Memetic Warfare Weekly: MY DATA LEAKS ON GITHUB Edition
This is a rare mid-week post but the recent news is worth it.
Readers of the blog may have come across news of a recent data leak of a Chinese APT contractor named iSoon (Anxun). iSoon works primarily for the MPS and had a massive amount of their internal data posted to Github the other day.
I came across this information thanks to Bushido Token on tweeting about it here.
Will accurately compared it to the Vulkan leaks but arguably better in that the data itself is publicly available on Github.
Twitter user DE7AULTsec also posted a machine-translated version of the documents here for the curious. The best overall coverage though is from AzakaSekai on Twitter, who has provided a lot of insight, as well as translation, of various elements of the leak.
I need some more time myself to dive into the various IO-related sections of the leak, such as a Twitter monitoring system and botnet control platform:
Tons, and I truly mean tons, of fascinating datapoints are available. Be it internal chatlogs of employees, payroll stubs for the average employee (less than 1,000 USD monthly for most), information on specific malware, VPS deployment and management systems, CDRs of victims and other proprietary information - it’s all here.
Sentinel One’s Dakota Cary and Aleksandar Milenkoski have also published a short report on their findings as well here. Dakota has also tweeted more in-depth about specific findings here.
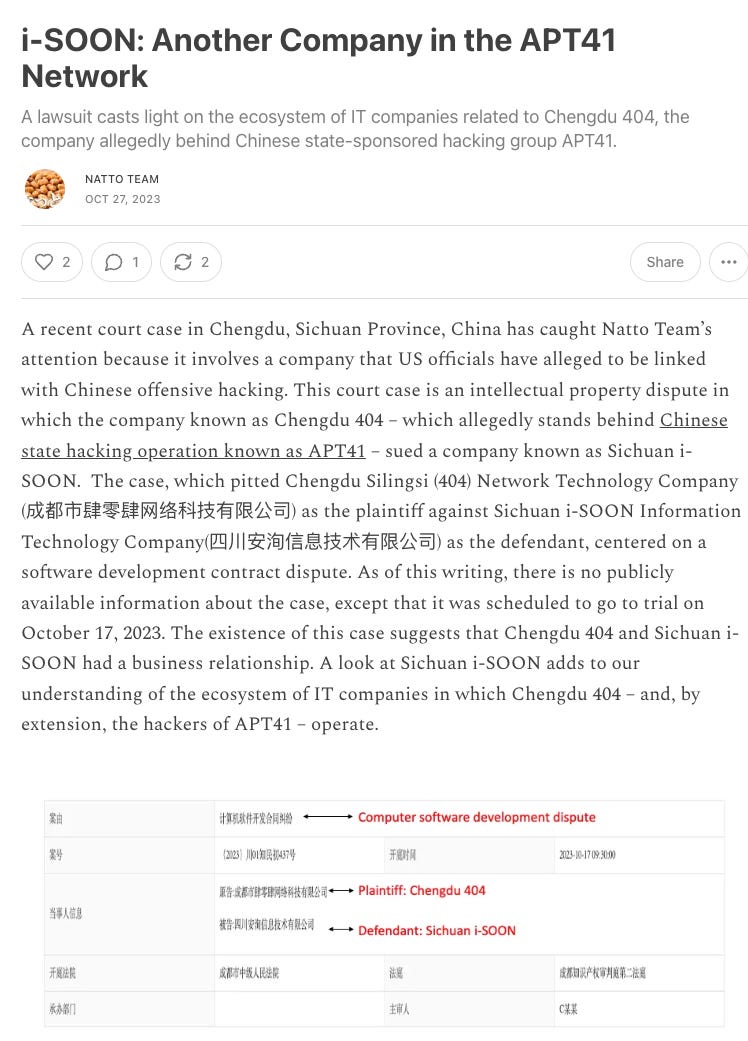
Those interested in reading more about this specific company, its activity and its connections to Chinese APT groups you can check out past MWW posts as well as the highly-recommended Natto Thoughts:
I’ll leave it to those better-equipped than me to go through the content itself in its detail, and will instead focus on something else that I like to do when these reports come out: pivot on the findings to find more information, map out additional potentially hostile infrastructure, and do our best to attribute as much as we can to specific actors just for fun.
Side note: one of the upsides of working in my space is that I get to work with interesting companies and products in the OSINT space, and to that effect, we’ll be using one of my partner tools - Falkor.ai.
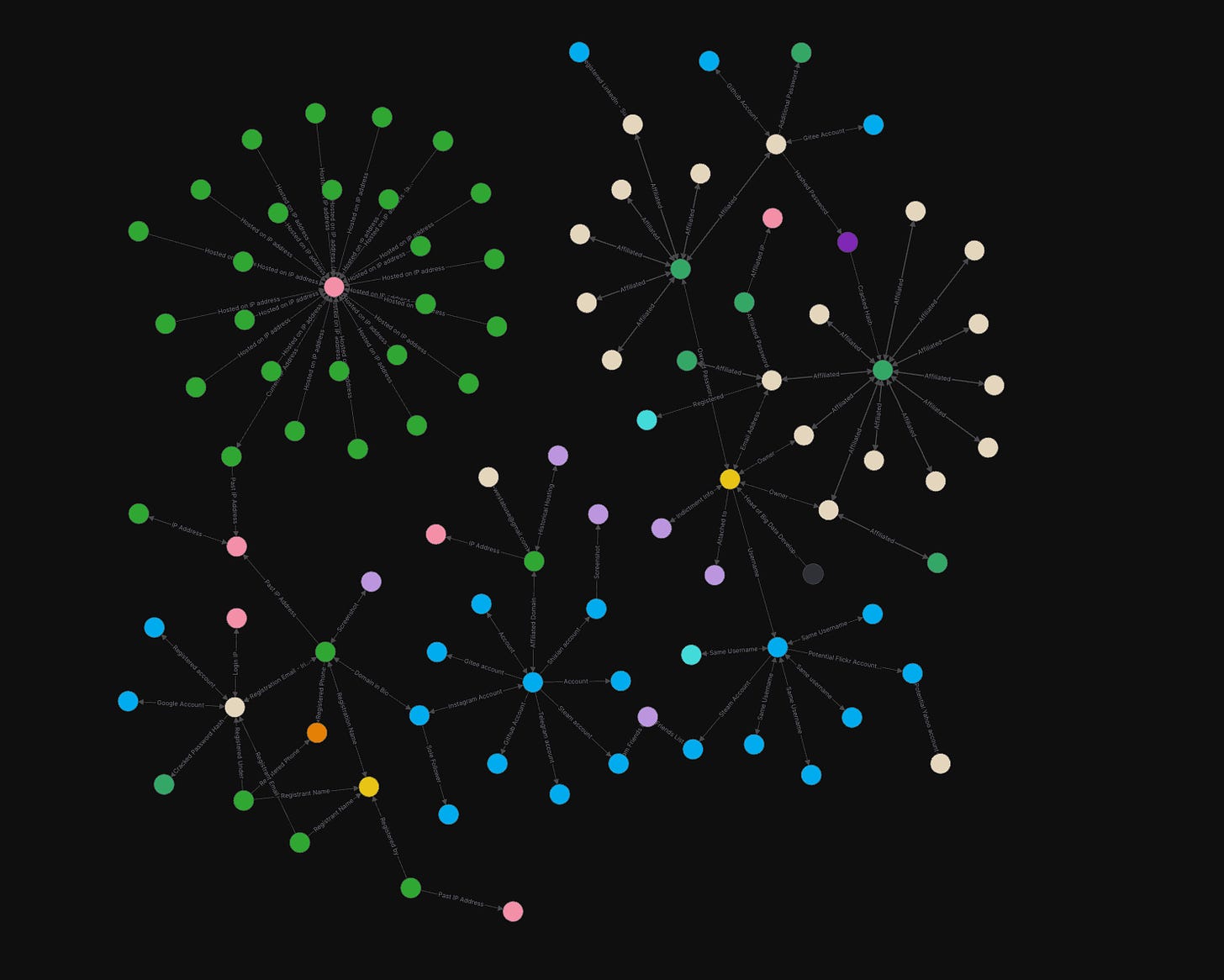
I’ve had some fun chances to use Falkor in the past, for example see a zoomed-out and very, very basic mapping out an APT 41 operator’s online presence, including newly identified email addresses and other IoCs:
Falkor is an investigations platform with a lot of fun features, and those will help us gain a better understanding of what’s going on here.
On that note, let’s begin.
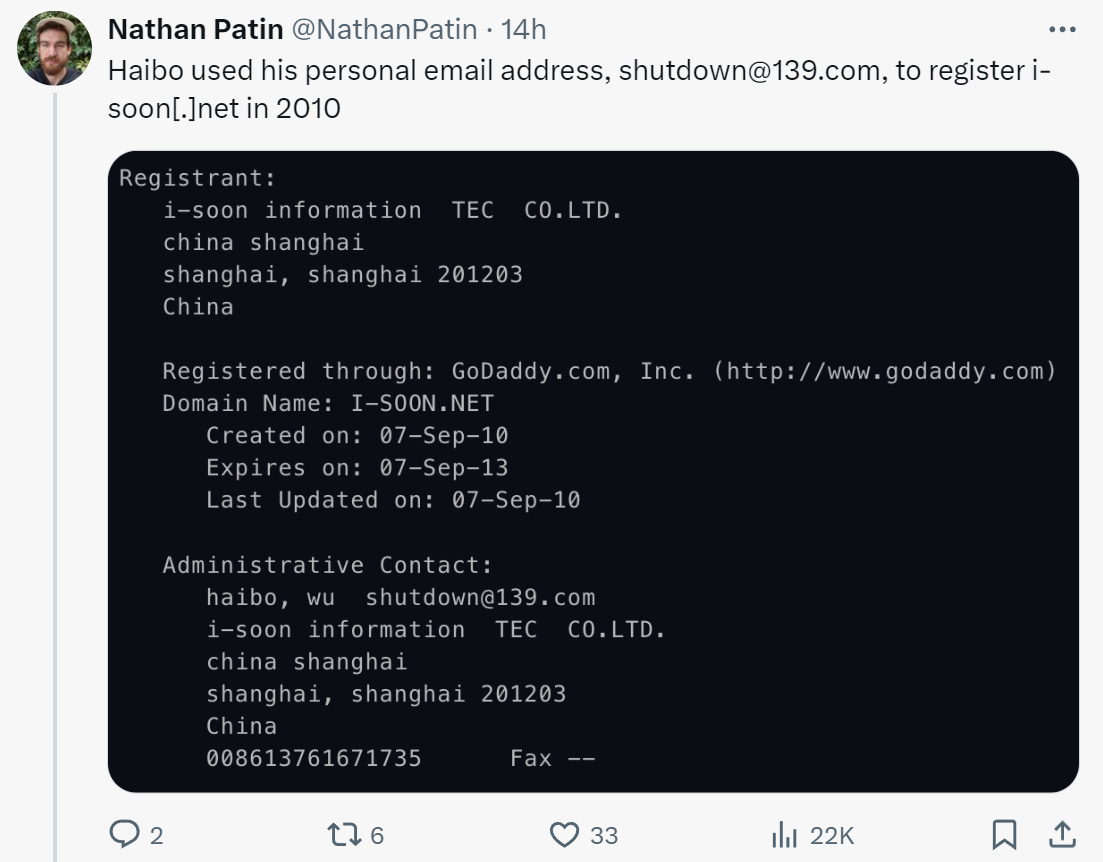
Chinese APT contractors are not known for their rigorous OpSec, and thus the front domains they use themselves are often valuable pivot points in of themselves. i-Soon itself was founded by one Wu Haibo, and key figures are also in of themselves excellent pivot points.
