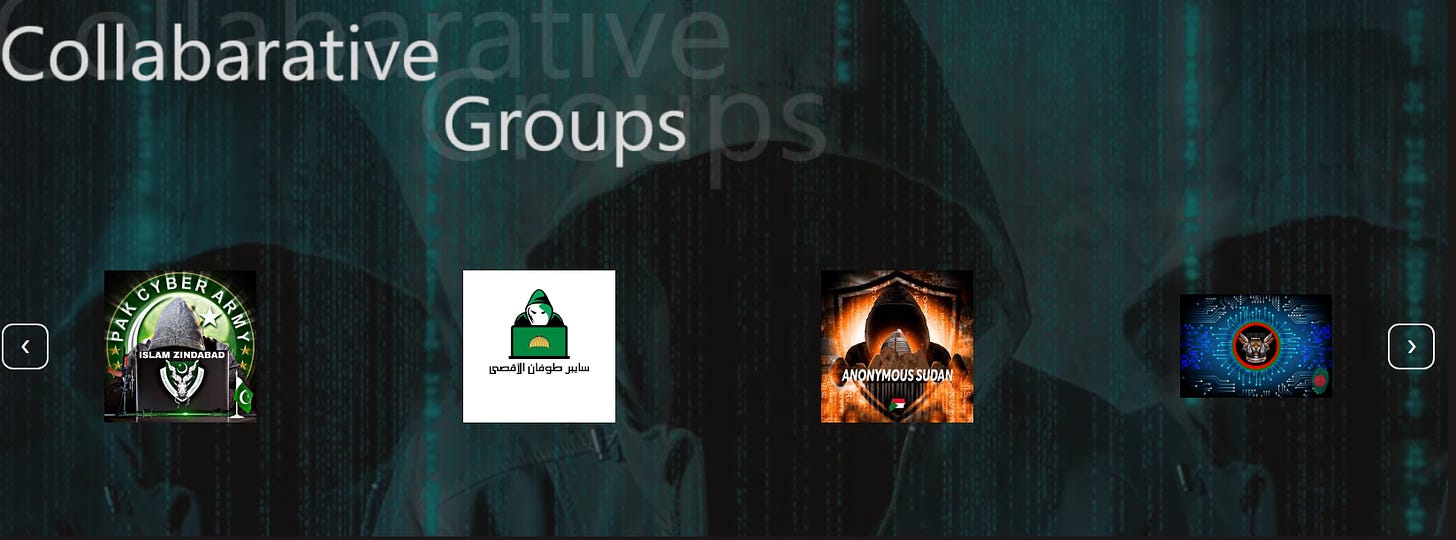
The domain’s hacktivist partners include some known TAs, such as Anonymous Sudan (believed to be Russian), Cyb3r Av3ngers (Iranian) and some lesser-known groups such as Mysterious Team Bangladesh, Makhlab al-Nasr, Net Hunter, the new “Anonymous South Africa” (wow, wonder who could be behind that one) and others.
The nature of the relations between these various groups and themselves, let alone the Cyber Court domain and its organizers, isn’t clear in its entirety. This wouldn’t be the first time that hacktivist groups/APT front groups have banded together publicly online as well, but it’s still a notable moment.
They’re web3 compliant and are out there girlbossing! This is the first time I’ve seen a hacktivist group use IPFS to host a domain but correct me if I’m wrong:
They include a QR code for IPFS access as well:
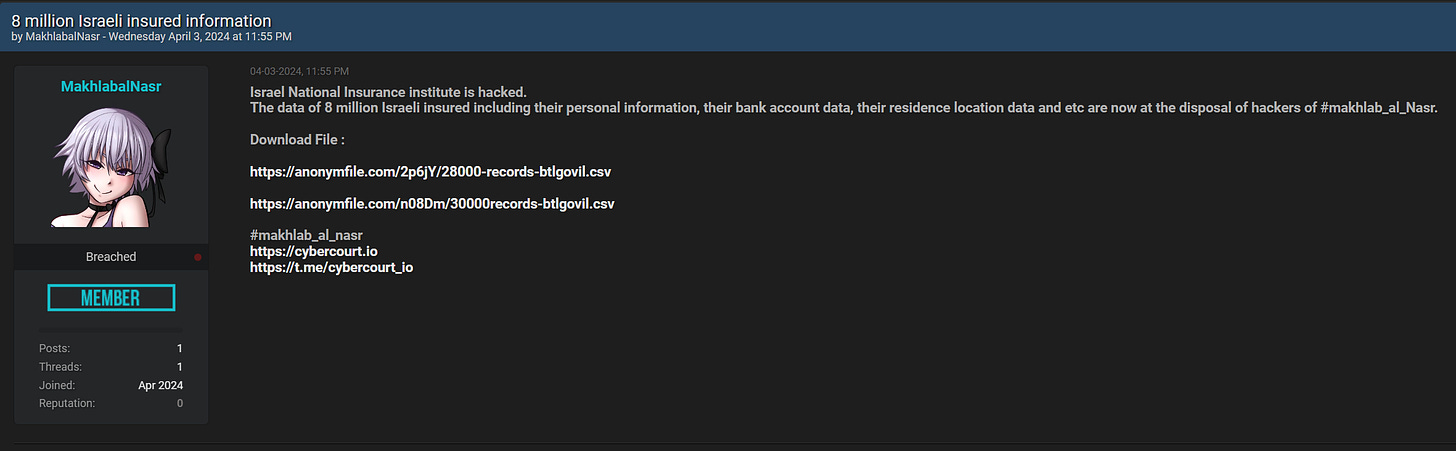
Makhlab al-Nasr has already posted an Israeli leak on Breachforums:
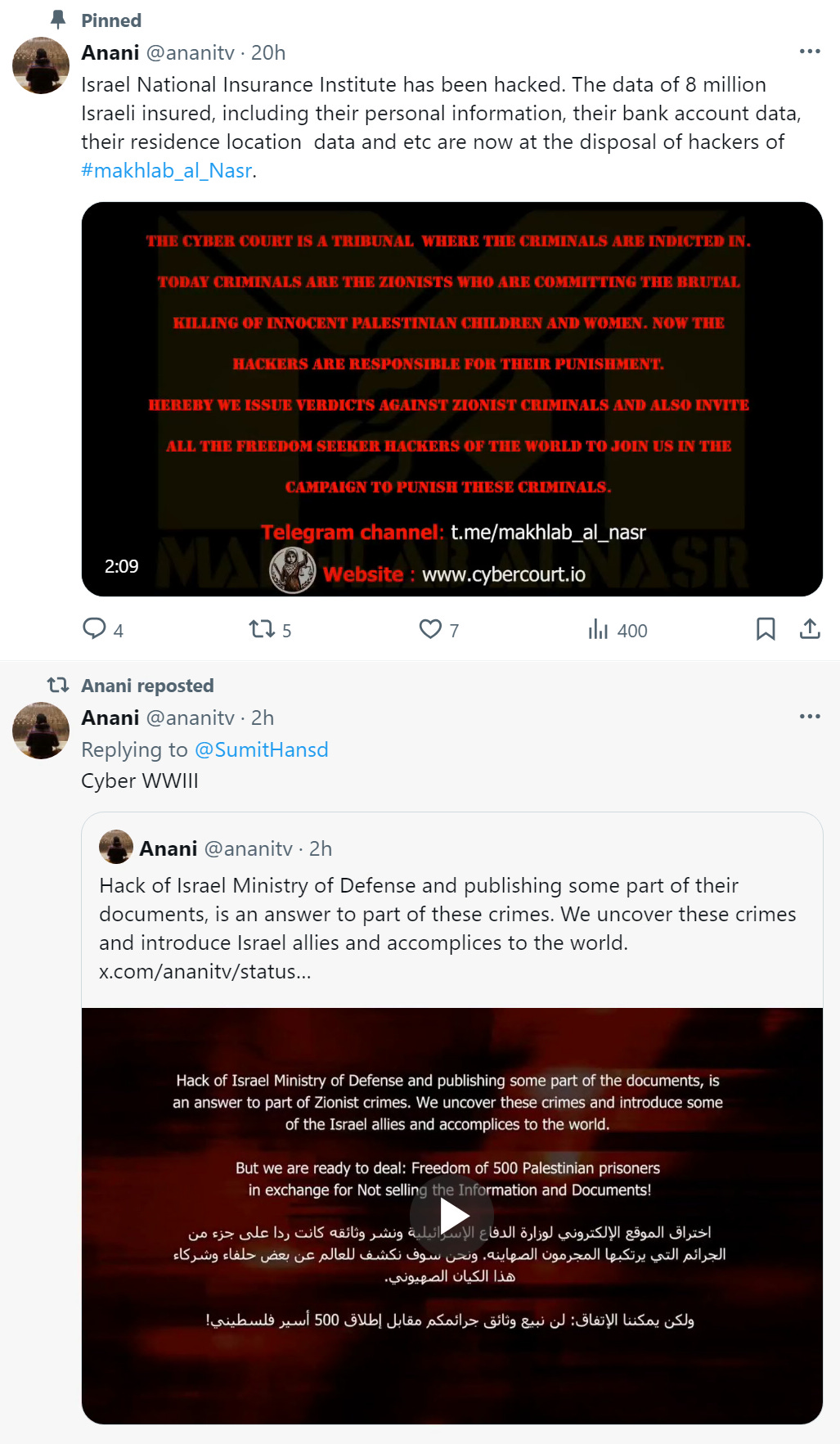
It wouldn’t be a hack and leak site without a few suspicious accounts promoting it:
Makhlab al-Nasr isn’t the only sub-group out there wildin.
