Welcome to Memetic Warfare Weekly.
My name is Ari Ben Am, and I’m the founder of Telemetry Data Labs - a Telegram search engine and analytics platform available at Telemetryapp.io. I also do training, consulting and research so if you have any specific needs - feel free to reach out on LinkedIn.
Before beginning this week, I want to take a moment to announce the launch of Telemetry 1.0! I’m still getting used to not having “beta” appended to the end there.
Telemetry 1.0 is the full, commercial version of Telemetry search and analytics for Telegram data.
Users can use Boolean logic, multiple keywords and more to search intelligently across 1.5+ billion Telegram messages from over 1.07 million public groups and channels, and of course view analytics for those groups and channels.
What does this mean for our users?
Firstly, we're going to keep full access available to all users until April 1st to ensure a smooth transition, time for bug fixes and more. If you come across any issues - let me know here or via admin@telemetryapp.io.
Those who purchase an account prior to April 1st will receive a one time credit boost or alternatively a discount for a limited time period on future plans purchased.
We've also uploaded a much faster and more stable version of Telemetry to the site, so check out our new speed.
When we reach April 1st, our paid plan users will get to keep using our advanced features, including but not limited to:
- API access from Pro and above
- Channel/Group Analytics
- Expanded historical Data
- Significantly more results per query than Freemium
- Export to CSV for UI searches
Supporting Telemetry now by purchasing a paid plan will help us further develop Telemetry into an even better product, letting us:
- Exponentially increase our data acquisition
- Develop new features, such as a monitoring suite
- Add new analytics
- Implement an automated channel/group update system
- And much, much more
We'll keep a Freemium plan available for those who want to use it, and it'll enable you to search our database in a limited fashion and with fewer results.
I’d like to add a personal note to the readers of this blog. Telemetry has been a shared project very close to my heart for the past year +, and supporting it by purchasing a membership directly supports me, the blog, and IO/CTI research. I truly and deeply hope that you all find it as useful as it’s been for me in my work.
On that note - let’s begin this week’s post!
We’ll start this week with a shoutout to Kirby Plessas, who published new findings recently on how Facebook manages Facebook page IDs, available here.
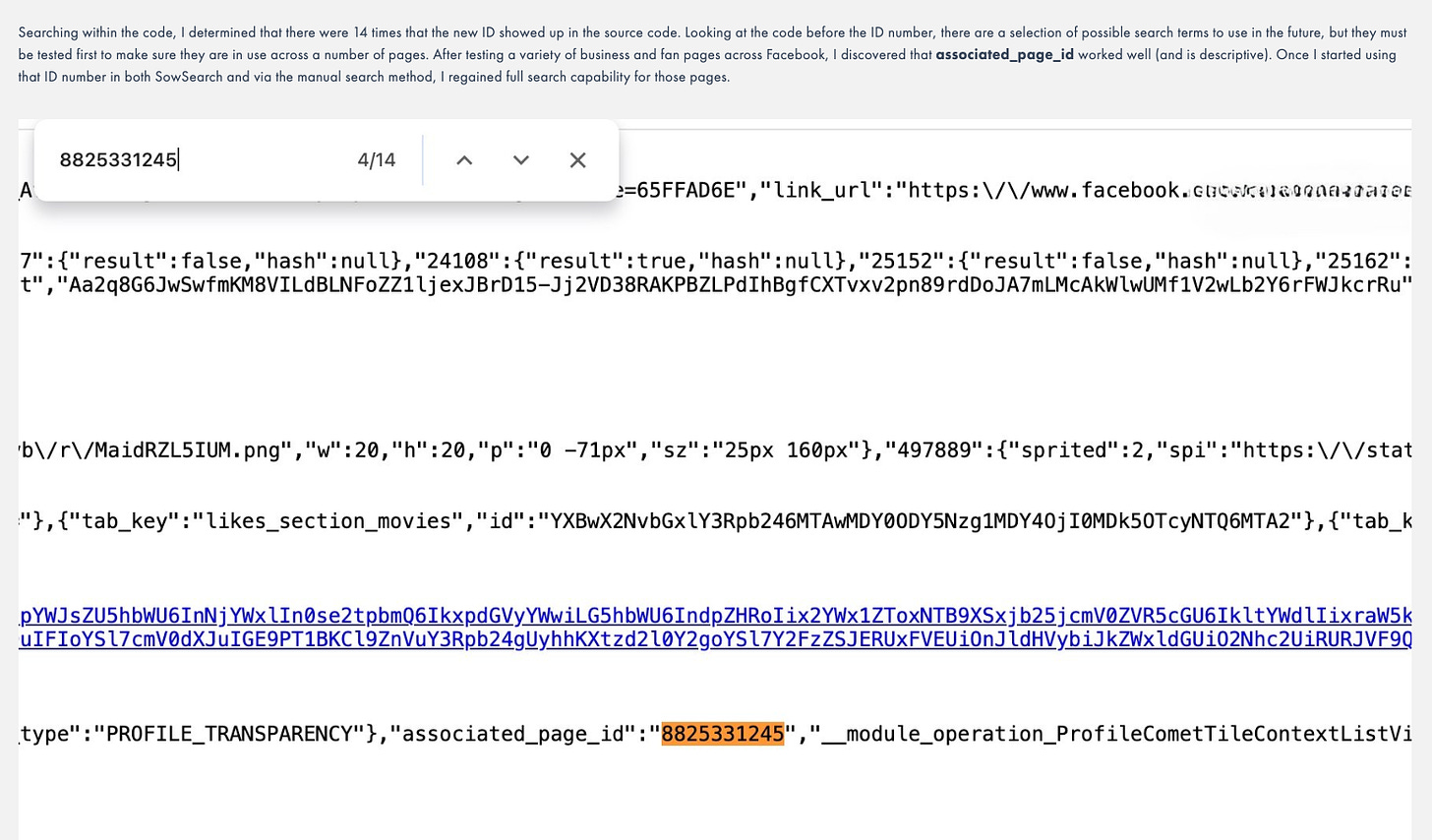
Plessas shows how tried-and-true methods can change on a dime, in this case showing that the base64 URL method and SOWsearch aren’t usable anymore due to the old page ID being retired.
I’d recommend reading her whole post (it isn’t long), but to make a short story even more concise, she found mentions of a new page ID that she could confirm in the source code, and eventually found the field, “associated_page_id”, for the new Facebook page ID.
The utility of this in IO should go without saying.
We’ve been Wuhan-ed!