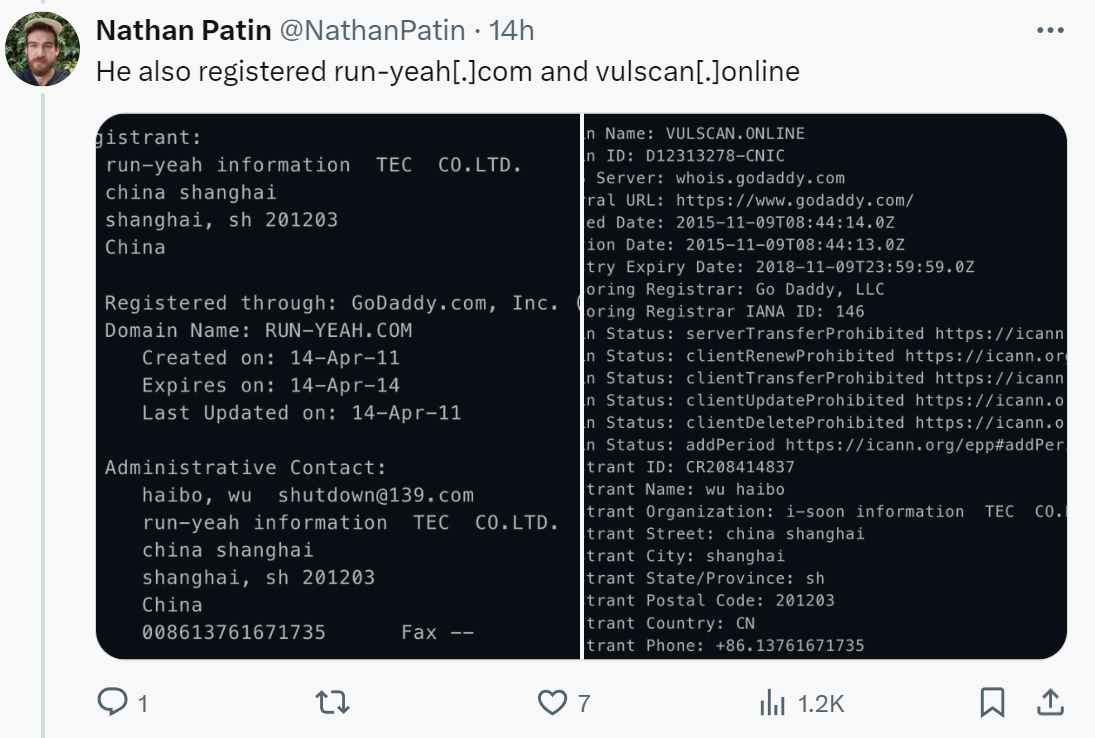
Other analysts and researchers, such as Nathan Patin and others, have begin looking at Wu Haibo and others:
The various OpSec breaches themselves are long and interesting, view Patin’s thread in its entirety here for more.
Some standouts include additional domain registrations under the same email address:
Twitter user Soufiane also took the chance to dunk on Wu’s poor OpSec:
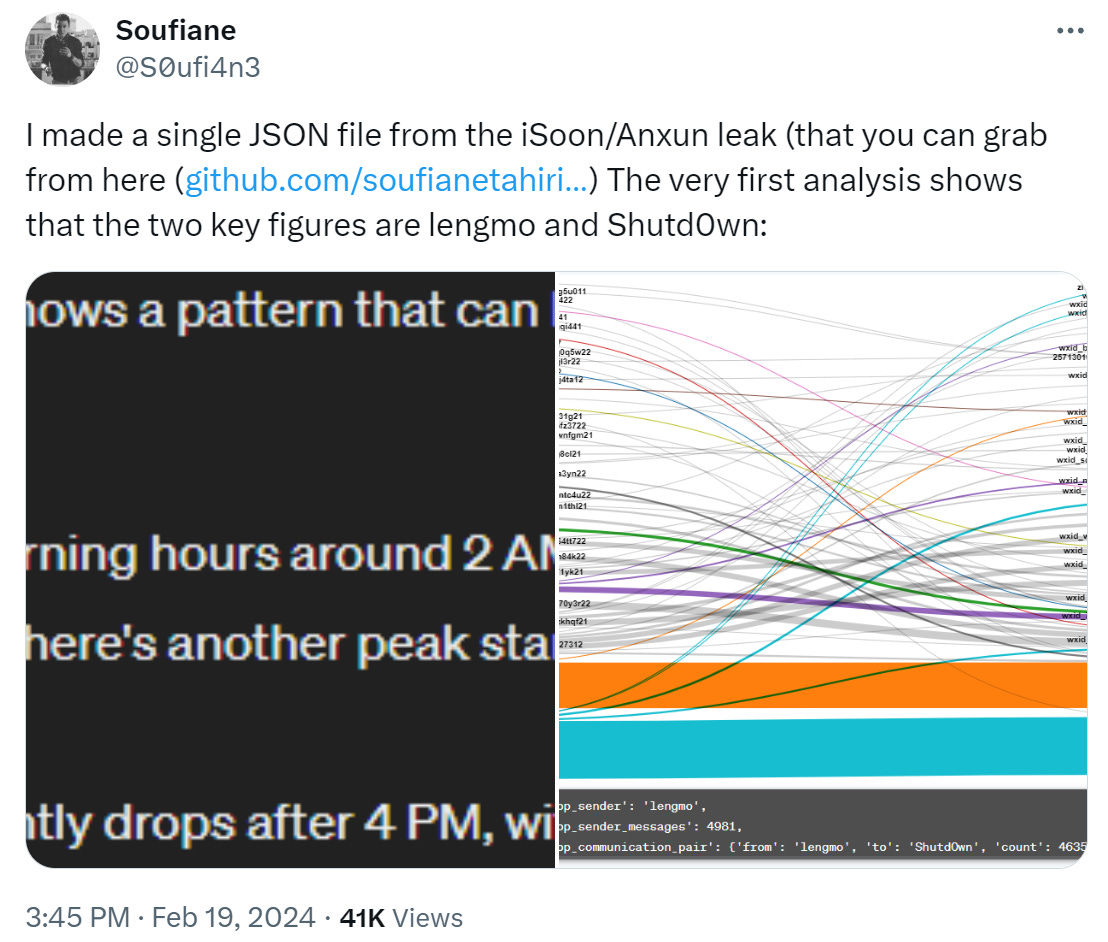
Soufiane took the time to create a JSON file of the leak to show the relations between the key figures, and found that Wu (using his moniker Shutd0wn) and one user named Lengmo are the two most central and active users in the leaked chatlogs:
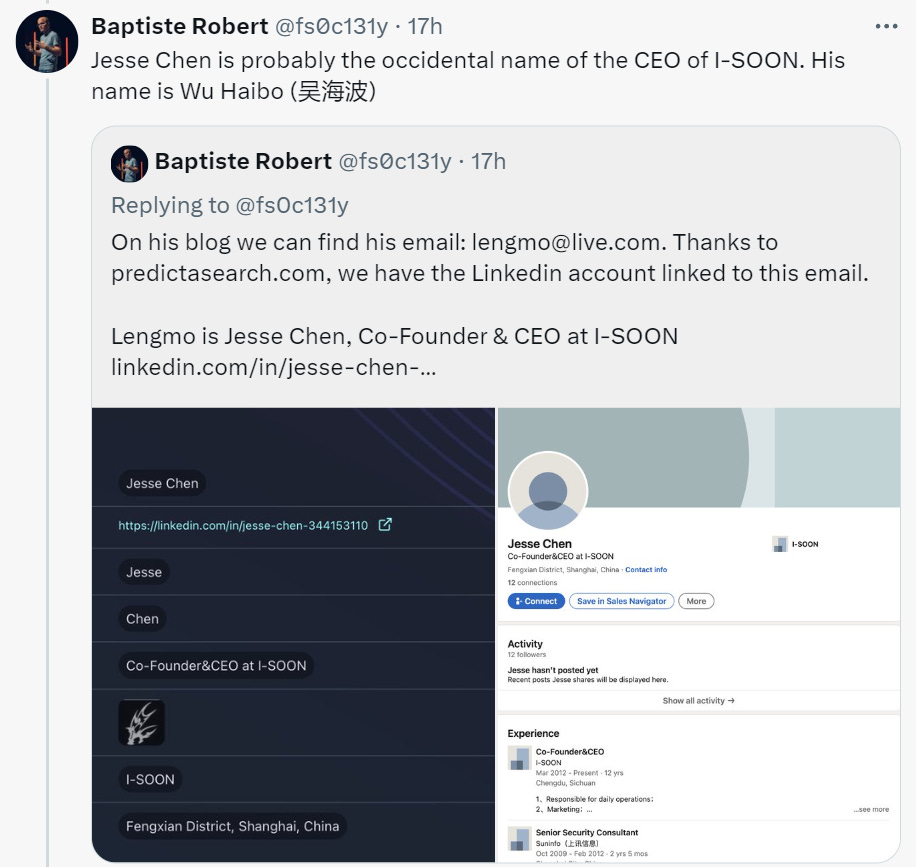
Baptiste Robert, the founder of Predica Labs, also took the time to look at the “lengmo” user, with his findings available here. With some investigation and the use of his own tool, he was able to show that lengmo is probably the taken Western name of Wu Haibo and that lengmo may be another username affiliated with Wu.
Insomuch as everyone is busy looking at Wu and other central figures, I figured that I’d take a different look at the more recent activity and perhaps some of the lower-profile members of the company.