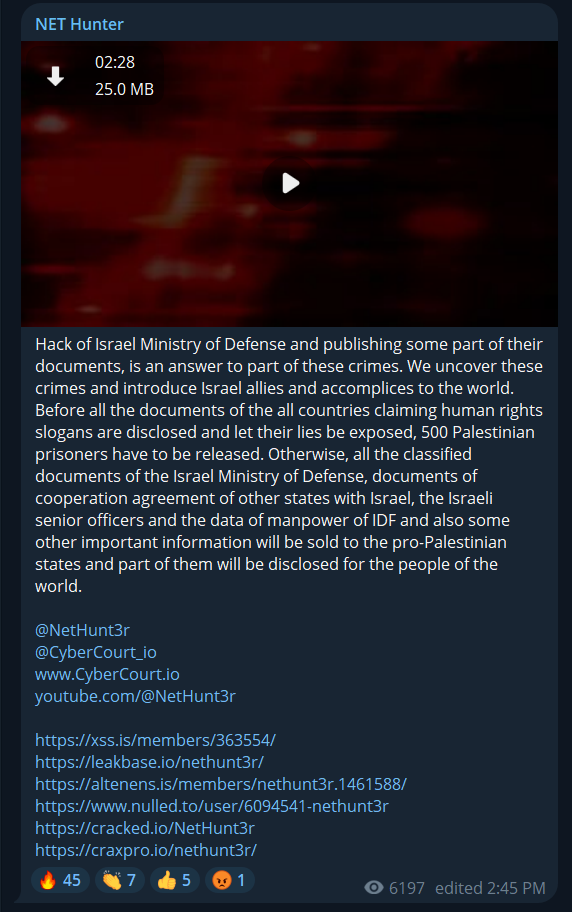
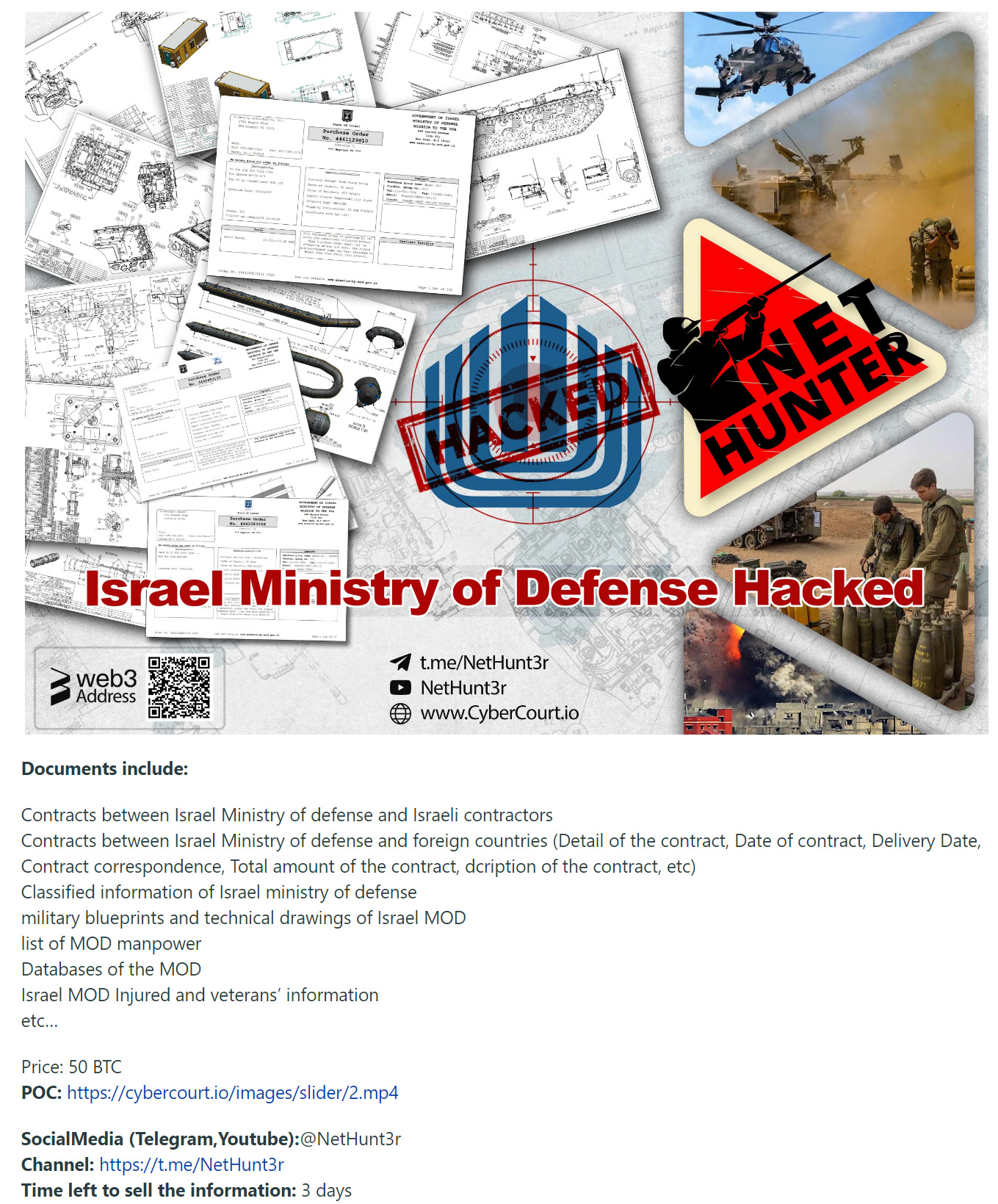
Nethunt3r, one of the groups involved in Cyber Court, allegedly breached the Israeli Ministry of Defense, and they’ve begun posting the leaks on Telegram and hacking forums such as Leakbase, Cracked, Nulled and so on:
Tasnim news (alongside other Iranian state media outlets) has already covered Nethunt3r:
Those interested in almost immediate Iranian state media coverage of hacktivist activity can check out my last blog post on Kargar and Rid’s article on Iran/Yemeni hacktivist groups.