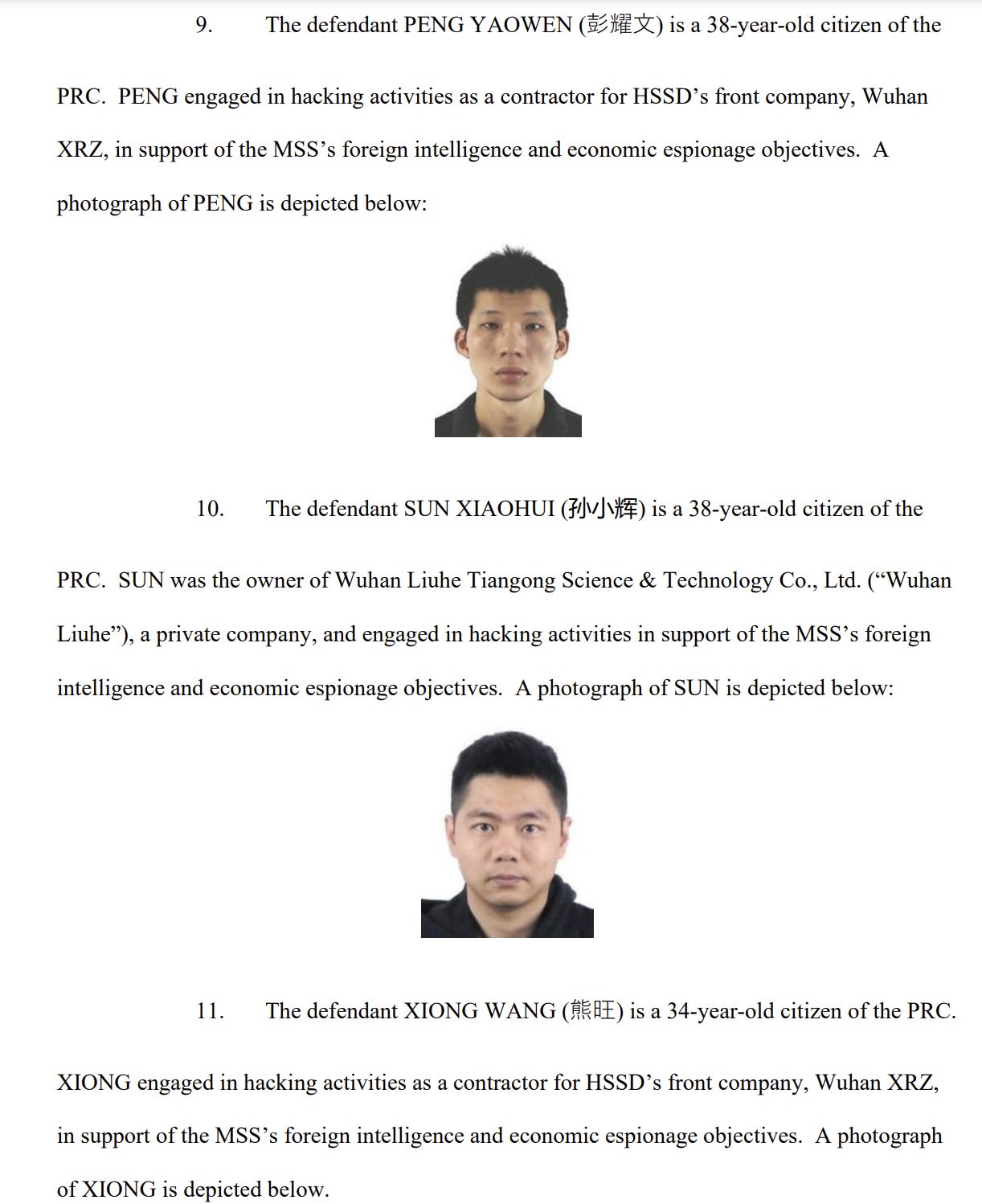
CNN’s Sean Lyngaas has reported that the US DOJ will be indicting Chinese hackers soon belonging to APT 31. These hackers utilize a Wuhan-based front company for their activity, and apparently, as per Lyngaas, it’s the same cluster as investigated by Intrusion Truth in the past.
Interesting how these things work, huh? Who knows who’s really behind Intrusion Truth, but if it is a hack and leak OSINT-washing front - it’s certainly showing others how quality and ethical IO should be done.
Those that want to see the indictment can see it here, I’ll add my perspective on a few highlights:
The indictment itself refers to the front company exposed by Intrusion Truth - Wuhan XiaoRuiZhi:
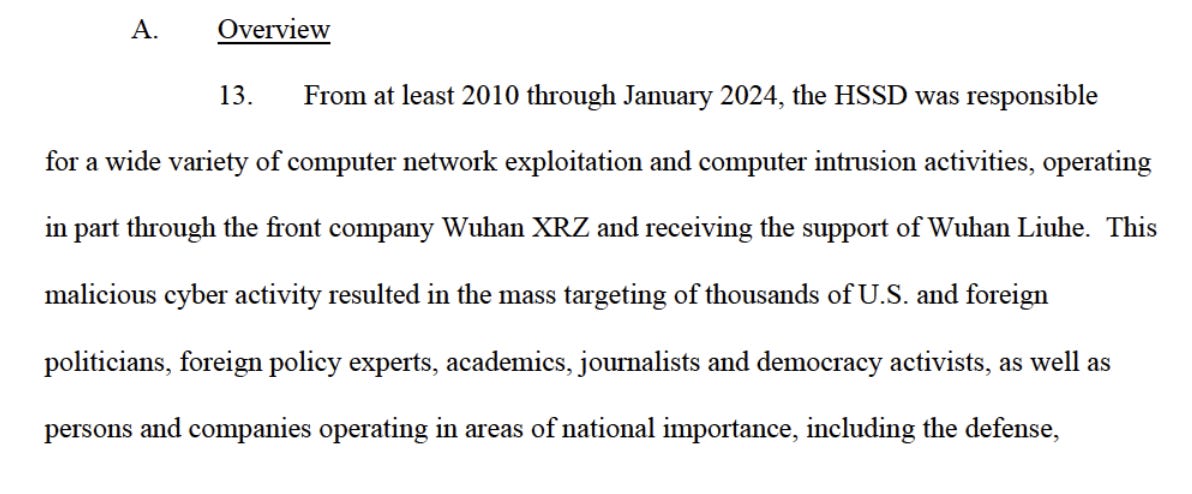
Interesting information on the long-term scope of activity, originating in 2010:
Tens of thousands of phishing emails were sent as the initial intrusion vector:
Election campaigns were of course targeted:
Apparently a zero day was burned to compromise a cleared US defense contractor, which then enabled them to use a simple SQL injection attack to create an admin user account.
I may be wrong here, but an SQL injection on a web form input box is to my understanding the kind of thing that shouldn’t pass a security audit/pentest for any high-risk industry, but I’m willing to be corrected here by those more knowledgeable than me.
Another interesting insight was the speed with which the APT set up malicious domains impersonating an American steel firm and an international steel trade forum following US tariffs on imported steel:
A notable specific intrusion - I wonder which polling firm or news outlet it was:
There’s more to read in the indictment, but the above were the key points I wanted to point out.
La Dolce Mema
While browsing LinkedIn, I came across a post from Matteo Pugliese on Russian IO activity targeting Italy.
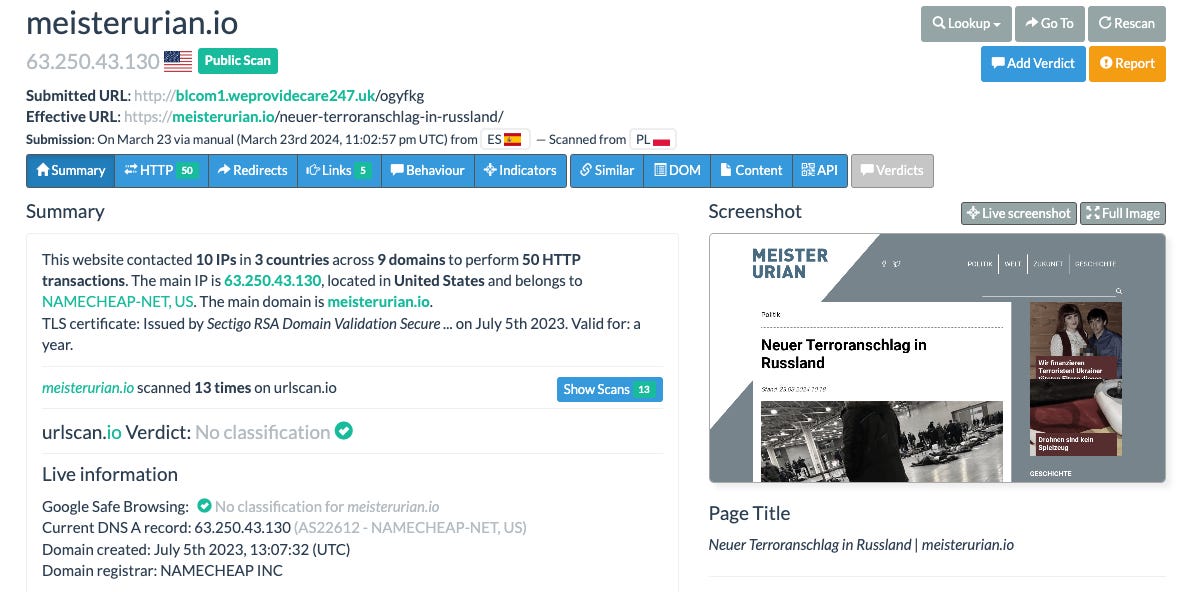
Immediately upon seeing this it seemed clear to me that this is Doppelganger-related due to the odd URL probably being used for redirects, and is probably a “Stage 1” domain as defined by Recorded Future. Let’s see if we can support that assumption.