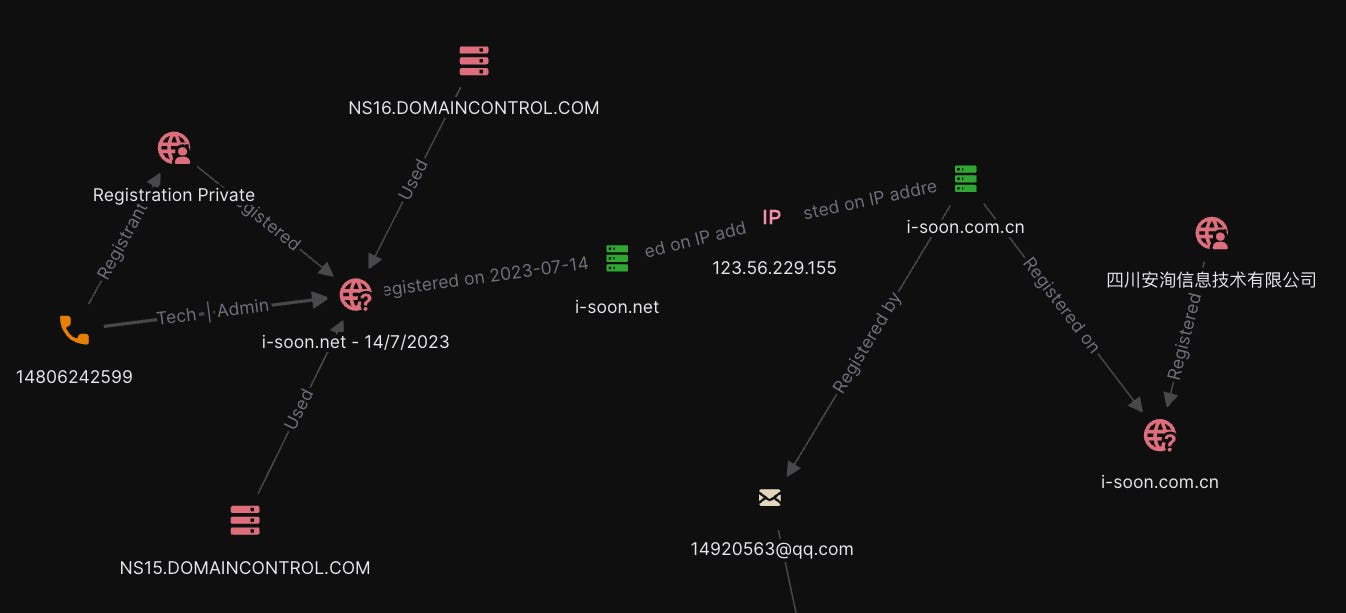
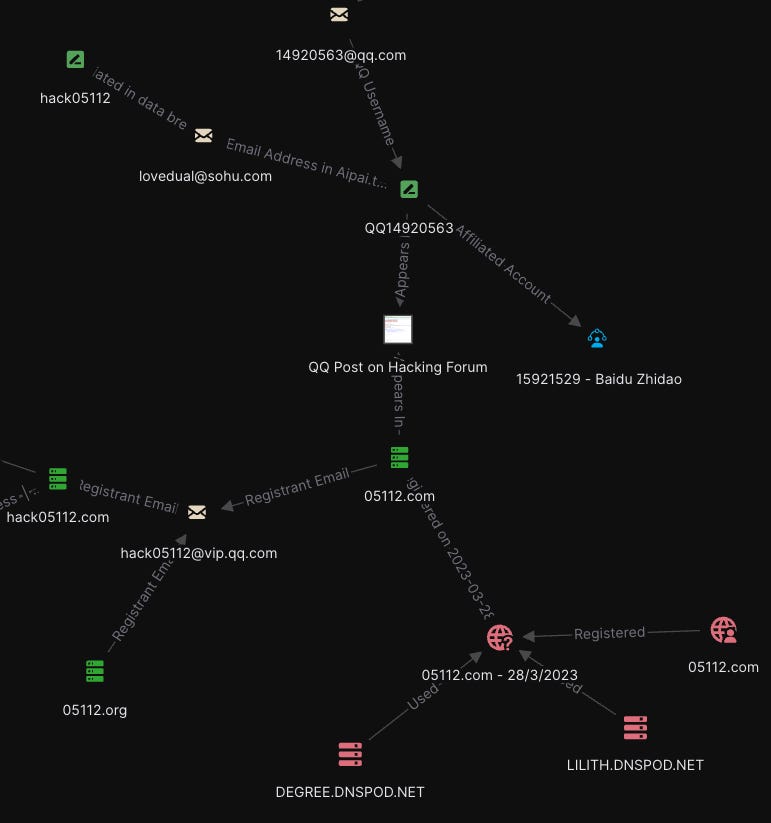
To do that, I started off with a basic DomainTools WHOIS query for the domain to retrieve the most recent domain WHOIS registration and IP address, as the historical records have already been covered. Querying the IP address with a reverse IP lookup retrieves the same domain name at a .com.cn TLD, which in of itself was registered by the company itself as we can see on the right-hand side. Interestingly, this domain’s last WHOIS registration includes a QQ email address as its registrant:
That QQ address is pivotable in various ways; looking it up in email lookup tools such as Epieos, OSINT.Industries, Castrick Clues, breached data tools such as District 4, search.0t.rocks, Dehashed and others, to name a few. However, in the case of many QQ email addresses, it won’t be used as frequently as “regular” email addresses to register accounts.
That’s not all we can do with it though. QQ email addresses are constructed of the User ID of the QQ account, meaning that the numerical string before qq.com is in fact the username. We can then query that as well in any search engine of your choice:
So far pretty par for the course for what we’d expect from a potential APT contractor (and an underpaid one at that) - active on ITPUB, a Chinese forum, other sites and even a Baidu Zhidao (akin to Quora let’s say but for Baidu, another similar platform in China would be Zhihu).
Let’s look at some of these results, including one brought up by querying the email address as a full string:
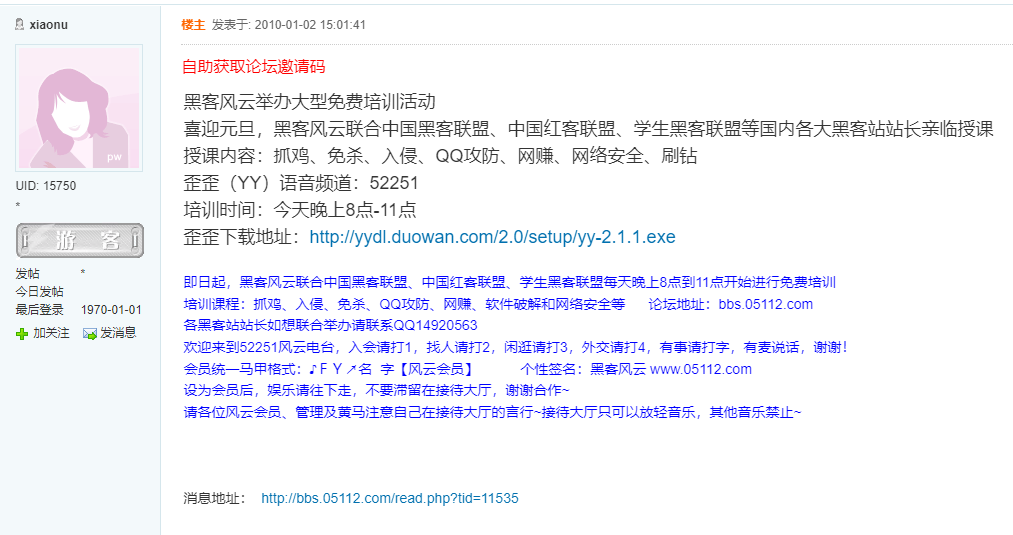
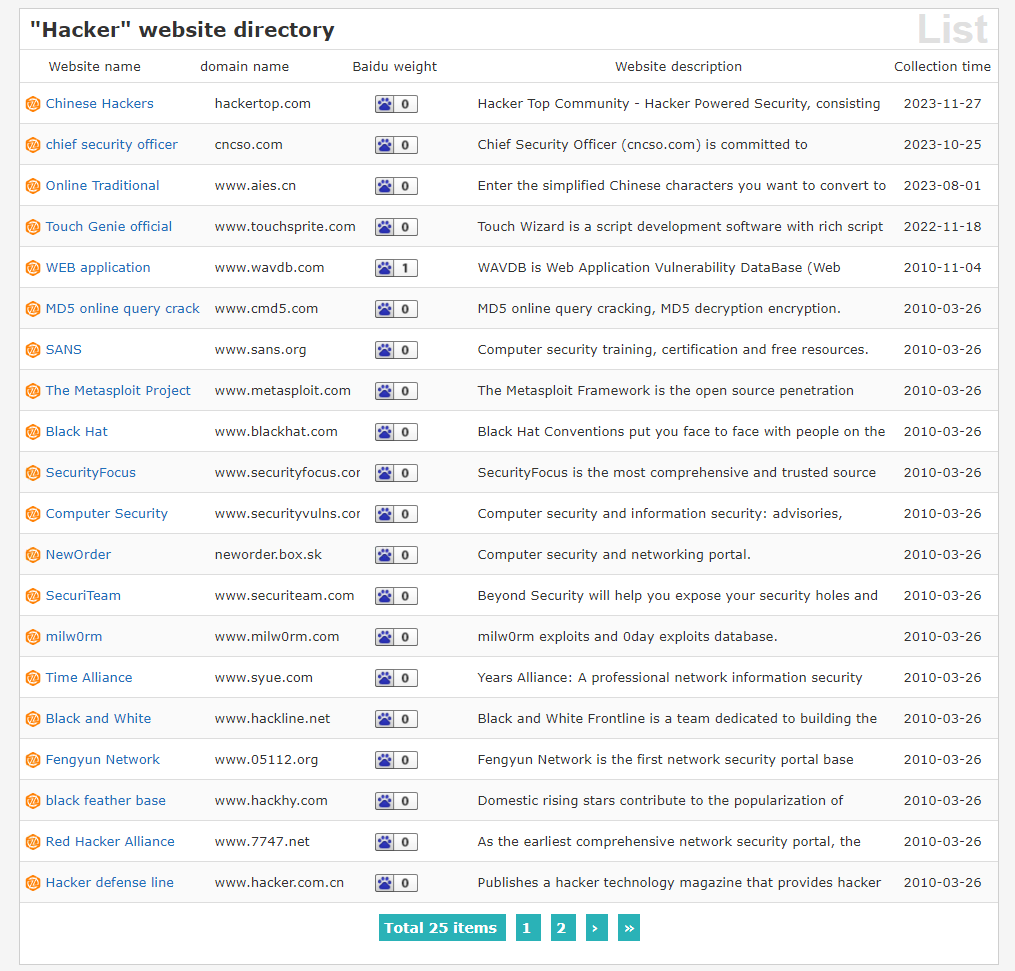
This one looks interesting, let’s look at the post itself. Ah, it’s a free training hacking event held by various Chinese security and IT organizations, and hosted by the Fengyun hacking organization.