In short - immediate amplification by state media is a common TTP of Iranian activity, and they even published it in Hebrew:
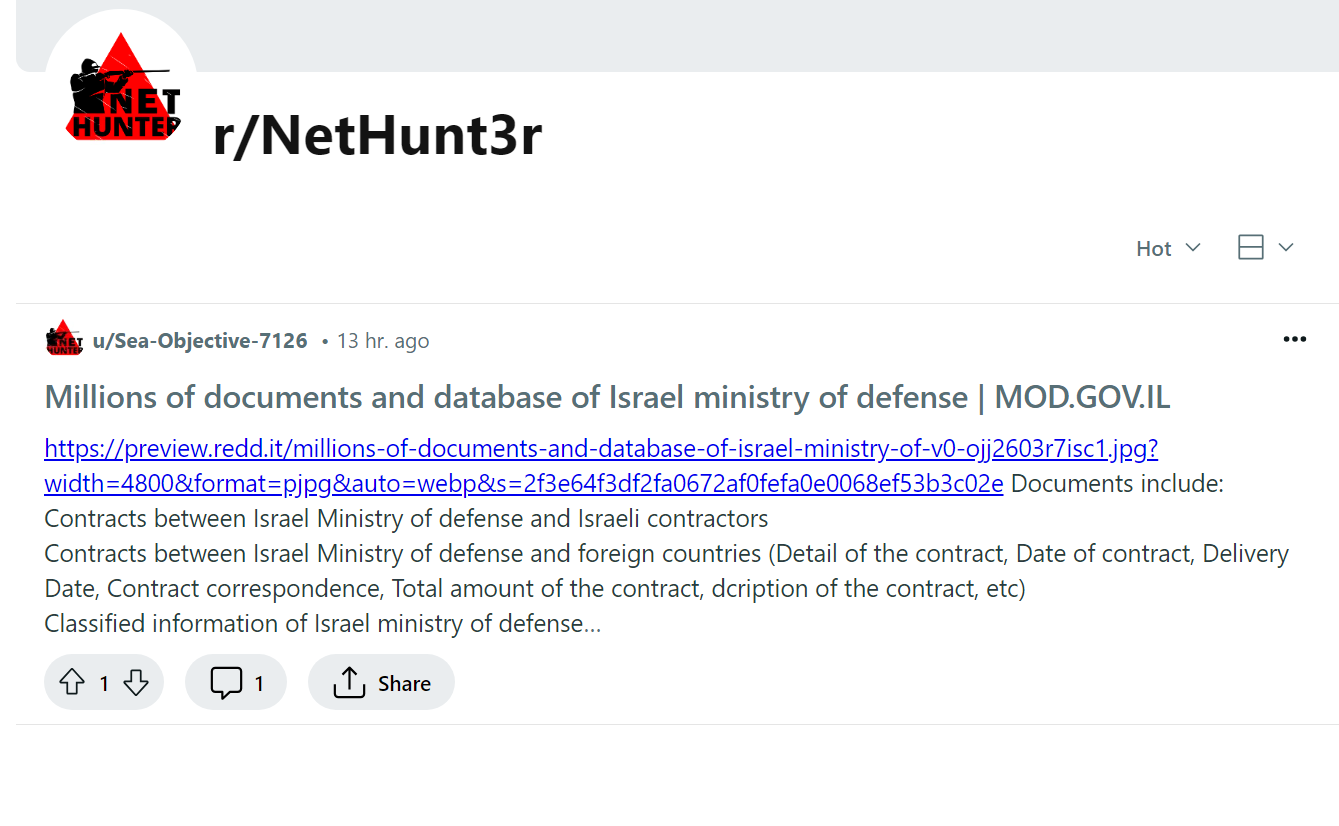
Iranian actors love to amplify breaches of any size, regardless of quality, on social media. In addition to posting Nethunt3r took the time to create a burner account and even a dedicated subreddit for it:
Looking at the actual post, we can see a similarly styled image:
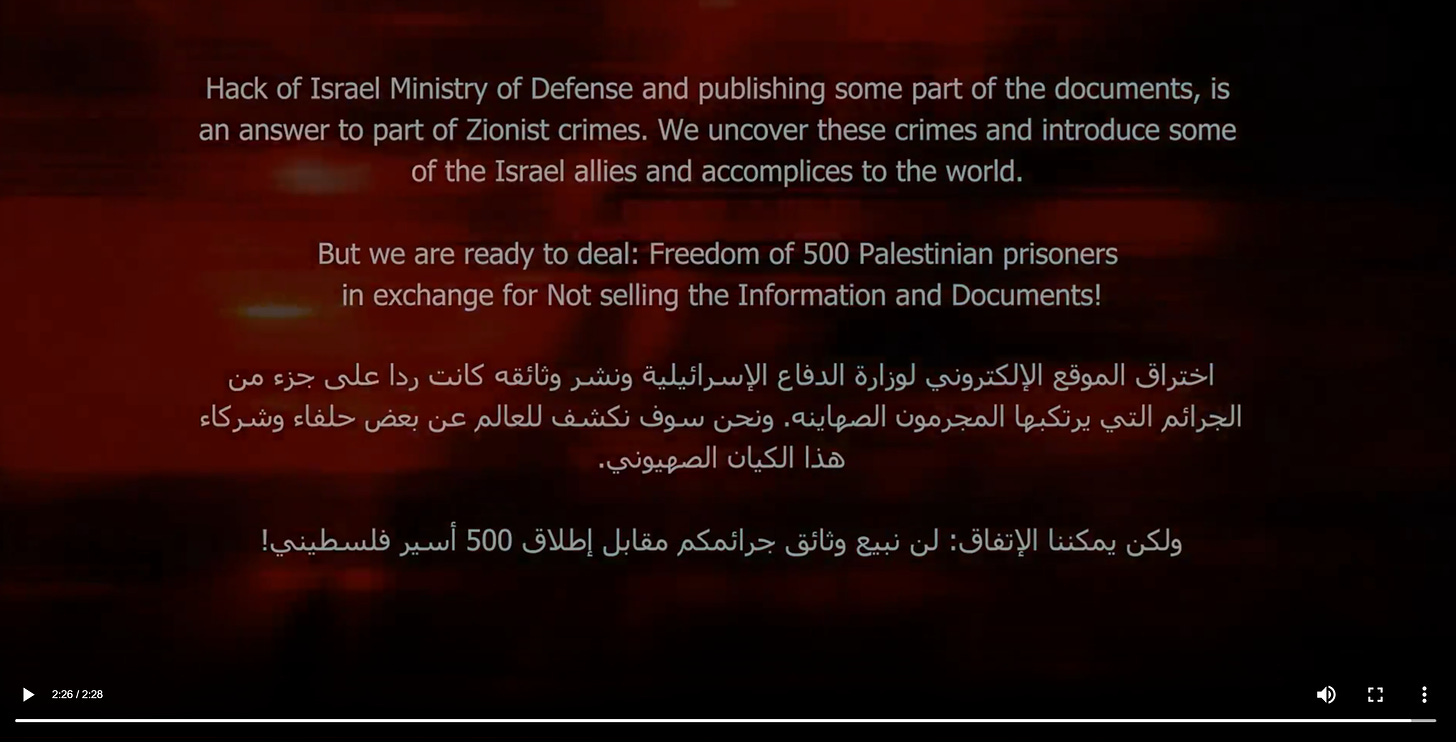
The “POC” link links to a several minute long video on the Cyber Court domain showing their demands, some samples of data and so on:
It should be pretty clear what we’re looking at at this point.
While it’s still far too early for me to make any conclusive statements/attribution, this appears to be an Iranian-run, or perhaps affiliated, cyber-enabled influence operation. I may well be wrong as I’ve only done some introductory research here, but many of the various elements line up for now.
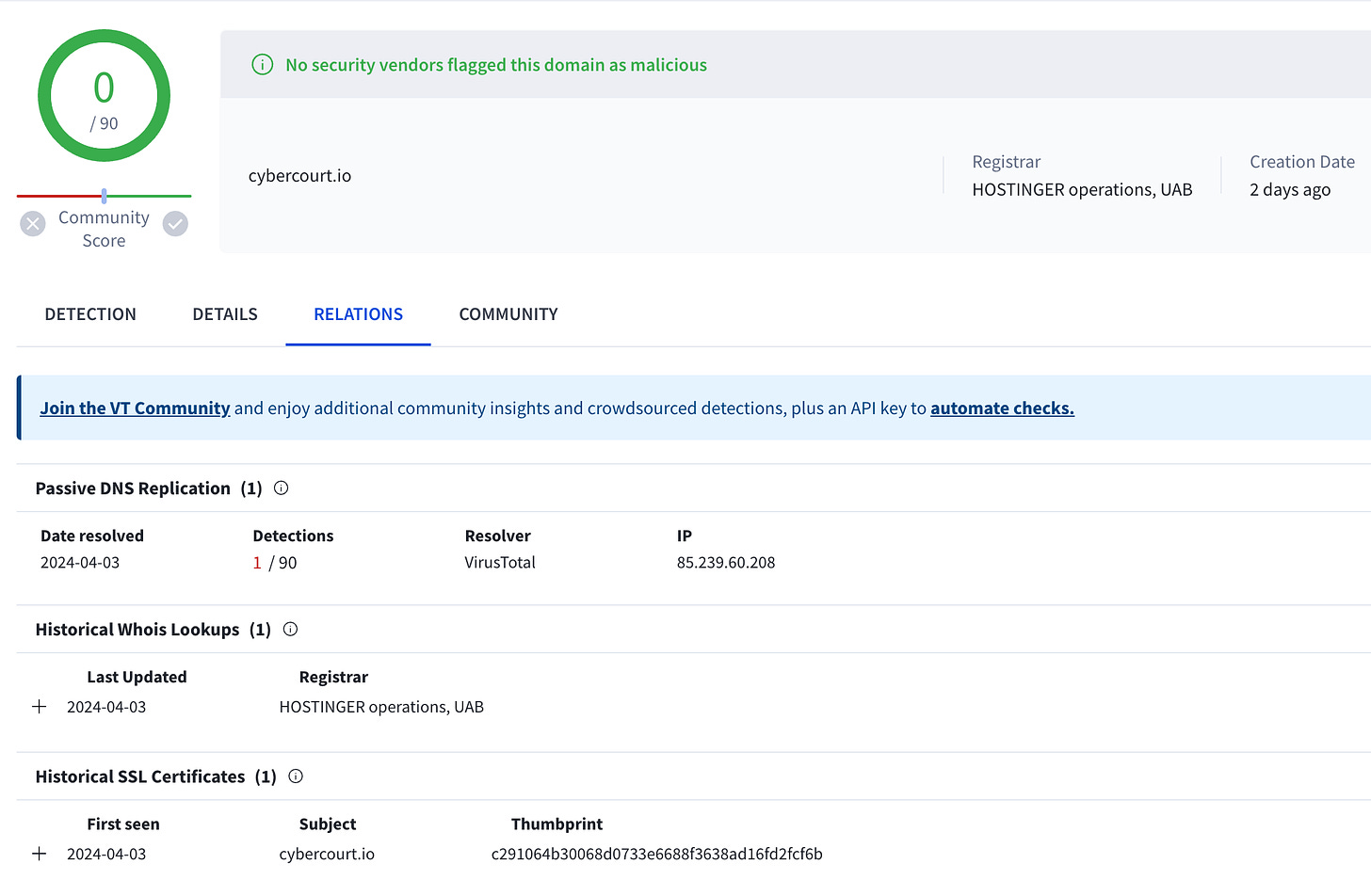
On that note, let’s look at the domain and see what we can find. Let’s kick this off by throwing it into VirusTotal and see what shows up:
So the domain was registered very recently, and has only had one host, SSL cert and of course a proxied WHOIS registration. Nothing shocking there, where would we go from here?