The account itself could be of interest, but in this case I decided to not bother with Twitter.
First, let’s note the URL in the above link. That refers to a specific subdomain, the part beginning with “dmu”, and also a specific link on the domain, the part beginning with the final slash /794 etc.
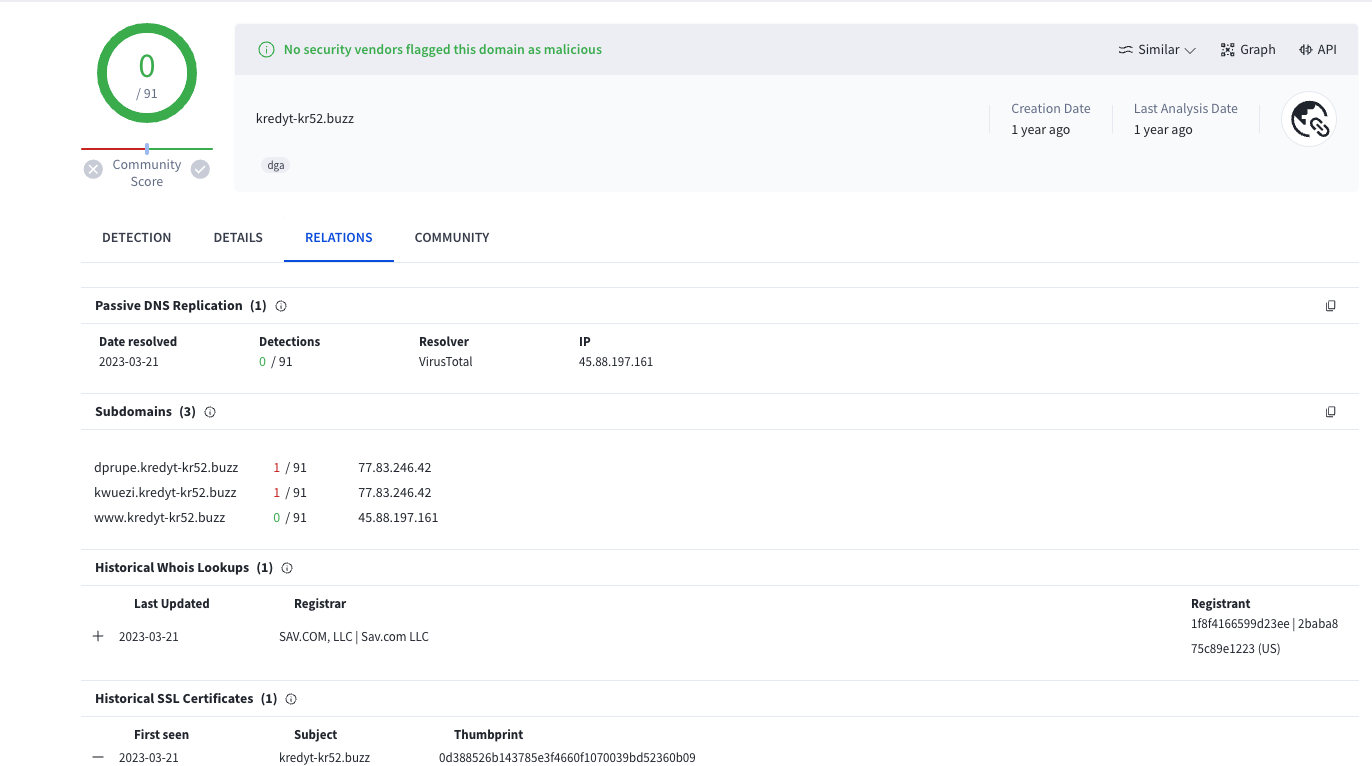
You could input the URL as is to VT and it’ll know what to do - once the page loads, open the relations tab. You’ll be taken to a page looking like this:
We see here that it’s only ever been hosted on one IP address with redacted WHOIS. In these cases, I always recommend looking at the subdomains. Subdomains can be hosted on different hosts (i.e. a different IP address) and thus provide us with two new vectors to check out - the subdomain itself and the IP upon which it is hosted.
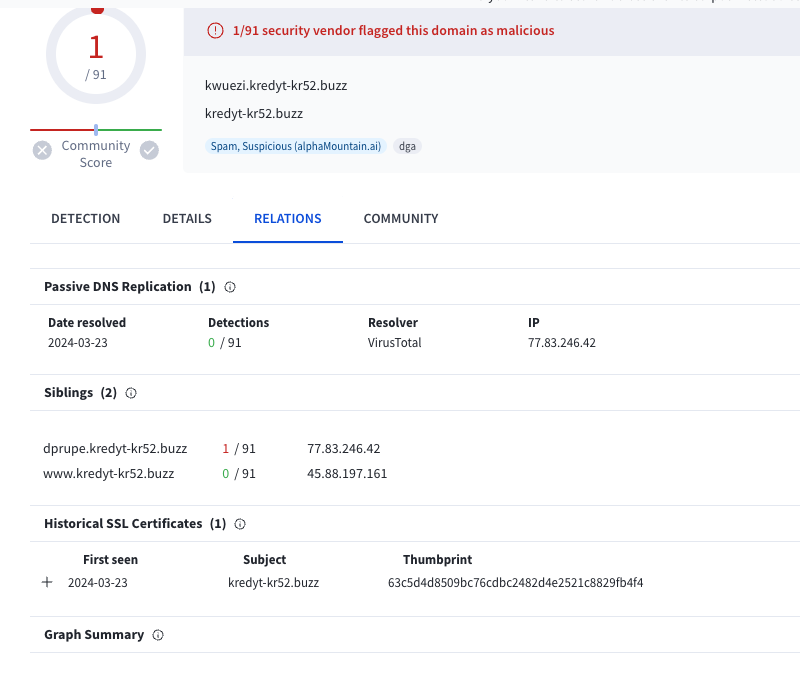
In this case we have two subdomains hosted on the same IP address. Checking out one shows that it too has only ever been hosted on one IP, and is flagged as suspicious by at least one AV provider.