This time, in English:
This provides us with evidence of the QQ handle being used in the past for hacking-related activity, in this case back in 2010.
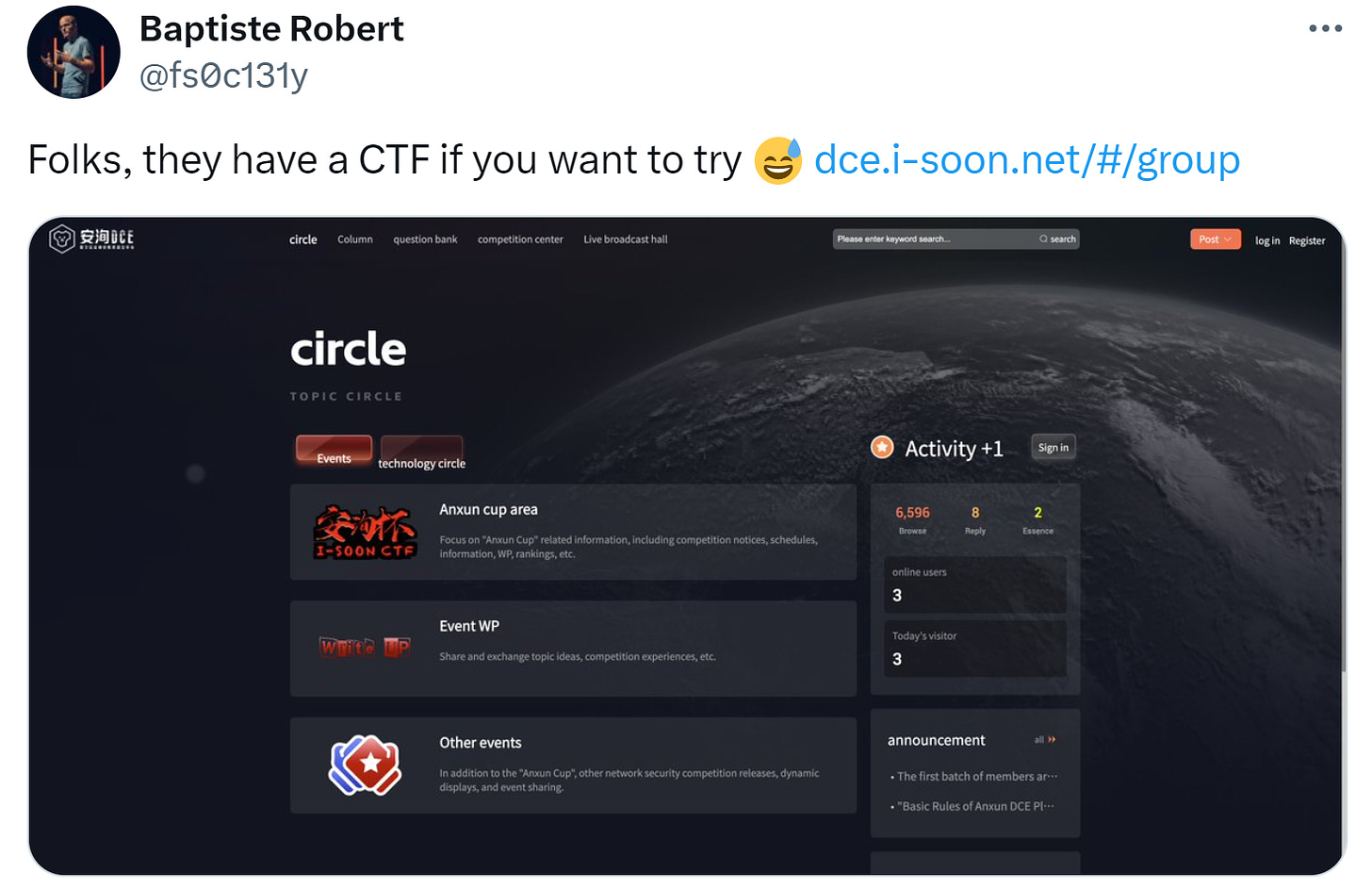
Baptiste Robert has also shown that Anxun/i-Soon runs CTFs and other hacking competitions on its main site in a similar vein:
This dynamic is actually pretty common, be it in China, Iran or Russia - young people with an proclivity for hacking have online presences in relevant forums, competitions and more and are then snapped up by contracting firms.
So not only do we have some interesting context there, but we can then look at the specific site referred to as well: 05112(.)com.
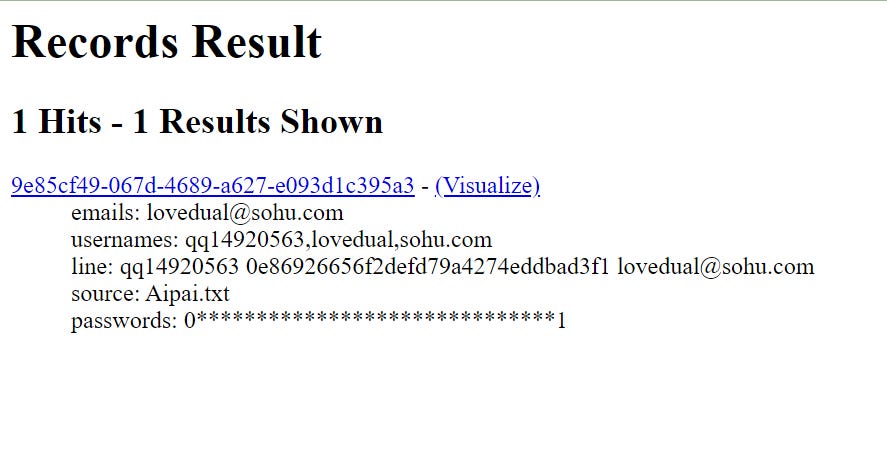
Before we look at that domain, though, we aren’t done quite yet with the QQ username. Looking it up in search.0t.rocks retrieves one result with the email address and username lovedual@soho(.)com:
Querying the email address in search.0t.rocks retrieves another record:
This provides us with some interesting context - in this case showing that the same email address is in fact affiliated with a username similar to the domain above: hack05112.
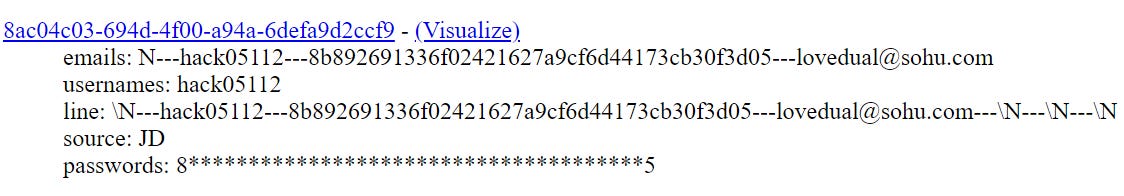
Lovedual also has TONS of other hits on other platforms, but we’ll leave those aside for now - just see below what District 4 brings us with the data removed for now - we have the email in the middle which has appeared in multiple breaches, with one password (to the left and just above the email in the middle), which would be an excellent pivot point:
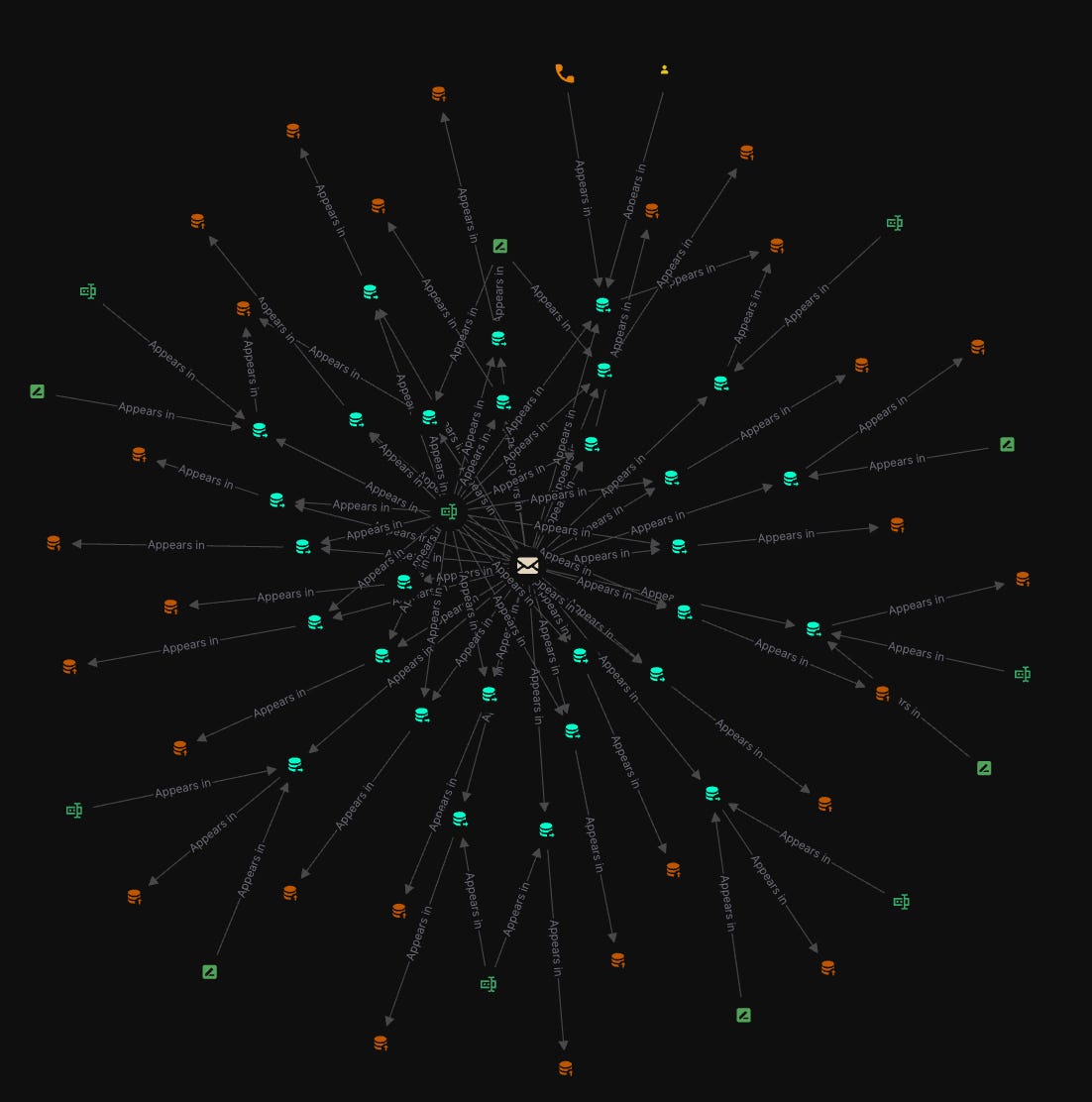
Back to Hack 05112. Hack05112 also appears as a username in the leaked chatlogs:
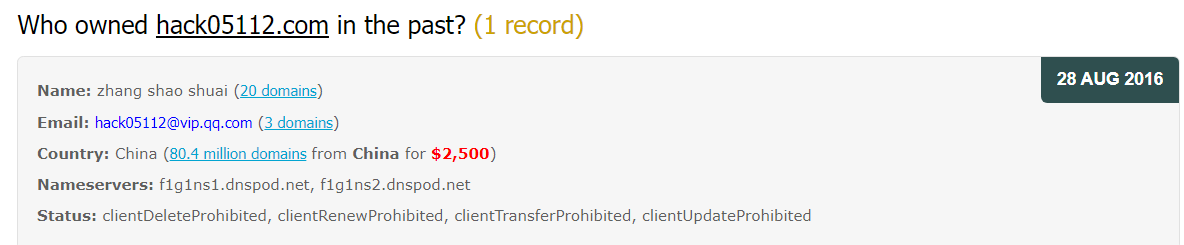
From there, we can then look up the 05112 domain in Domaintools to retrieve its past WHOIS registration, including its registration email: hack05112@vip(.)qq(.)com, which was also used as a registration email for 05112(.)org and hack05112(.)com.