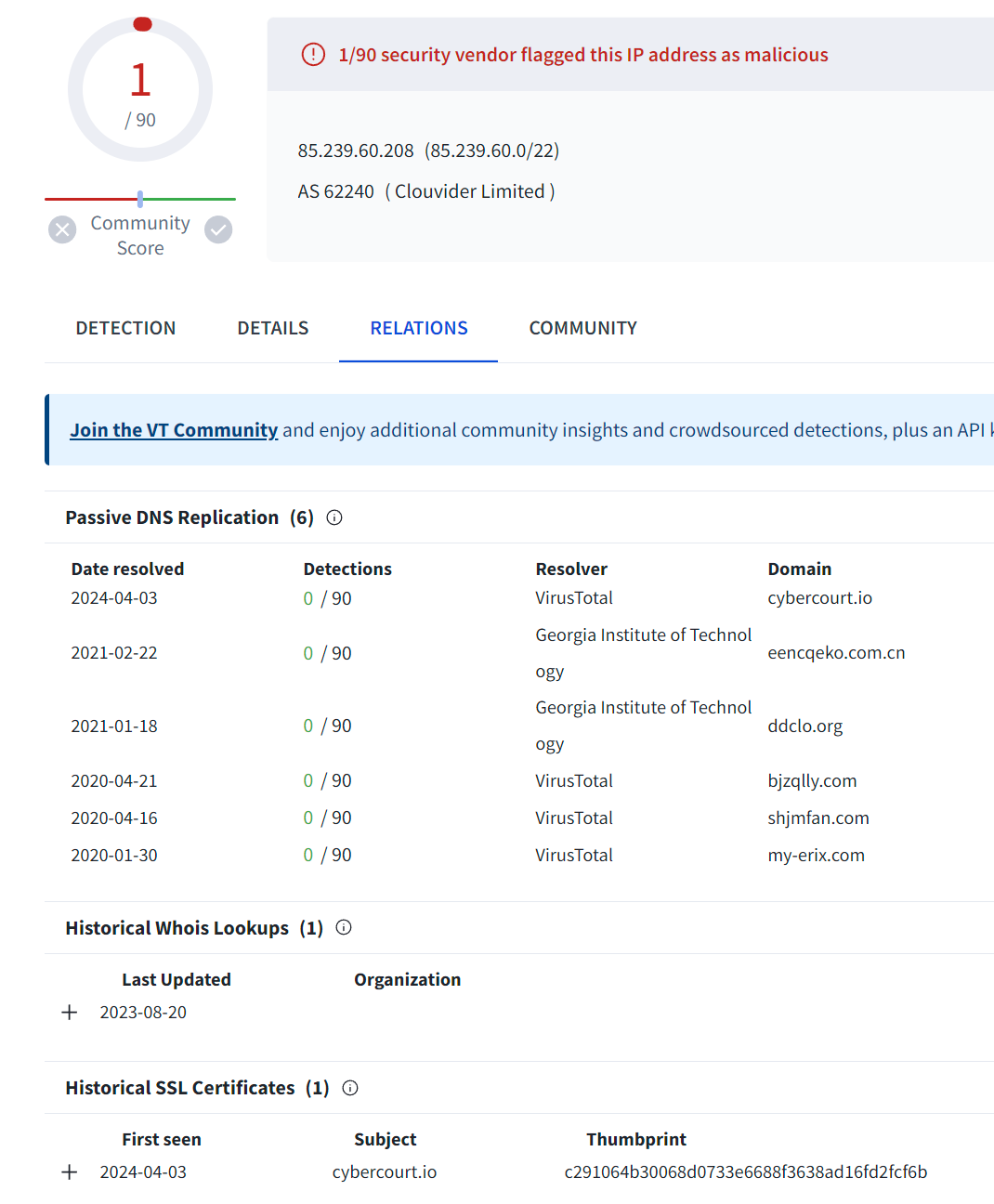
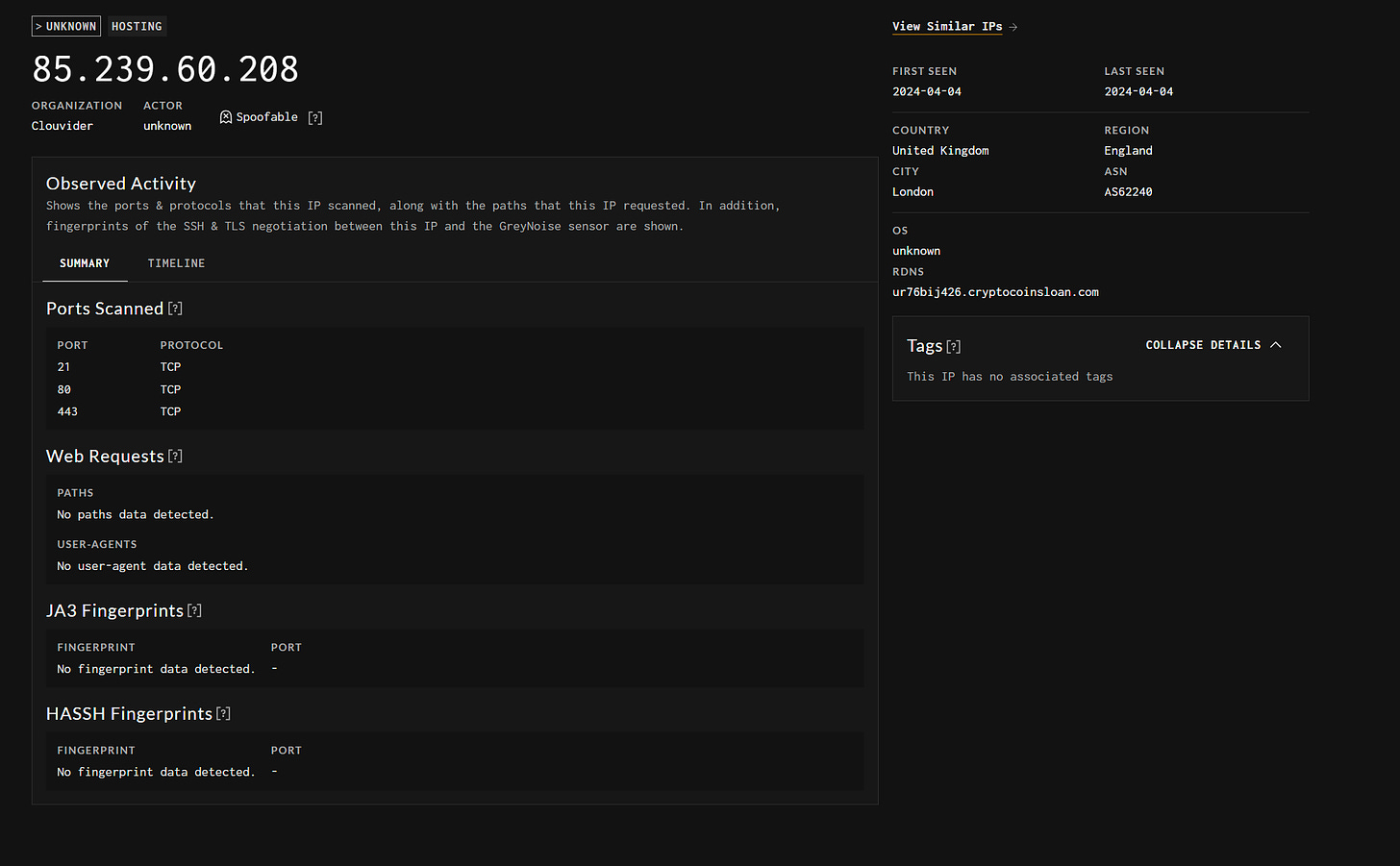
Looking at the host itself, we see that:
It’s been flagged as malicious by one AV provider
The host uses the same TLS(SSL) certificate as the cyber court domain
It hasn’t hosted any other domains since 2021 (one of these is probably the origin of the flagging of the IP as malicious)
In this case, we’re in a bit of trouble as the domains leading up to the most recent registration probably aren’t related to our given domain.