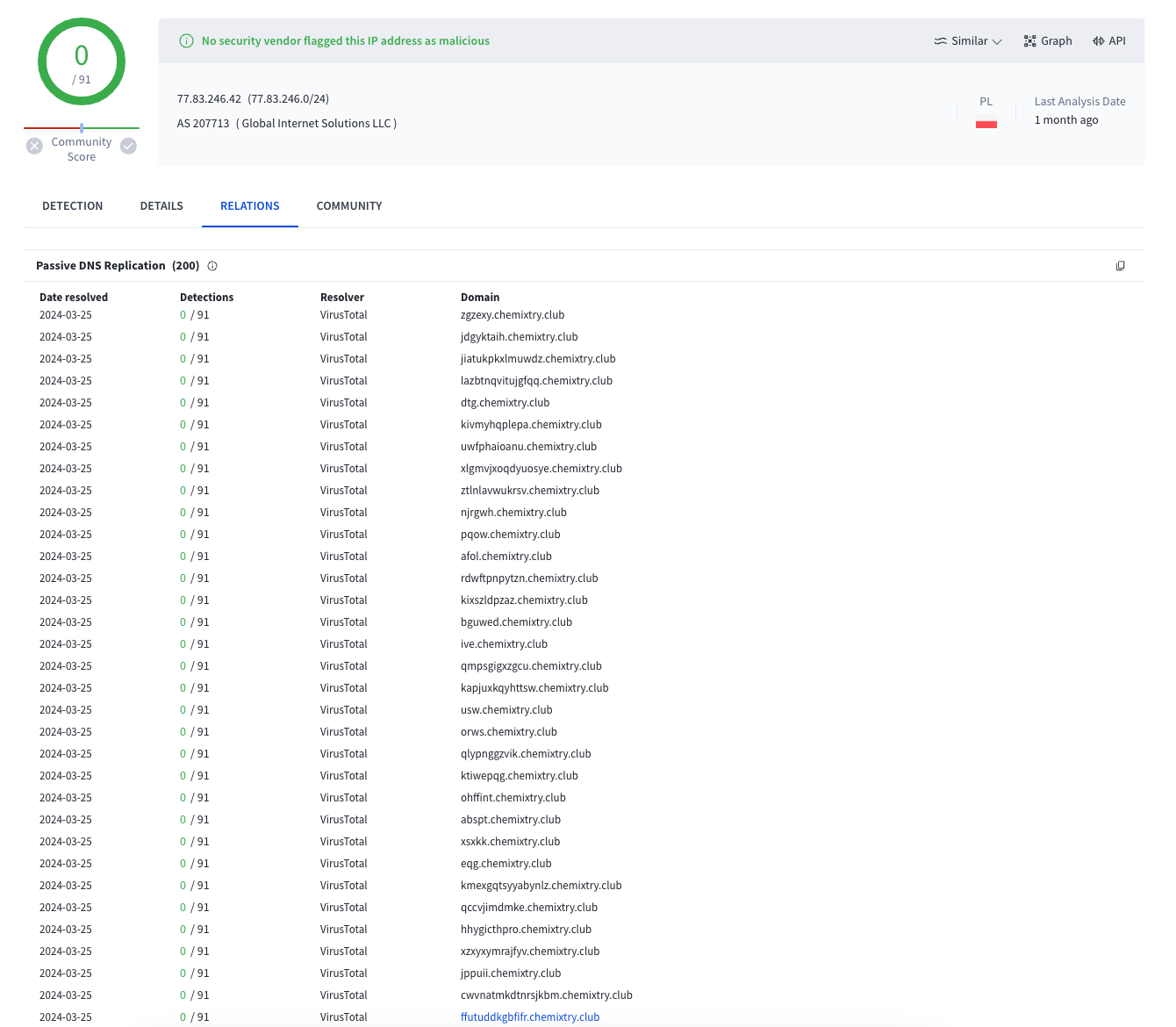
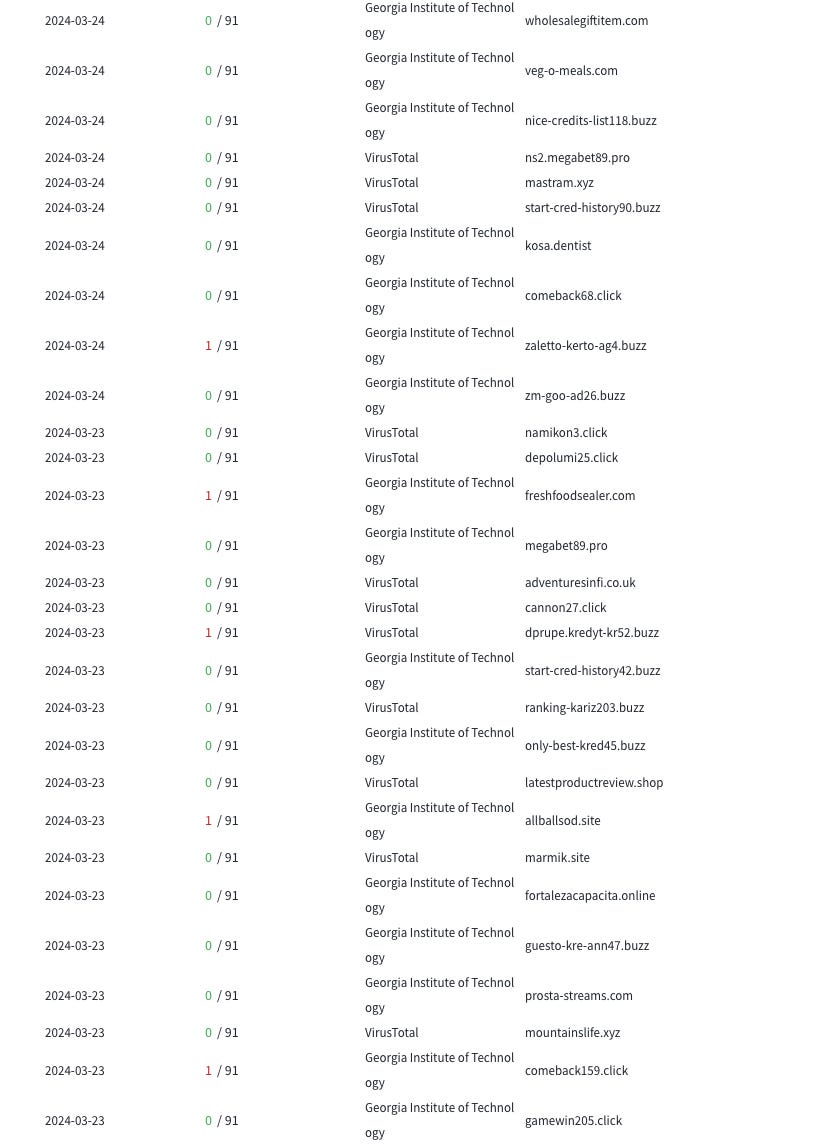
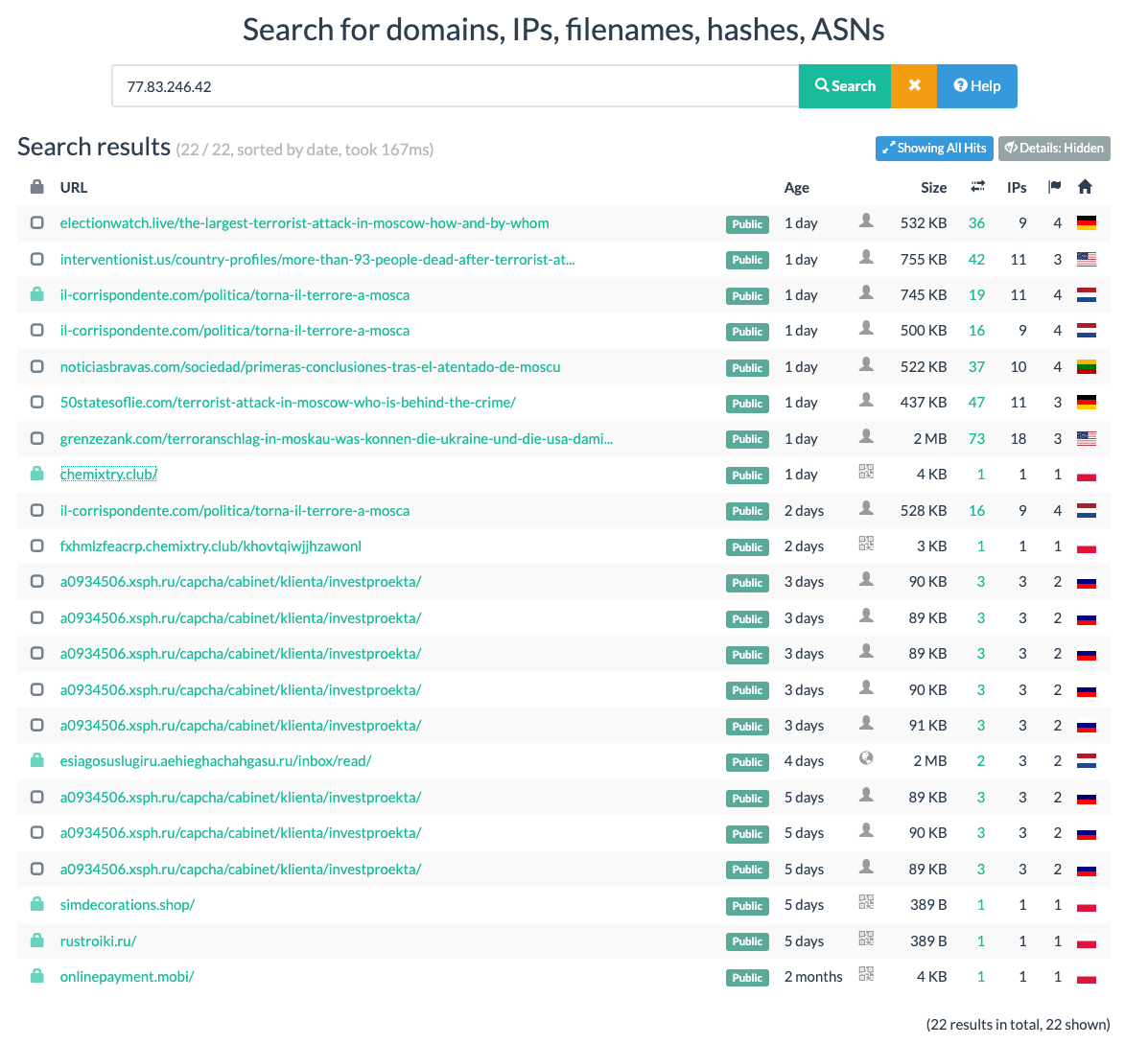
For those interested in following along, click on the IP address in VirusTotal and move to the relations tab. Here we see that the host itself is Polish and hosts primarily subdomains belonging to the “chemixtry(.)club” root domain.
We have to scroll through dozens of subdomains belonging to the chemixtry domain. Eventually we’ll come across others which are also highly suspicious:
Note also that many of these are “.buzz” top level domains, and that the buzz domains all have similar naming conventions similar to our