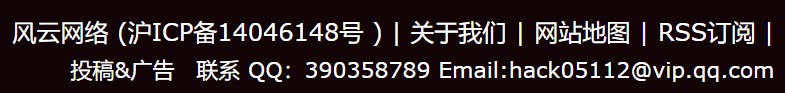
The email address was also used on an archived version of the domain, referring to the Feng Yun network, in this case a Chinese hacking/IT education/competition network:
The site is also listed as a IT/security research site, and looking at any archived versions of it (I’ll save you the eyesore) confirm that.
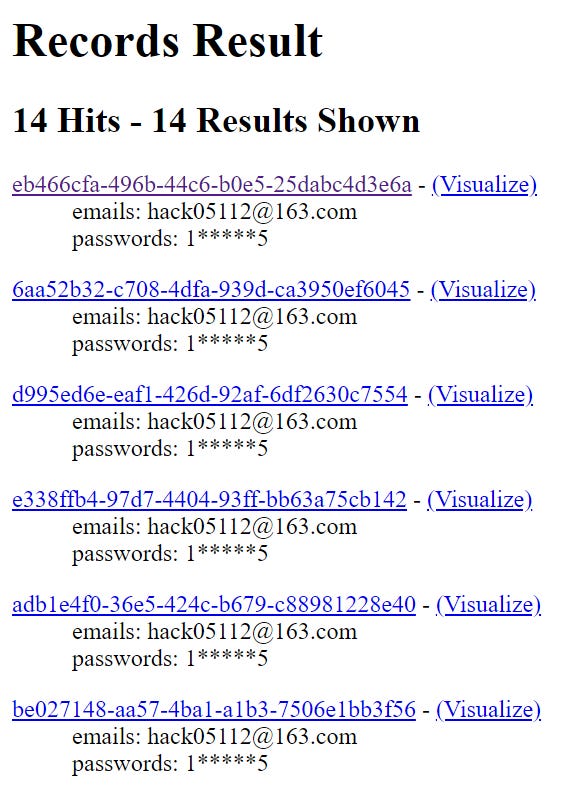
Before continuing, we should do another check for any email addresses registered under 05112 via search.0t.rocks, and from there see that that username at 163(.)com is pretty common, including the typical 1-5 password used for burner emails. I’ve seen Chinese operators use 163 as burner email addresses for phishing, domain registration and so on so wouldn’t surprise me if we have the same case here.
Back to the domains now. Let’s do a historical WHOIS lookup via Whoxy to check out some of the domains:
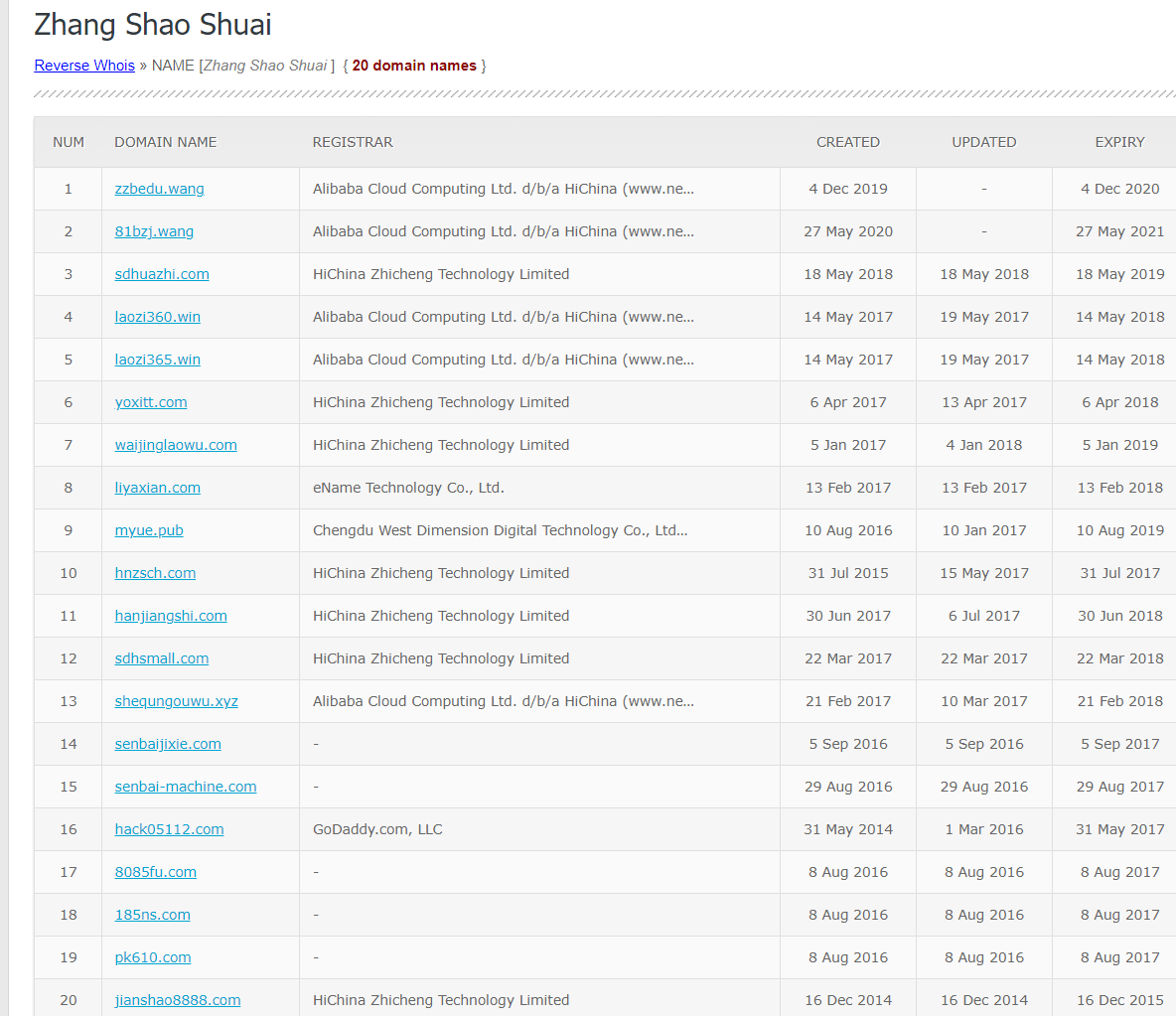
Here we get one specific name affiliated with the email address, Zhang Shao Shuai (possible 张少帅) who has registered 20 domains as per Whoxy:
Not an exact science due to the issues with doing reverse name queries, but overall we see that these domains may be in part related as well. This is a bit much for us to look into now, but we could now seriously look into this individual name going forward to see if 'he’s just a proxy, a fake name or in fact indicative of something.
Let’s now look at the IP addresses hosting the two 05112 domains - we’ll skip the hack05112 domain as it appears to not be active anymore in its original context.