In cases such as these I’d recommend trying to find other relevant hosts or infrastructure tied to the domain to map out its attack surface. Censys is a great tool for that.
In this case, I’ll focus on just infrastructure mapping via technical means and not qualitative methods - i.e. content and so on.
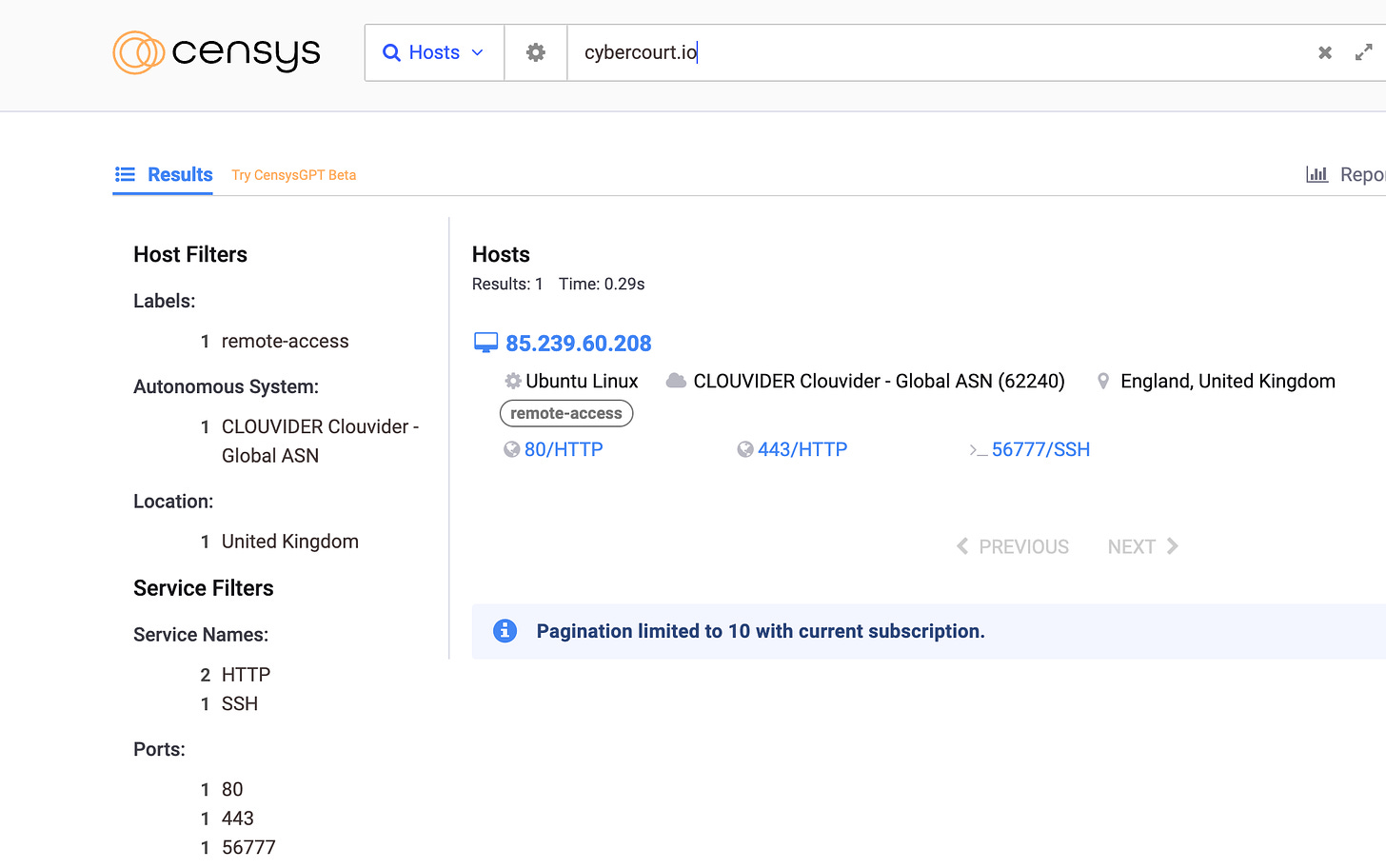
Querying the domain on Censys only gets one host as well:
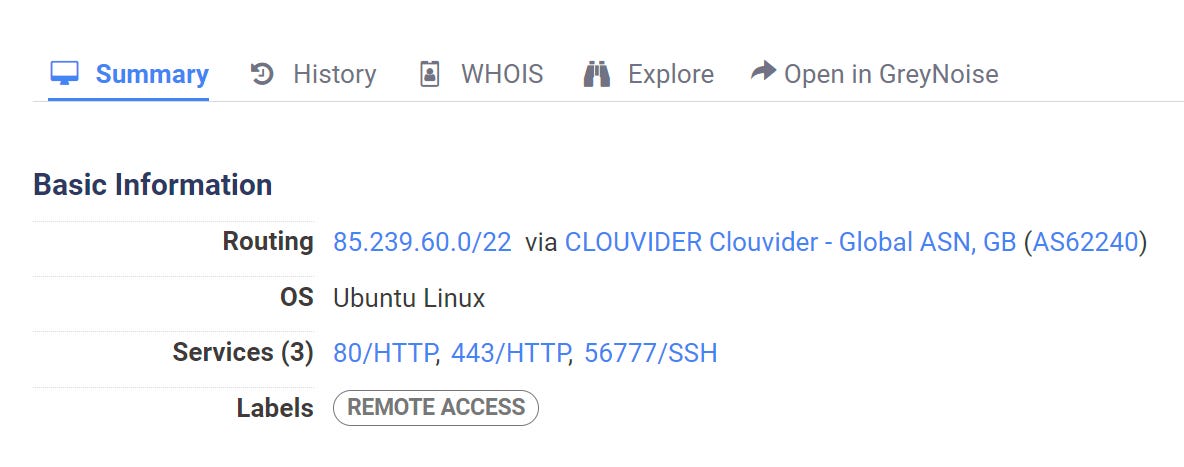
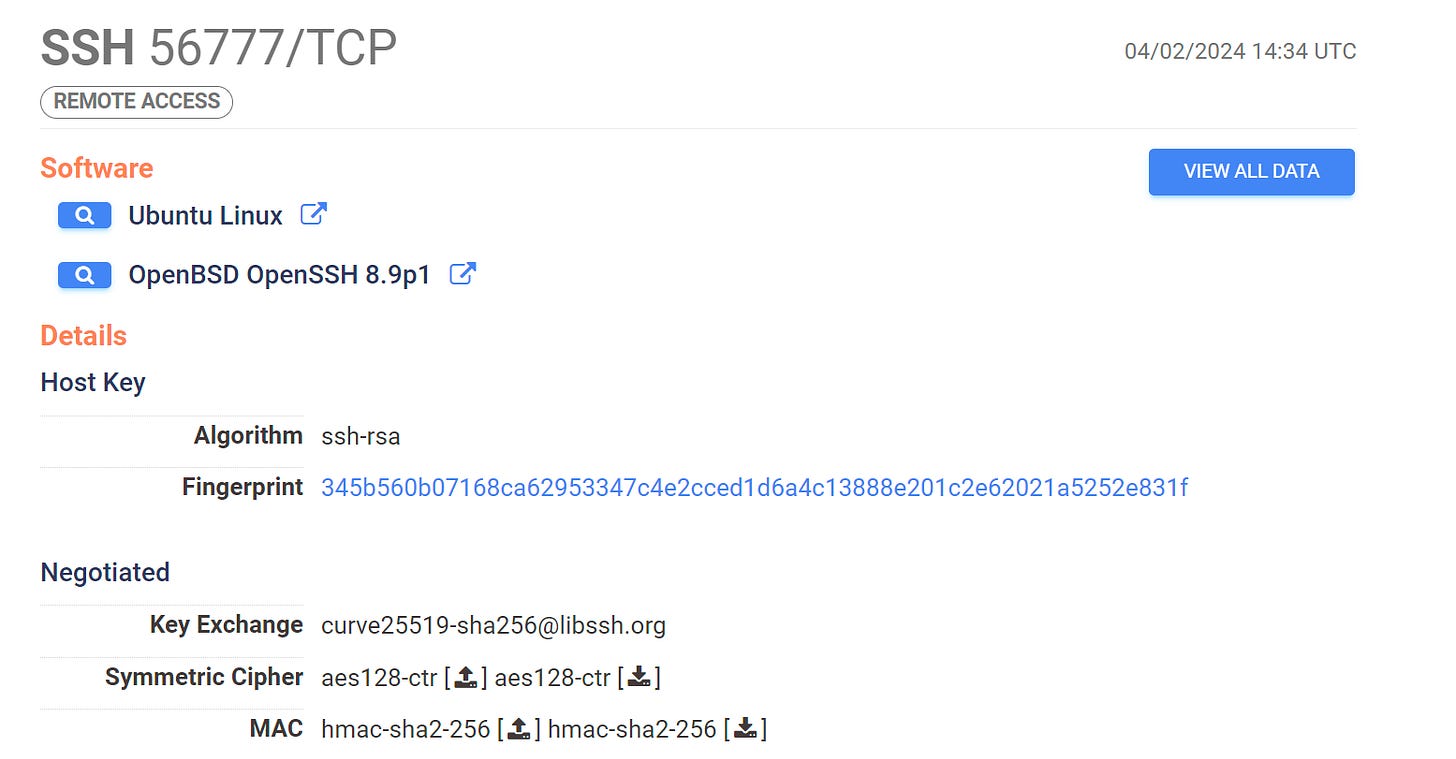
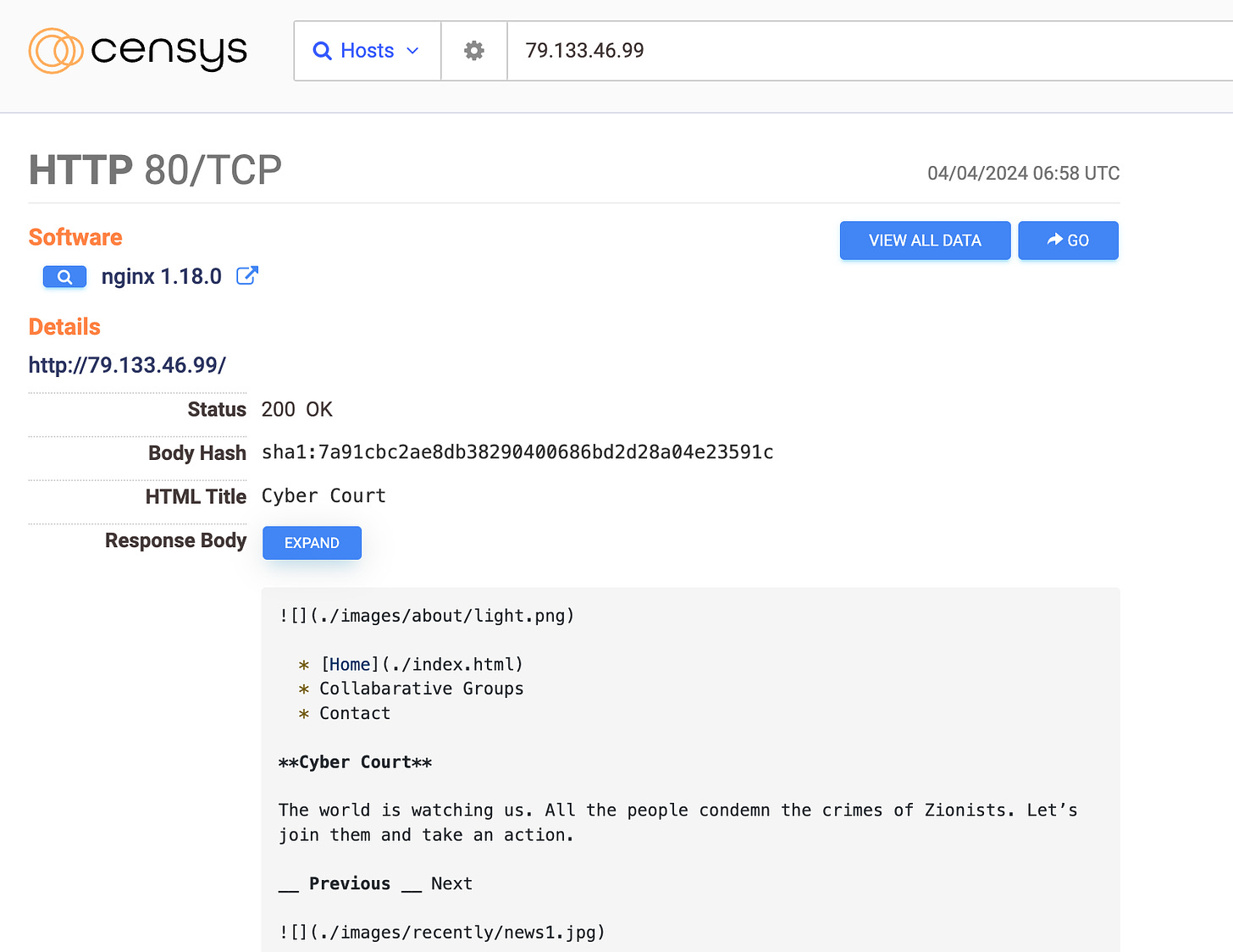
So let’s take a look at this host. Hosting provider aside, there are only 3 running services on 3 ports - 80 and 443 for HTTP, and 56777 for SSH.