domain of origin, with “kredyt” or “credit” recurring in many of their names. This is a useful heuristic for grouping domains together as well as improving our understanding of this host.
Let’s now go look at the Chemixtry domain, as it’s quite prominent.
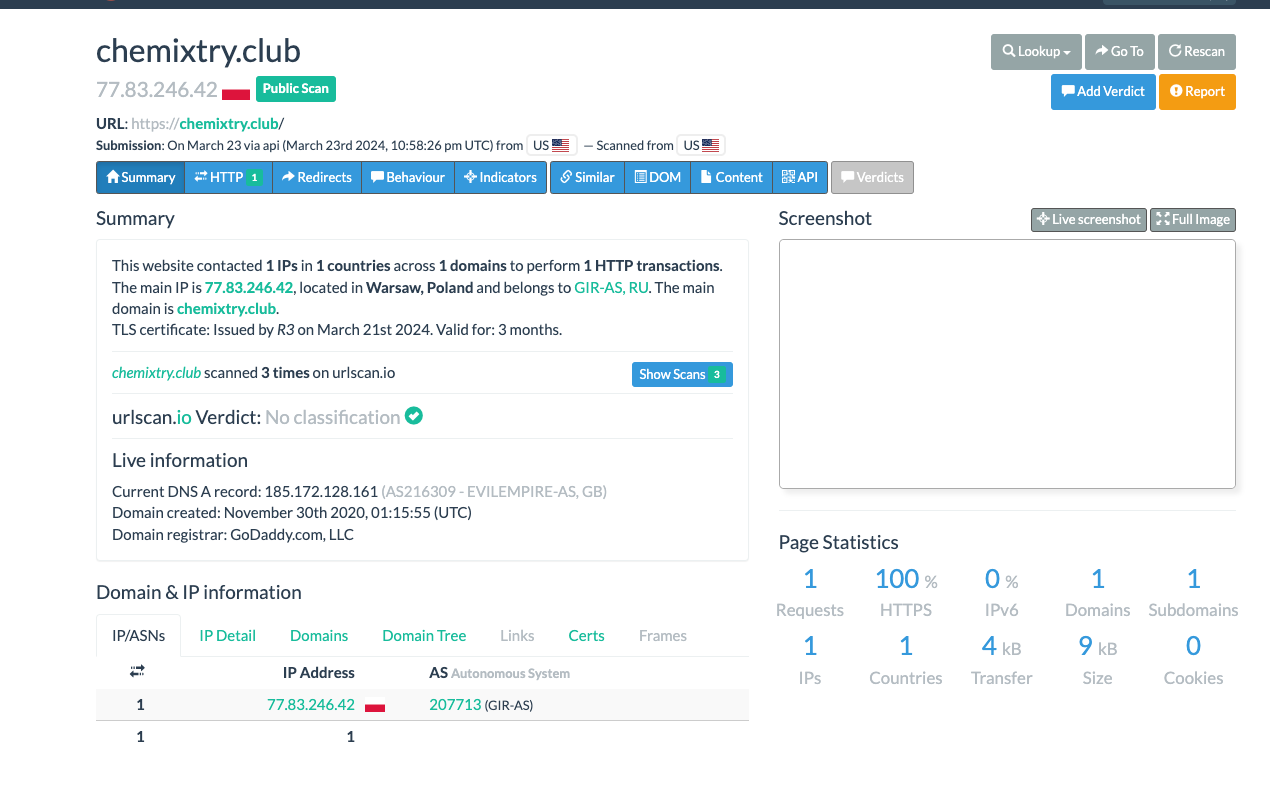
Looking at it in URLScan.io shows some interesting findings:
Some things immediately caught my eye. There’s no screenshot of the domain and only one interacting IP, so the domain is probably not up, and the subdomains appear to be the main story here. The AS is also based in Poland, but is owned by a Russian company - highly suspicious as-is.