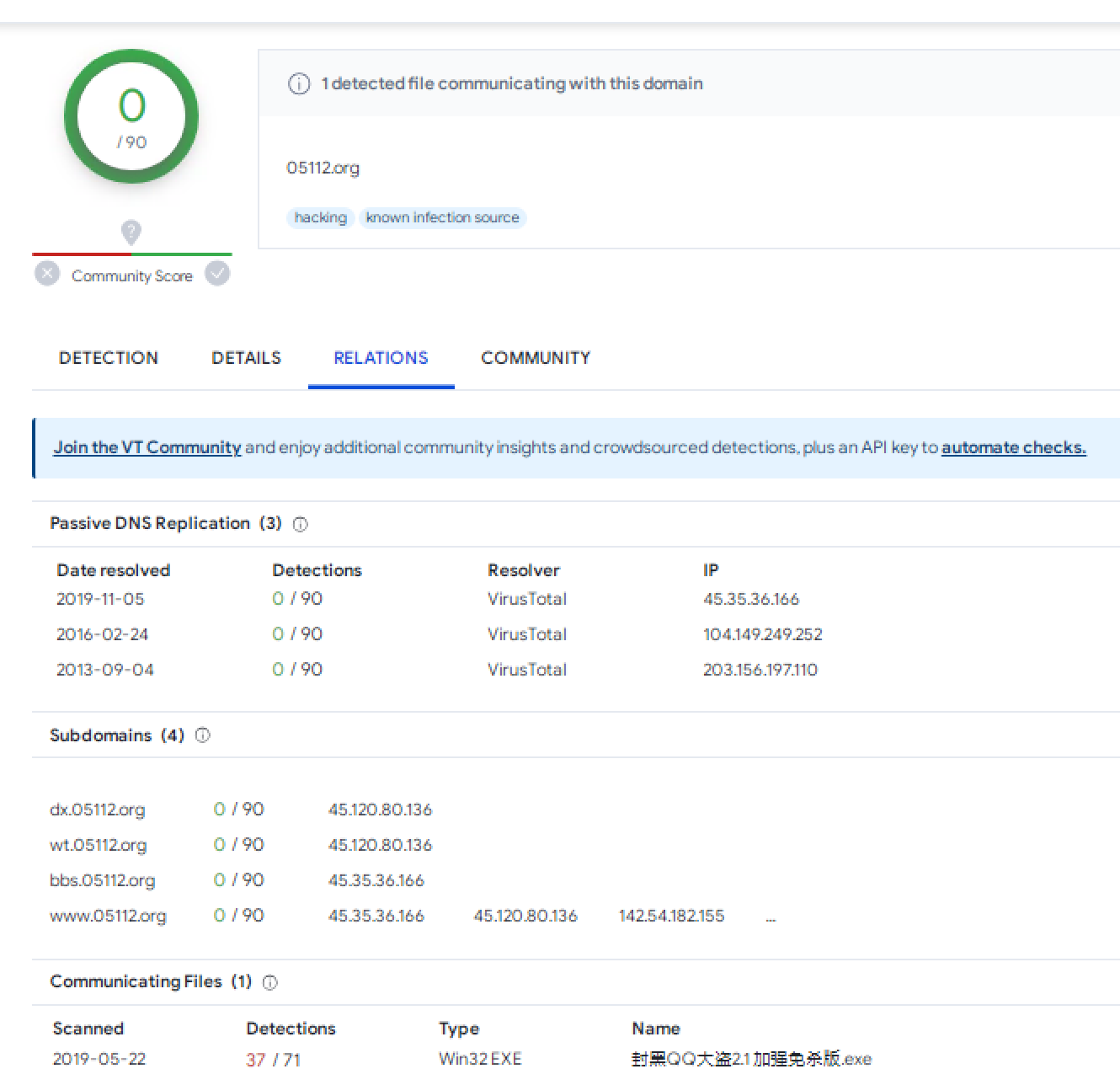
For the .org domain, we see that it’s been tagged as a known hacking domain, and that it’s been hosted solely on 3 past hosts, but communicates with known malware:
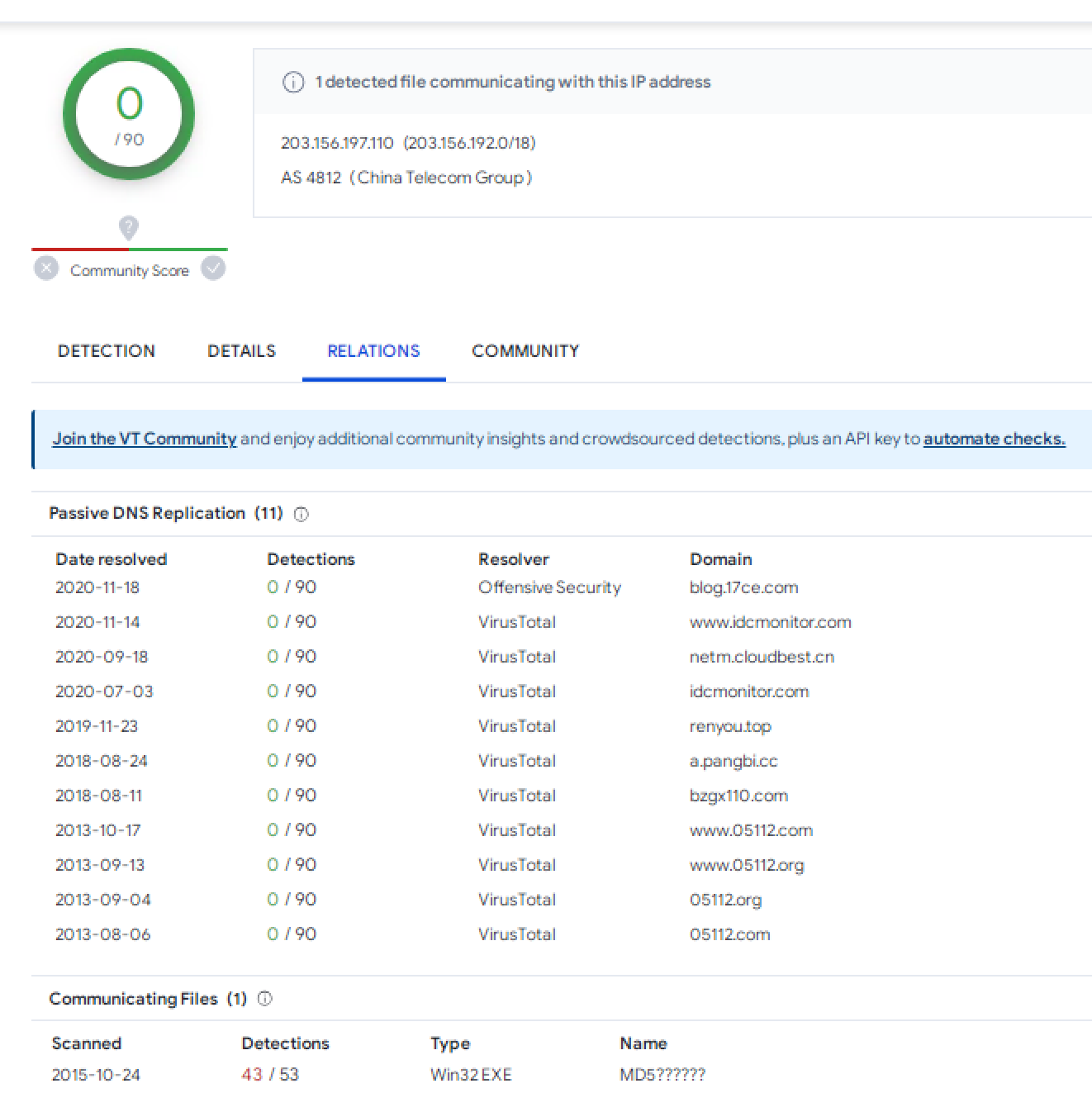
We can also see that the first host for the site once hosted the .com domain, as well as others in past years as well:
This has been fun, but let’s move on.
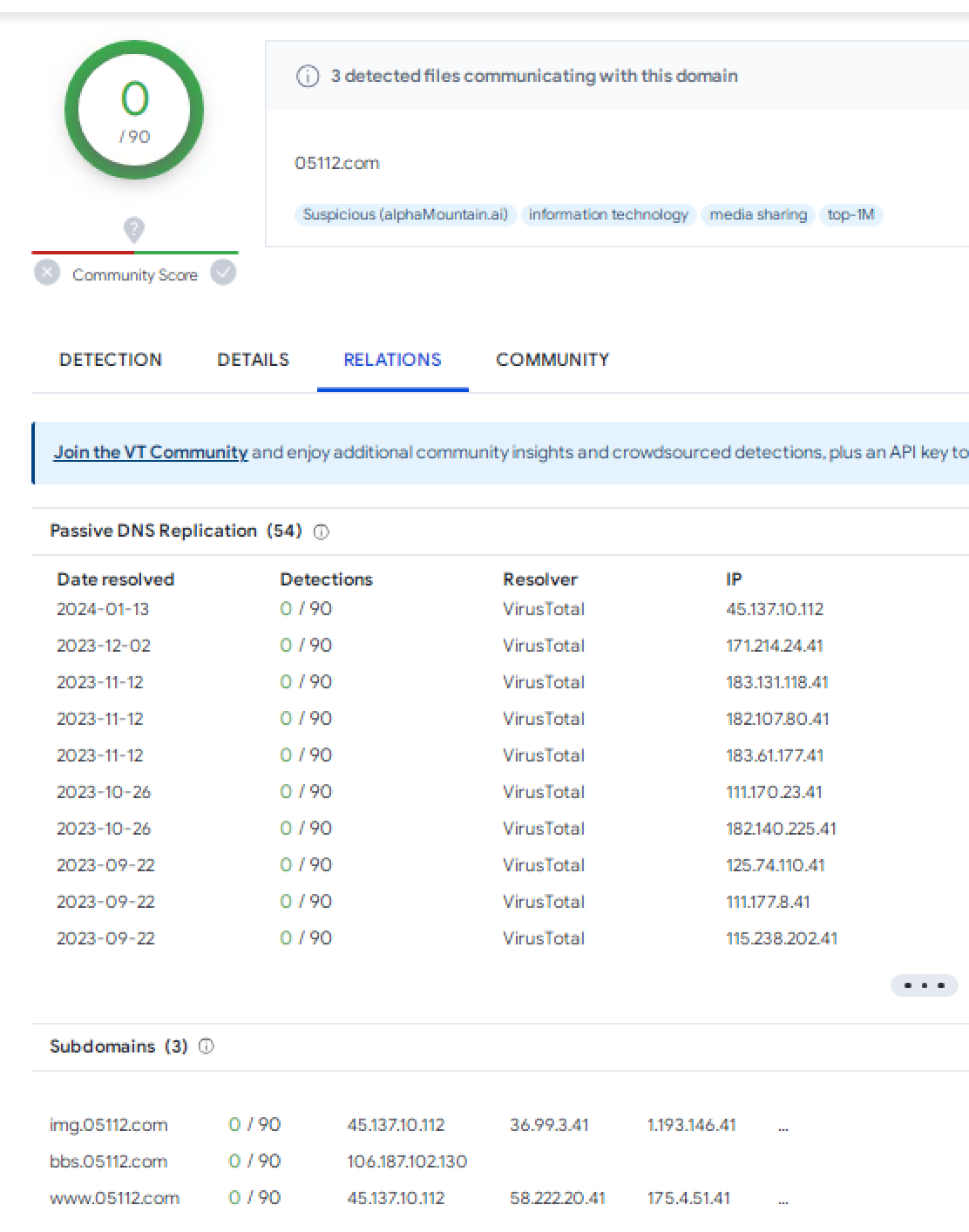
For the .com domain we have some interesting results in VirusTotal: 54 past IP addresses, mostly appearing to be in roughly similar ranges in a few different pairings, and also 3 subdomains.