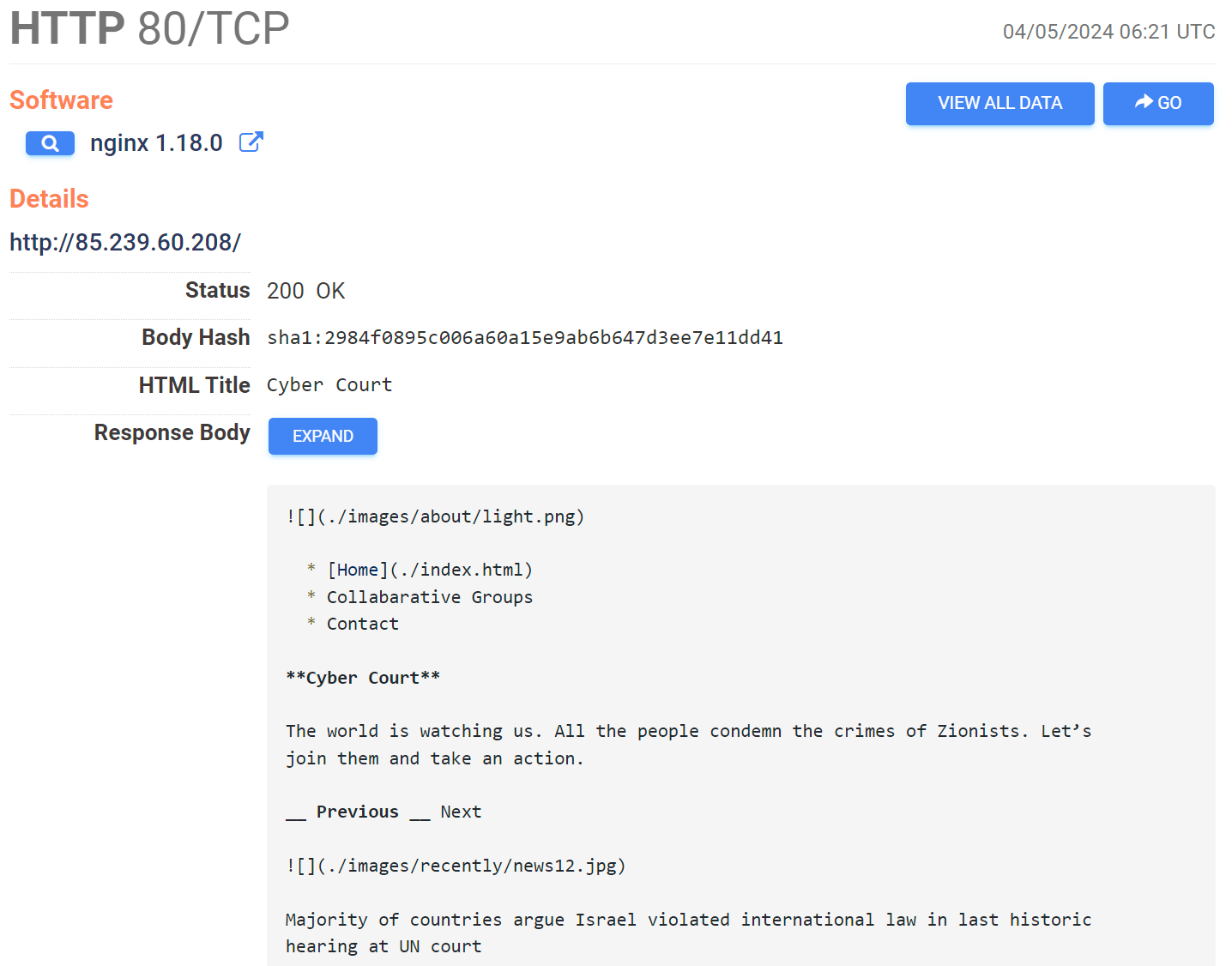
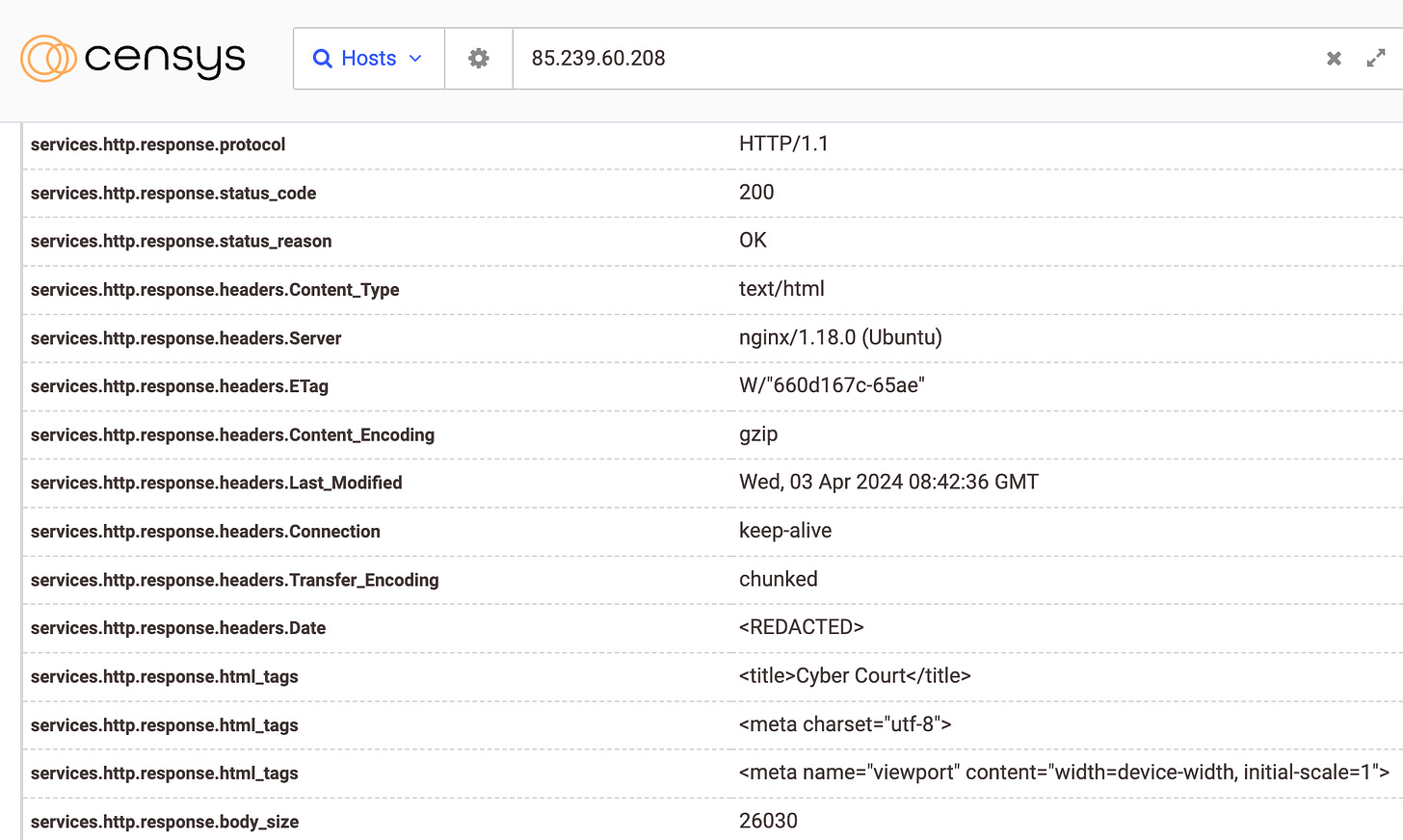
That gives us a bit less to work with but shows that it’s a pretty standard Nginx web server. In this case, we could look at the HTTP responses:
So that HTTP response body matches up. We now ideally would find other hosts that share similar fingerprints or characteristics.
As an aside - the SSH key is unique if it’s left public, so we could pivot off of its fingerprint, but in this case it’s used just for this server.