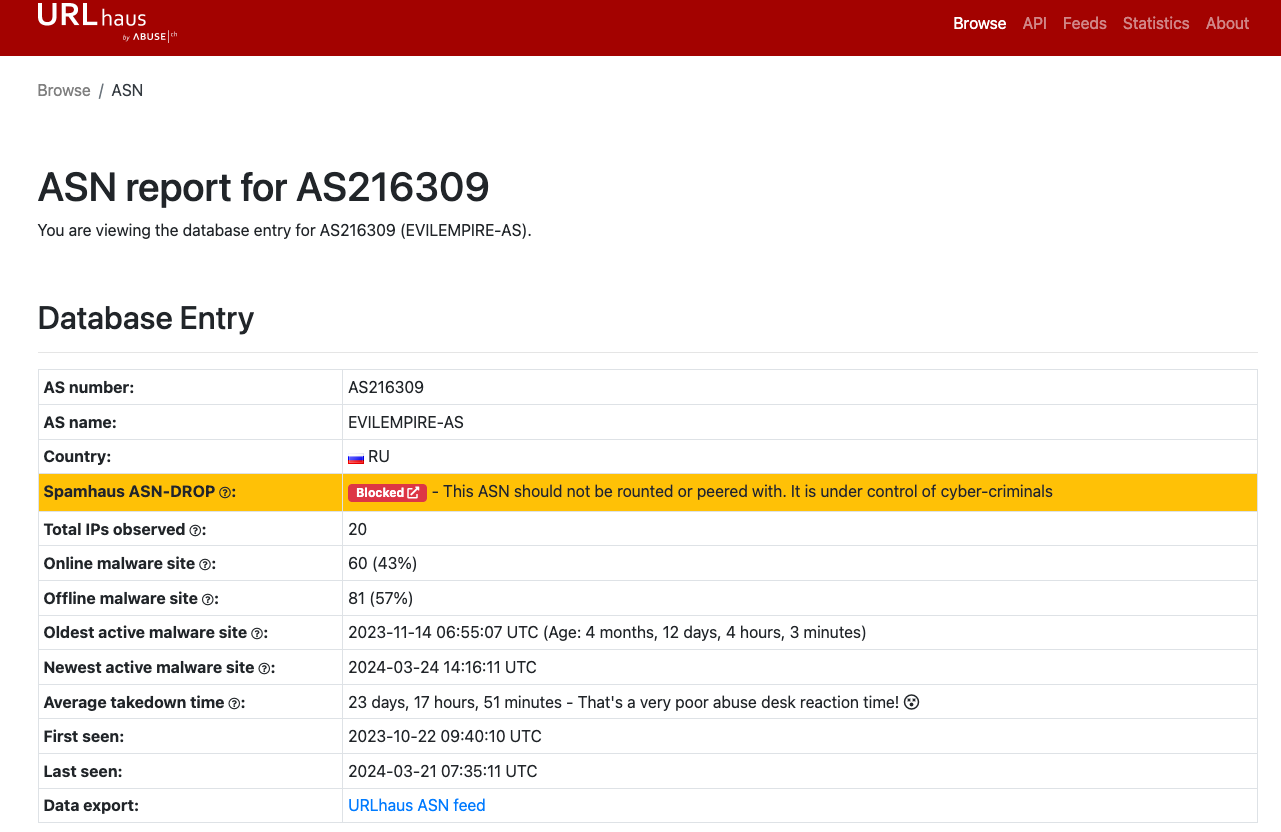
Also, what is up with that DNS A record IP? The IP’s AS is named “Evil Empire” - either just a cool name chosen by cybercriminals or perhaps a reference to Reagan’s “evil empire” speech - either way, a bold move. Checking it out on URLHaus shows that it is a blacklisted AS controlled by cybercriminals.
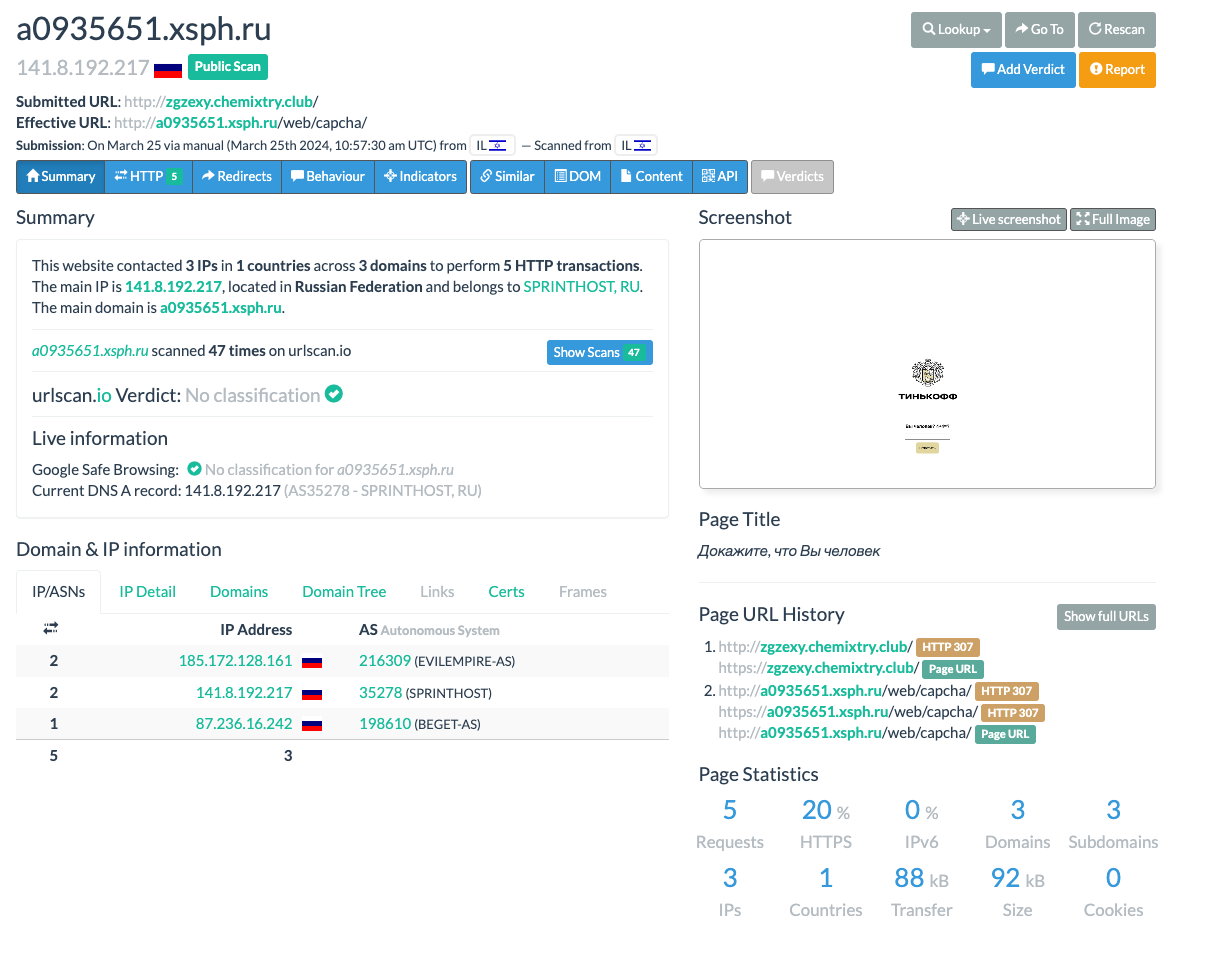
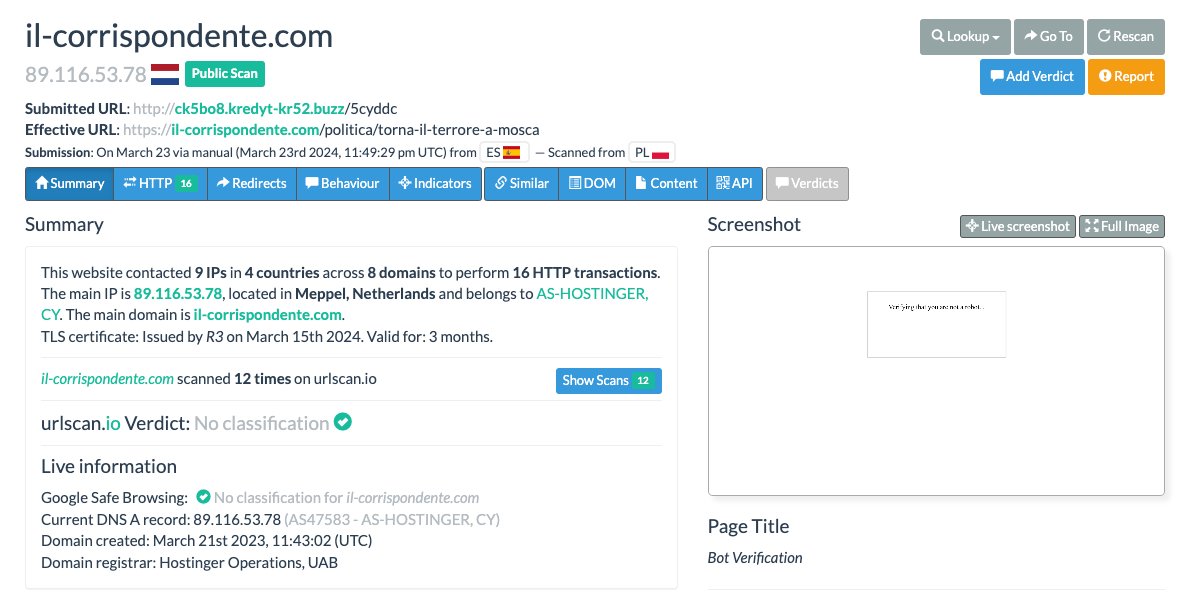
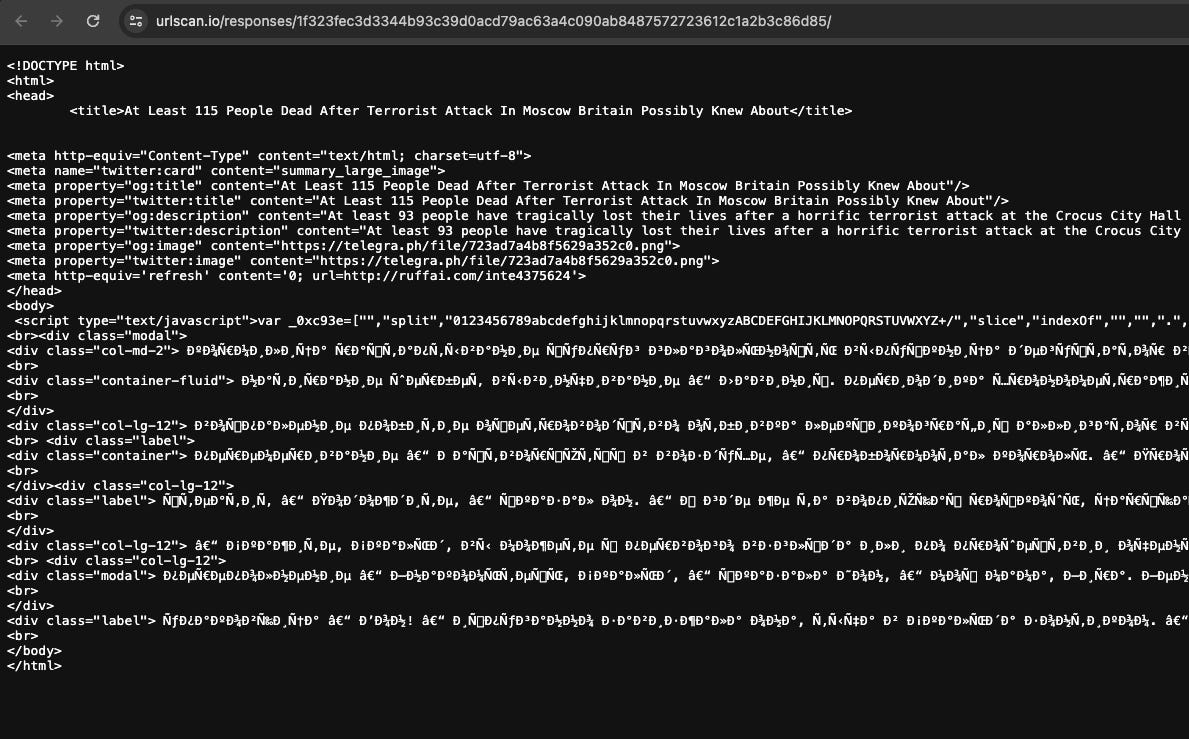
Going back to URLScan, we can look at one of the subdomains to see what’s up:
Here, we get a redirect to a different odd subdomain of the root”xsph” domain in Russia. This one is also hosted on an Evil Empire ASN and is a login panel with a captcha for “Tinkoff”, which after googling is apparently a Russian online bank - see the admittedly small screenshot in the upper-right section of the above image.
So, appears we have a phishing page here or potentially something else. Not surprising considering its AS.
Let’s recap - we have one inactive root domain, and dozens of subdomains - at least one of which is hosted on a suspected bulletproof host/cybercrime-affiliated Russian AS.
These domains are hosted on the same host as suspected Doppelganger activity. This may well be the sole connection, and it wouldn’t necessarily be odd to see that the hosting overlap is the only shared element connecting Doppelganger and cybercrime infra. This makes a lot of sense actually, as it’d be quite hard for Doppelganger operators to find any reputable Western host for their activity, and using bulletproof hosts may make the most sense.