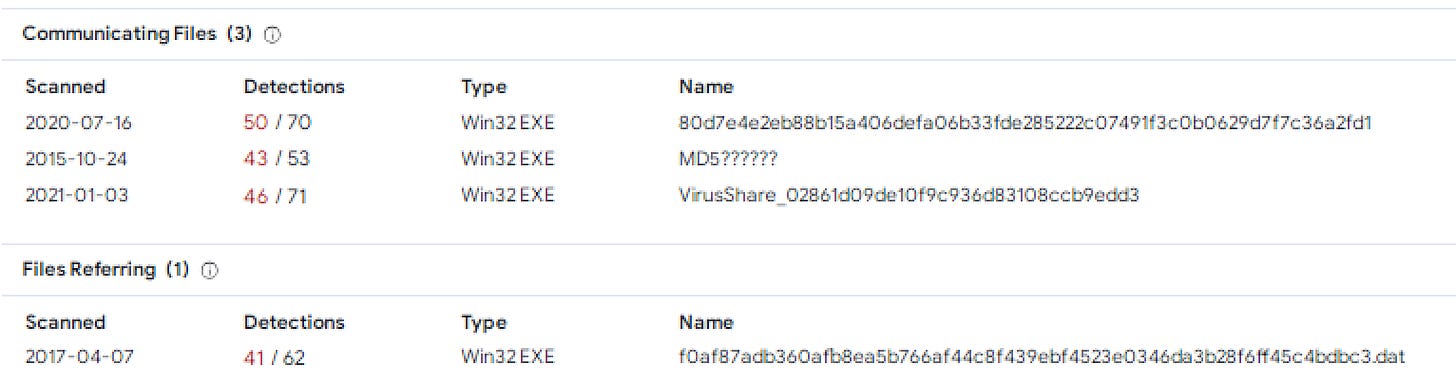
There are also a number of communicating malware files but overall nothing super interesting there:
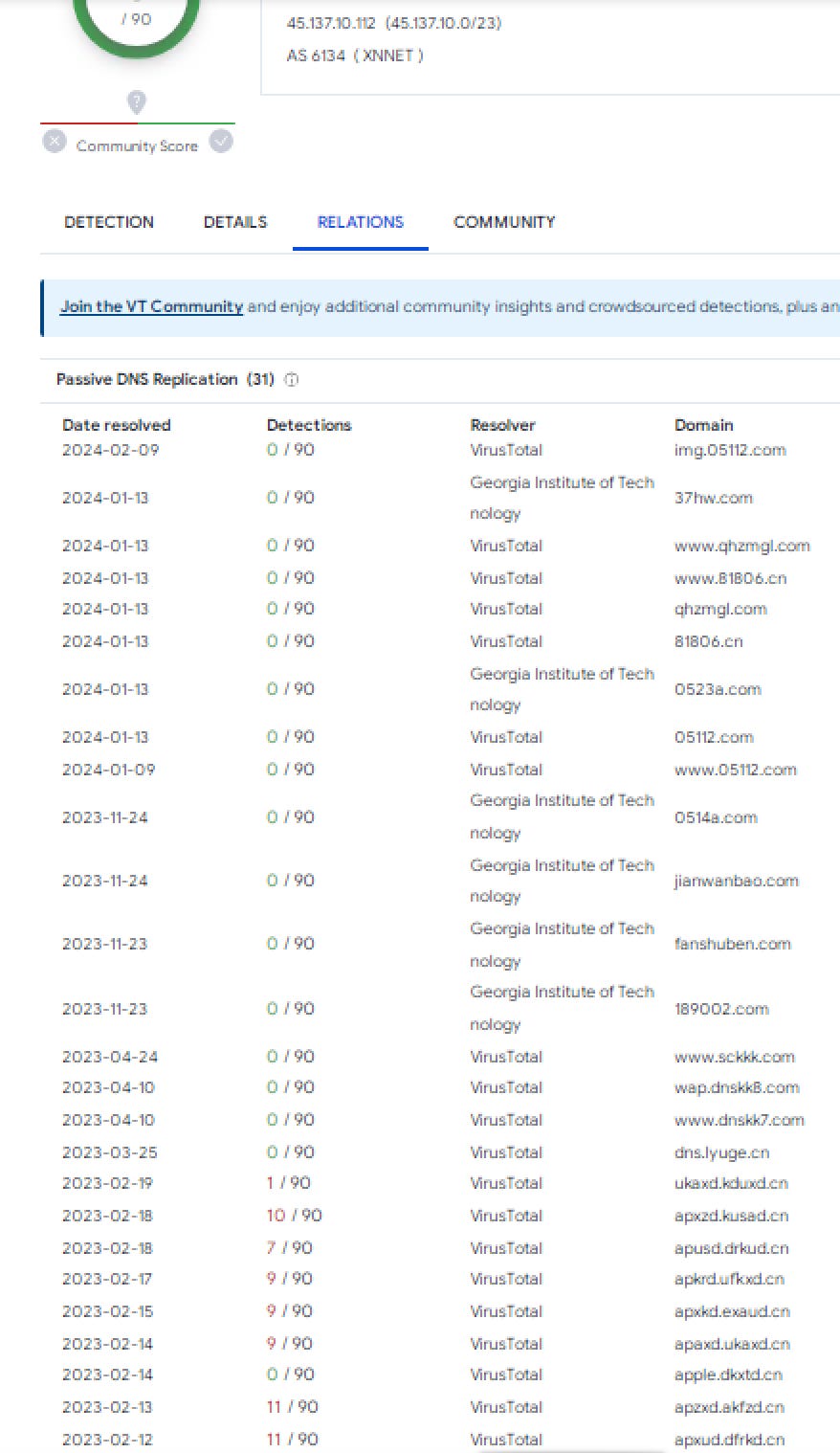
Just looking at the current host for the domain retrieves some suspicious activity with the various hosted domains and subdomains:
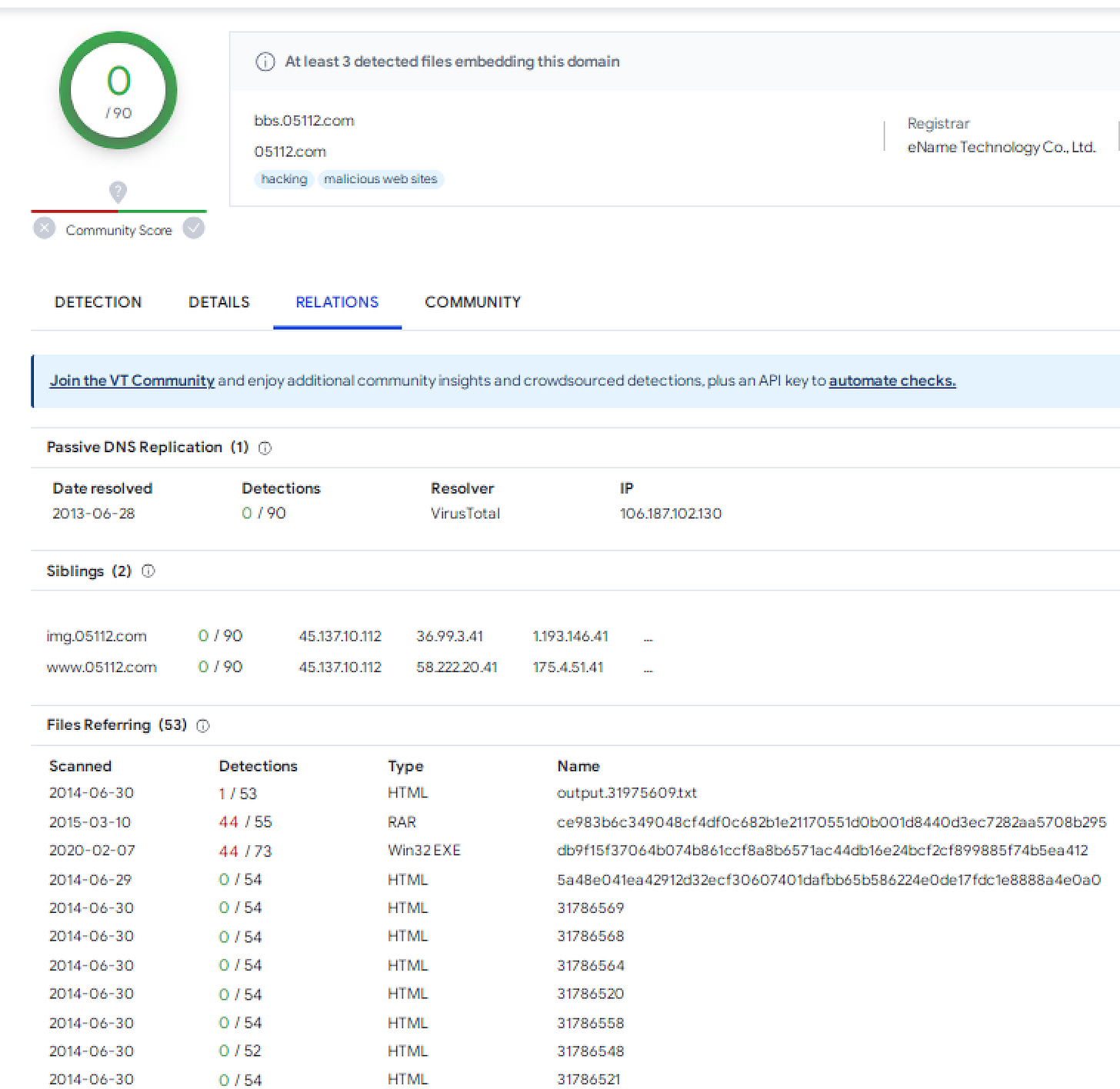
You may recall from the forum post that we found earlier in Google that there was a specific reference to the “bbs” subdomain, so let’s take a look at that. That subdomain has also remained on the same IP address, compared to the others. Here’s where it starts to get a bit more interesting. Looking at the subdomain shows some odd results - it has over 50 different files, some malicious, interacting with it - all scanned back in 2014/2015. Some of them are also odd, sequential HTML files. Something to look into for later.