Due to the paucity of information available on this specific host, we may need to get creative. In these cases, I like to look for e-tags, which we can pull from HTTP responses from the domain in Censys, just click on one of the buttons where it says “view all data” for a given service HTTP response.
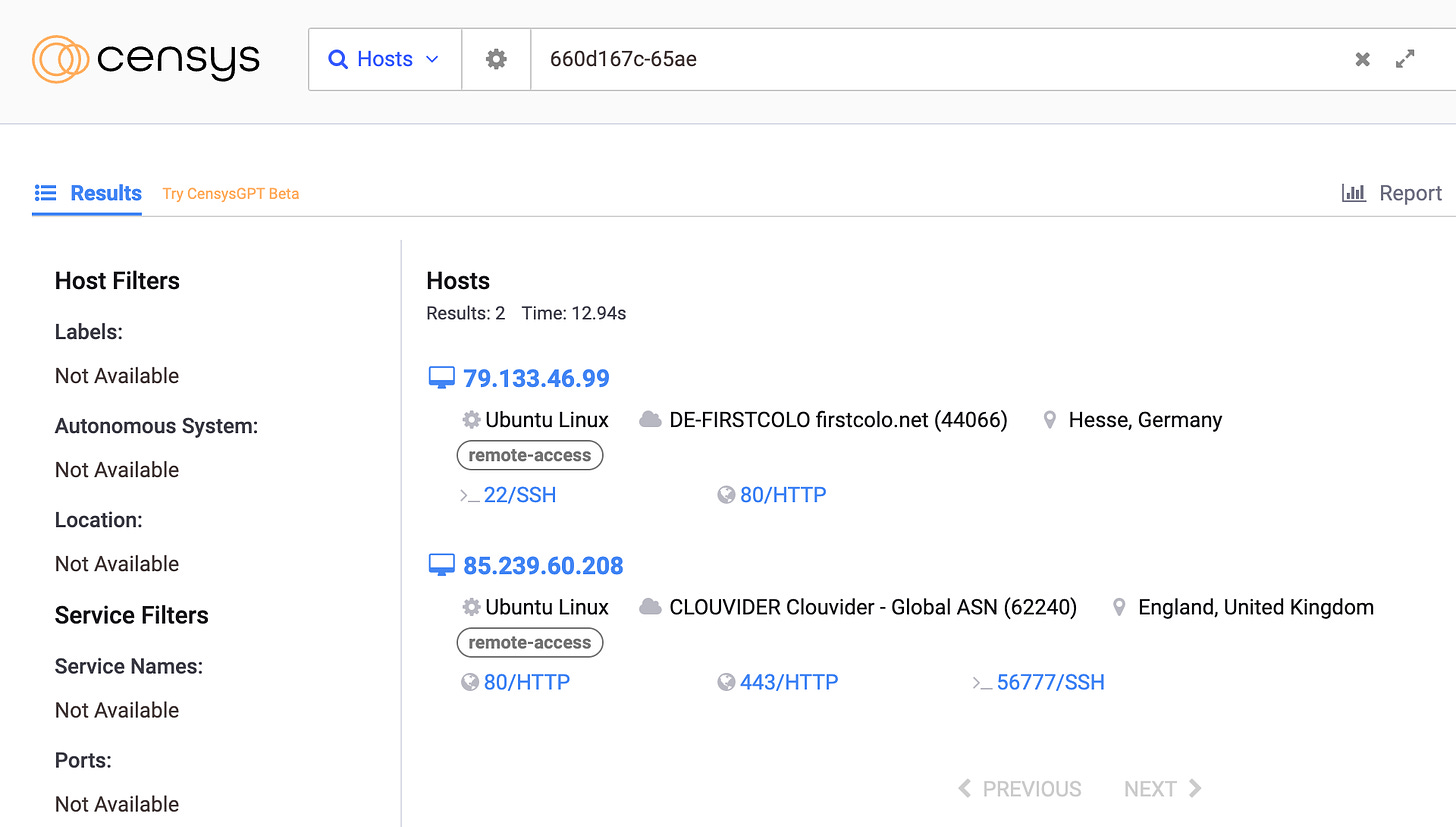
There we go, we see a specific e-tag. Querying it in Censys retrieves another host that didn’t show up earlier! For those curious, there are other ways to find this host as well, including arguably easier ways, but I’ll let you figure those out.
E-tags are great but we have to double check them whenever we find a successful pivot point, as they can change and be unreliable.
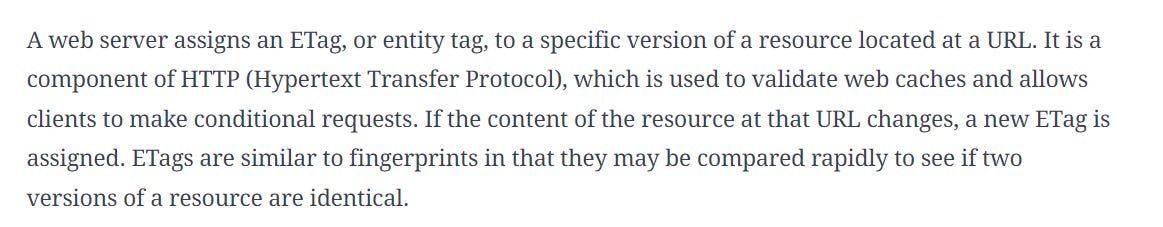
E-tags can change if the HTTP resource itself changes, read more here - they’re an interesting part of HTTP:
In this case, looking at the domain shows that it is in fact hosting Cyber Court content available via the HTTP service on port 80:
Overall, we’re in good shape here - we already have another affiliated host.
That in of itself is great! We have another host, and can pivot from there to expand our investigation, or report it to LE or to the provider.
What are some other things we could do?
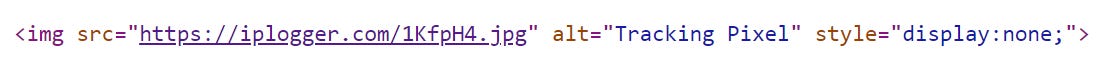
There’s a tracking pixel embedded in a JPG image in the source code - could be worth reporting to the provider.
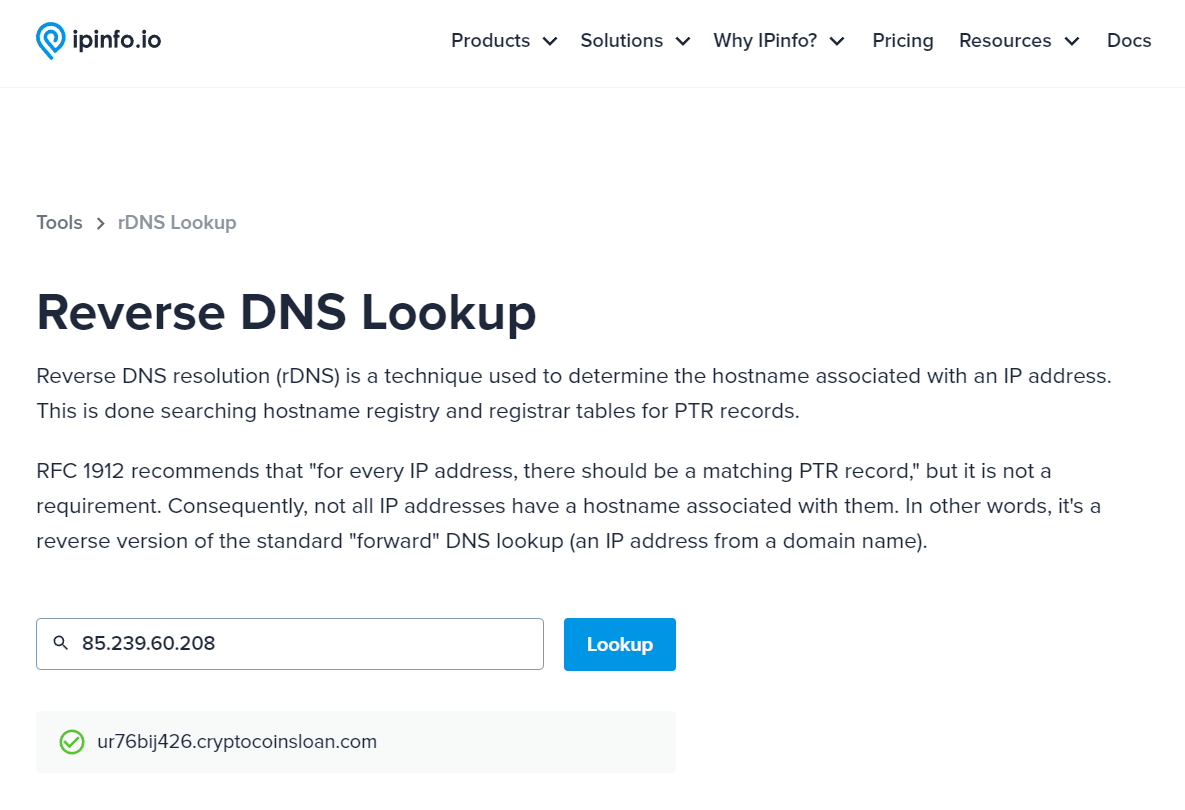
We could also use other tools. URLScan was a bit underwhelming in this case, so I utilized the Greynoise pivot built in to Censys. Here we see that Censys has the host resolving via a reverse DNS lookup to a suspicious subdomain of some crypto loans site.
We can confirm that via IP Info:
Chances are that this was an old registration of some odd subdomain used for whatever purpose, but still something fun to look at. Were I to speculate wildly, I could presume that that subdomain could have been used by threat actors as part of a phishing operation. One of the harder things about this field is knowing when to pivot and when not to accept a given result as accurate, and I’m definitely not fully sold on this one.
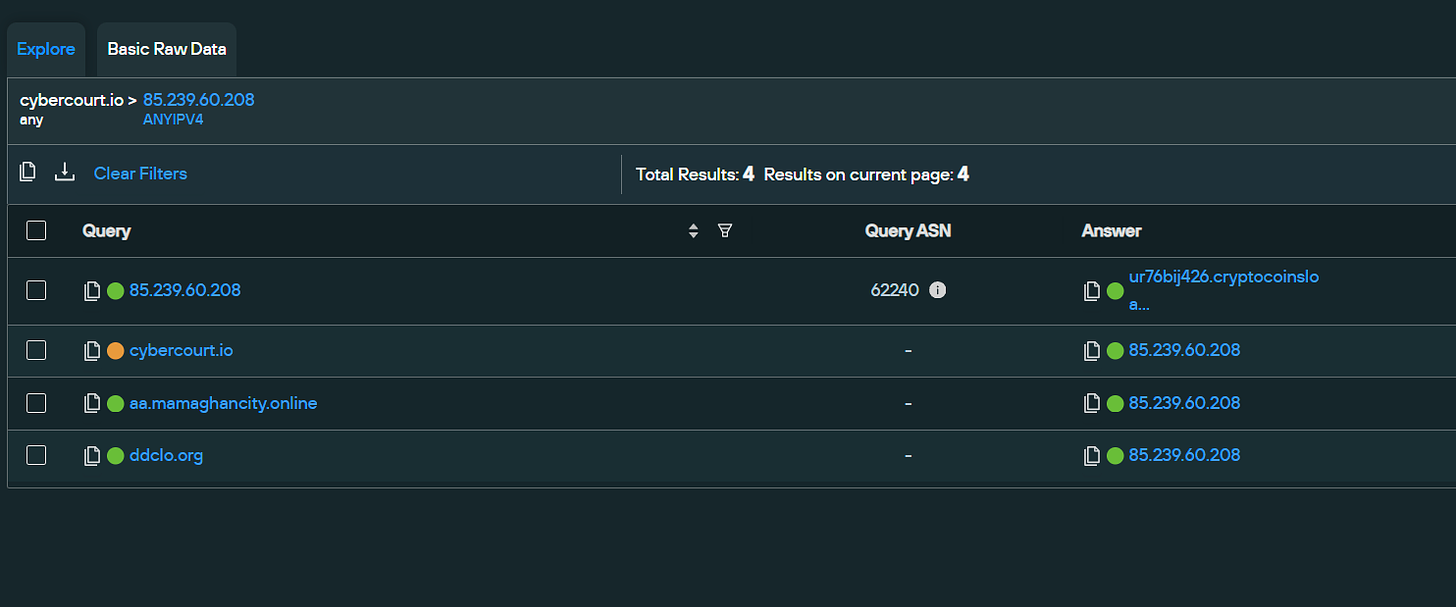
Let’s take a look at passive/reverse DNS in other providers, like Silentpush:
Here we see that we have two new domains that have resolved to it in the past - one in 2023 (the mamaghancity one) and one in 2021. Mamaghan is a city in Iran, so that’s a nice piece of evidence in of itself, but is far from being conclusive. The DDCLO org domain is down also, but previously has hosted a gambling/porn site, and before that a data analytics organization in China, as per archive.org.
All things considered, it’s definitely a bit odd to have recently hosted a local Iranian domain alongside so few other domains historically! If anyone has a Zetalytics or other premium DNS tool to query for this, I would be eternally grateful if you could check it and send me the results.
Let’s recap and call it a day. We started off with the suspicious domain, and investigated it for context to make some early calls.
We then investigated its infrastructure, found a new host that wasn’t easy to otherwise tie to it, and have now come across some domains that were previously registered on the host and may be indicative of ownership or activity.
We have plenty of data and pivot points to investigate, as well as of course keeping an eye on the domain of origin and affiliated entities.
That’s it for this week - next week we’ll take a look at Microsoft’s latest threat report on Chinese activity!
I’ll reiterate as well - have any questions or feedback about this post? Feel free to let me know via LinkedIn or ari@telemetryapp.io!