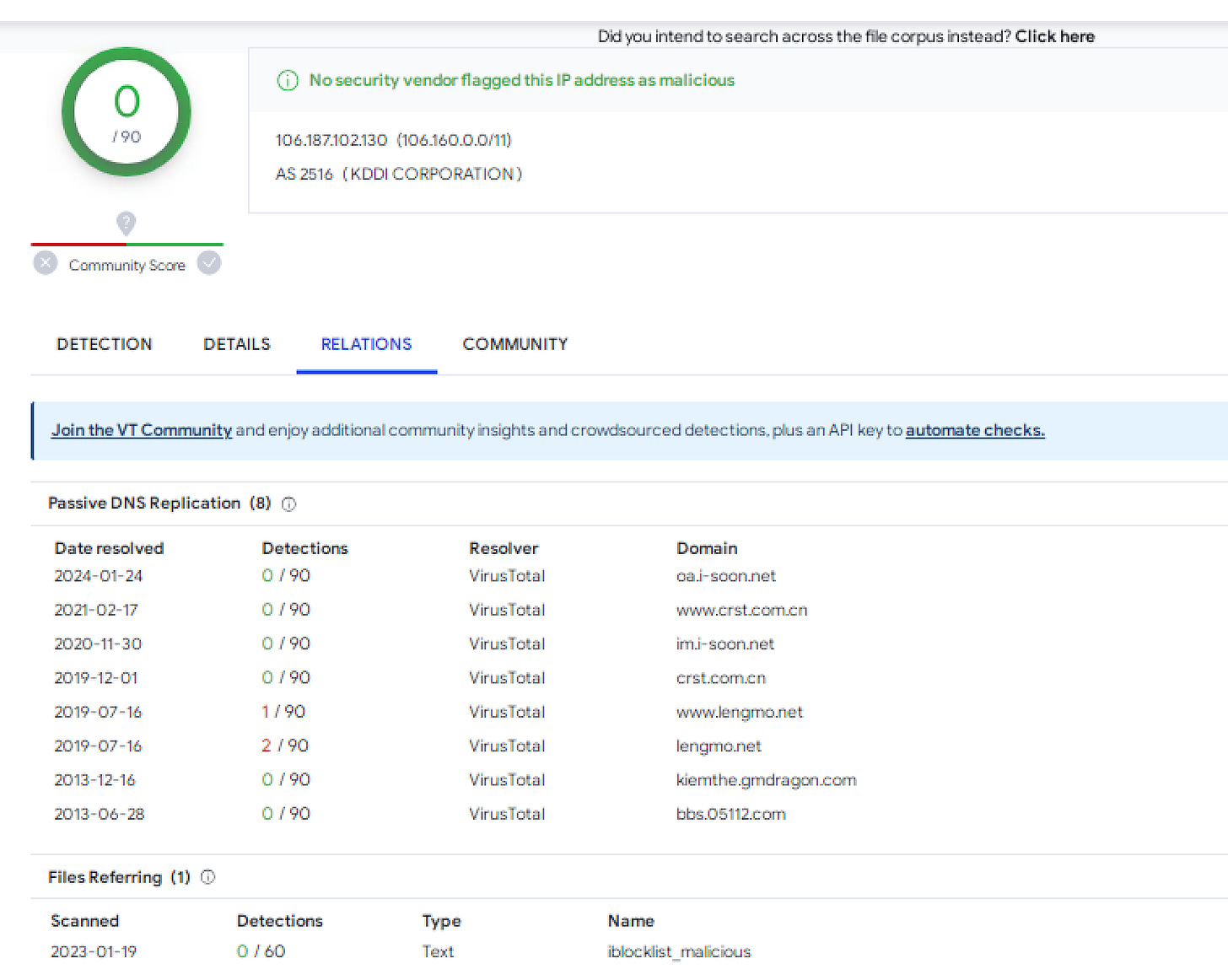
Moving from the subdomain to the host IP shows that this specific host has hosted an i-soon(.)net subdomain, the bbs subdomain, a “lengmo” related subdomain, and even a domain for the CRST, a Chinese hacking group as identified by Baptiste Robert here.
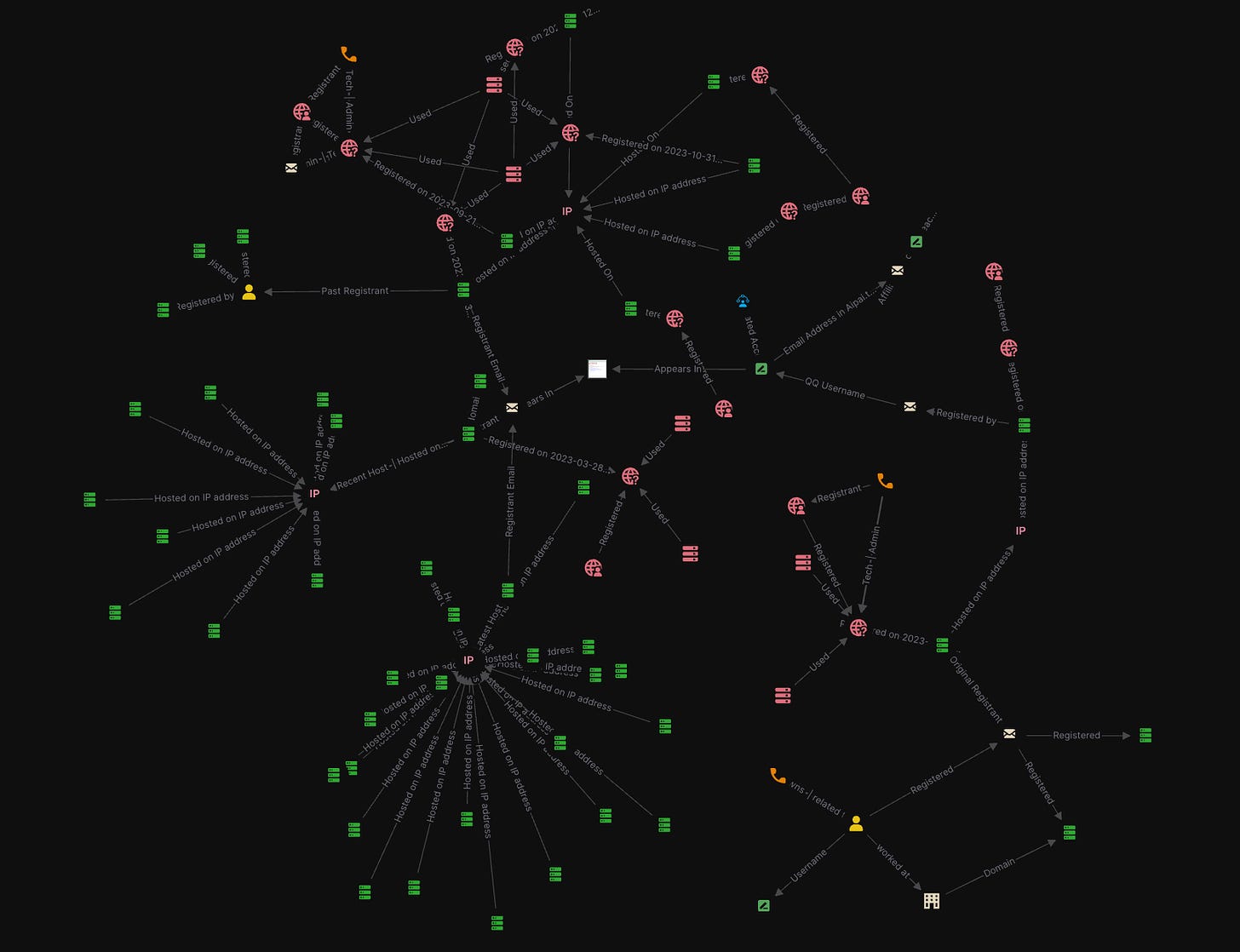
Let’s recap our findings so far. Having started off with no real end-goal in mind but rather an open-ended attempt to map out as much as possible, we have mapped out small part of the overall presence of the i-Soon company based upon its recent Whois records, checked out a few individuals to uncover more information on the most recent registrant, and we have some potential leads even on who this individual may be as well as other identifiers. See a zoomed-out and still basic visualization of some of the findings below just to get an understanding of the possible directions to continue investigating:
We’ve come across an effective cluster of activity here surrounding the last registrant of the site and the 05112 domains, so that’s a nice start in of itself.
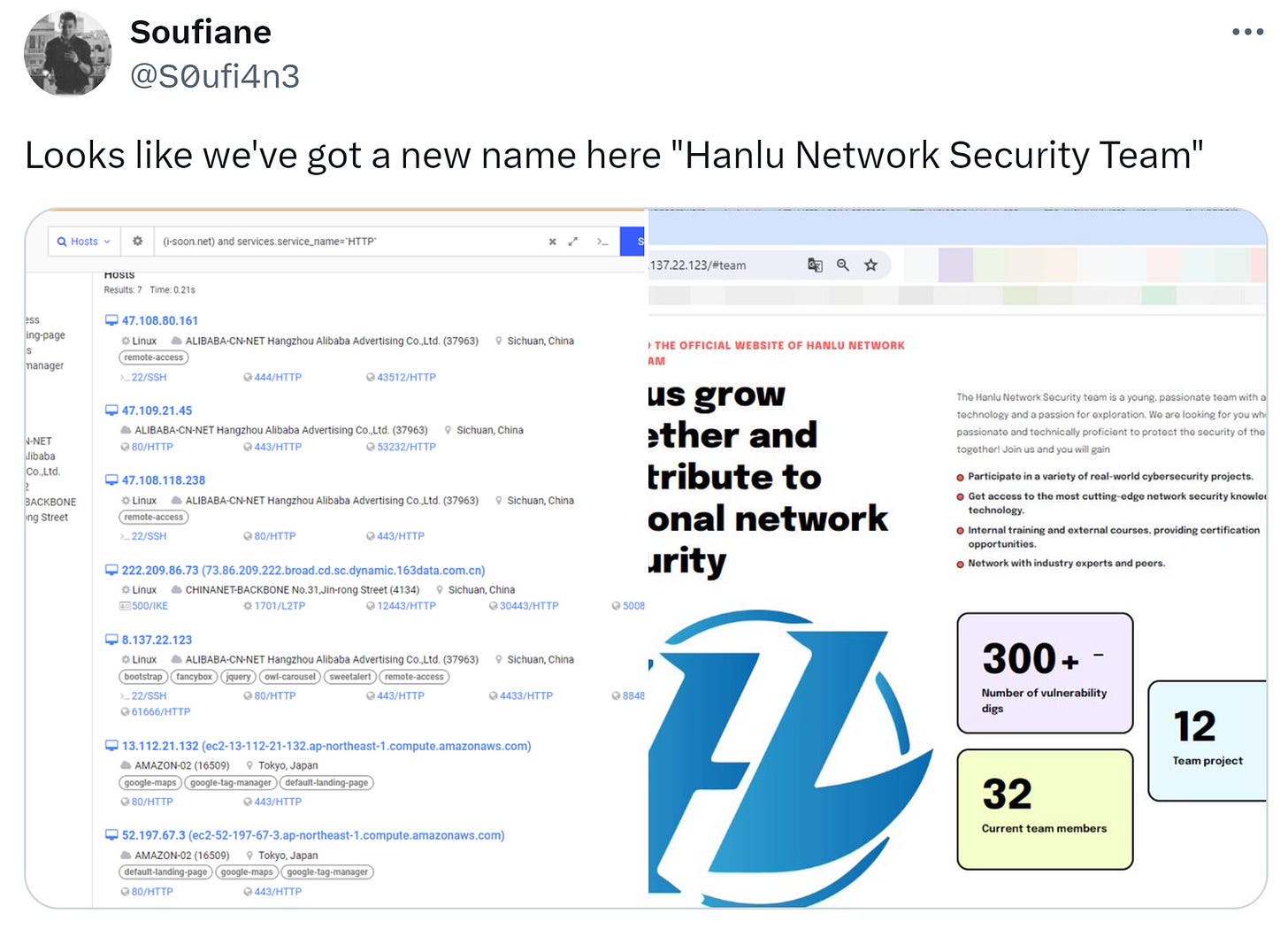
The work never really ends though. There are myriad ways to pivot upon this wealth of information. Soufiane, for example, has found some other interesting hosts based upon searching the domain name in Censys, coming across another front name - Hanlu Network Security Team.
From here, additional research and pivoting could be done for hours, if not days and beyond considering the scope of activity here, and I’m sure that others will begin to find much, much more.