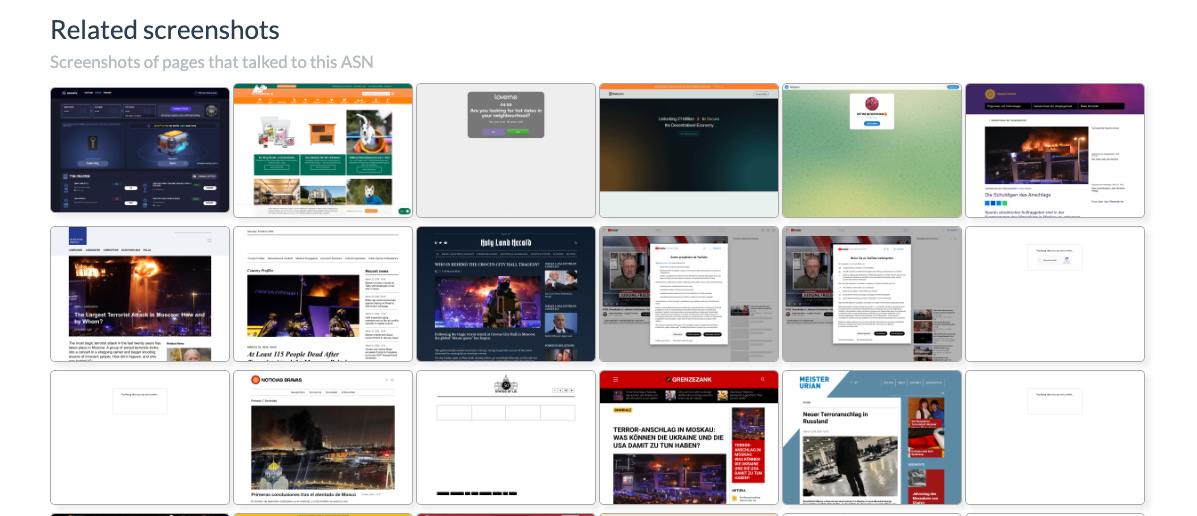
Anyway, going back to the root “chemistry” domain - we can check out its AS as well via URLScan.io. Scrolling down to the “related” screenshots occasionally has some interesting findings:
Looking at some of the pages that talked to the AS, we can see at least one Telegram invite page (interesting, potentially C2 or just a redirect?), and we can see a number of news pages, I’ll drop a few screenshots below:
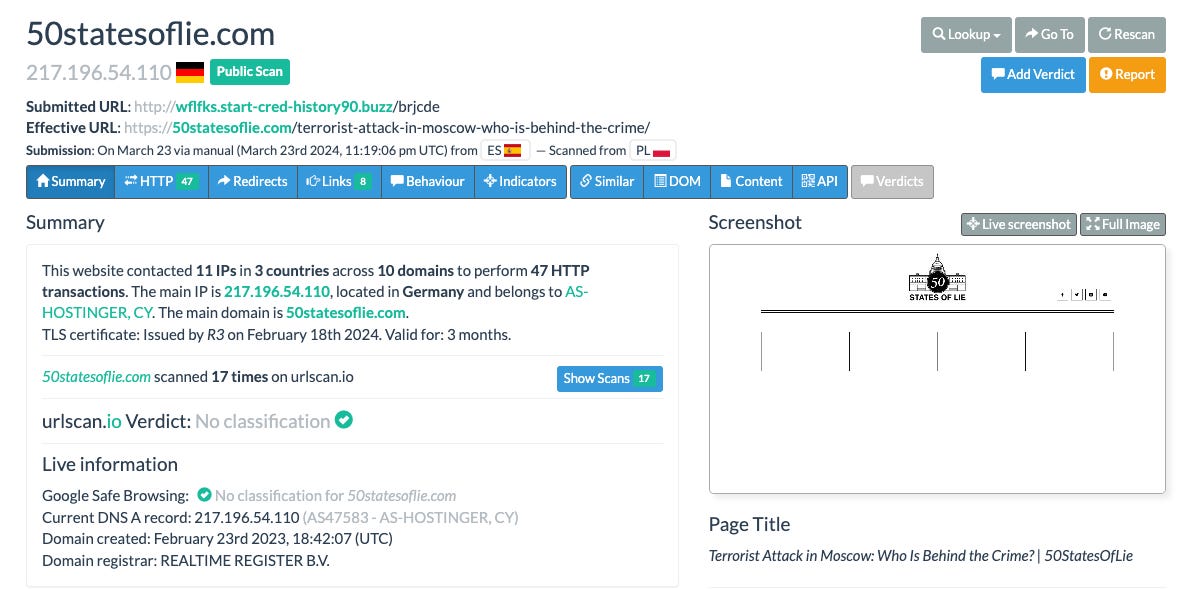
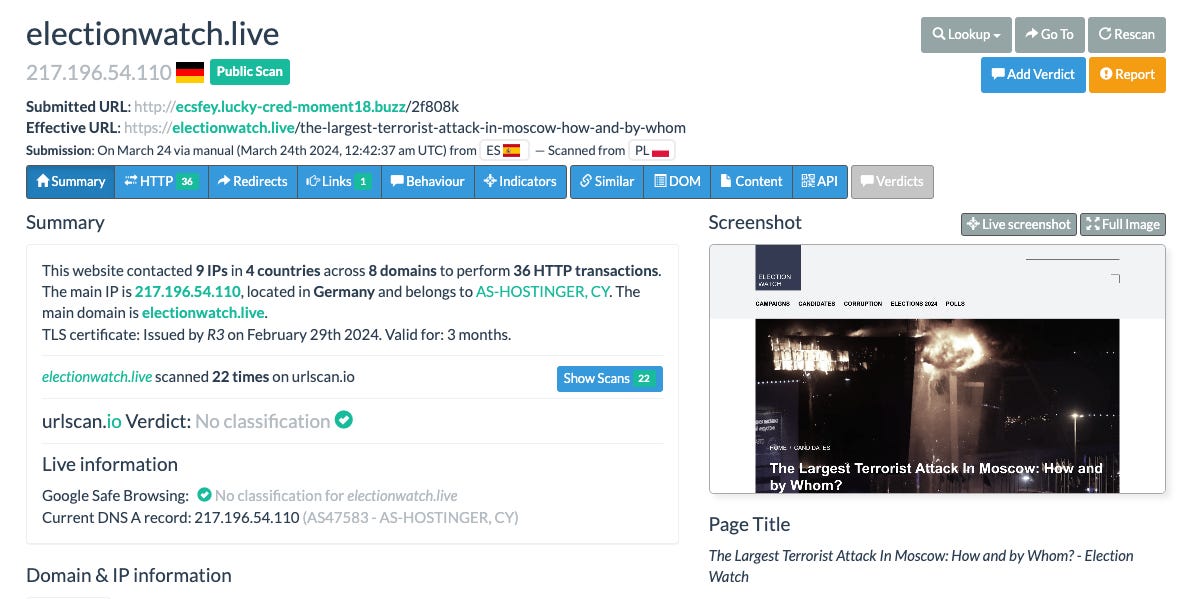
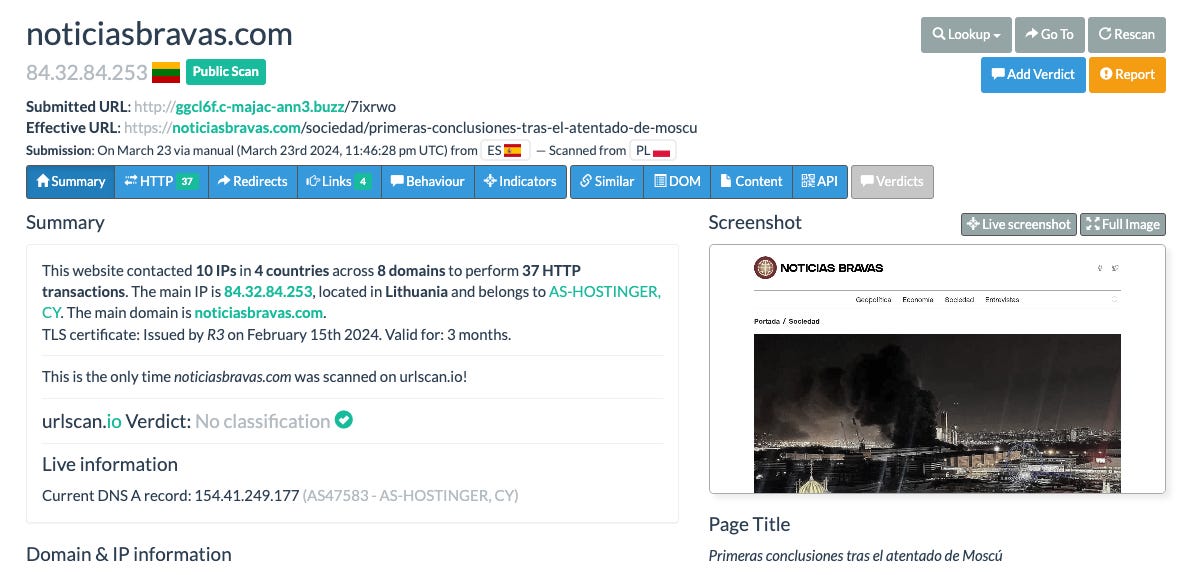
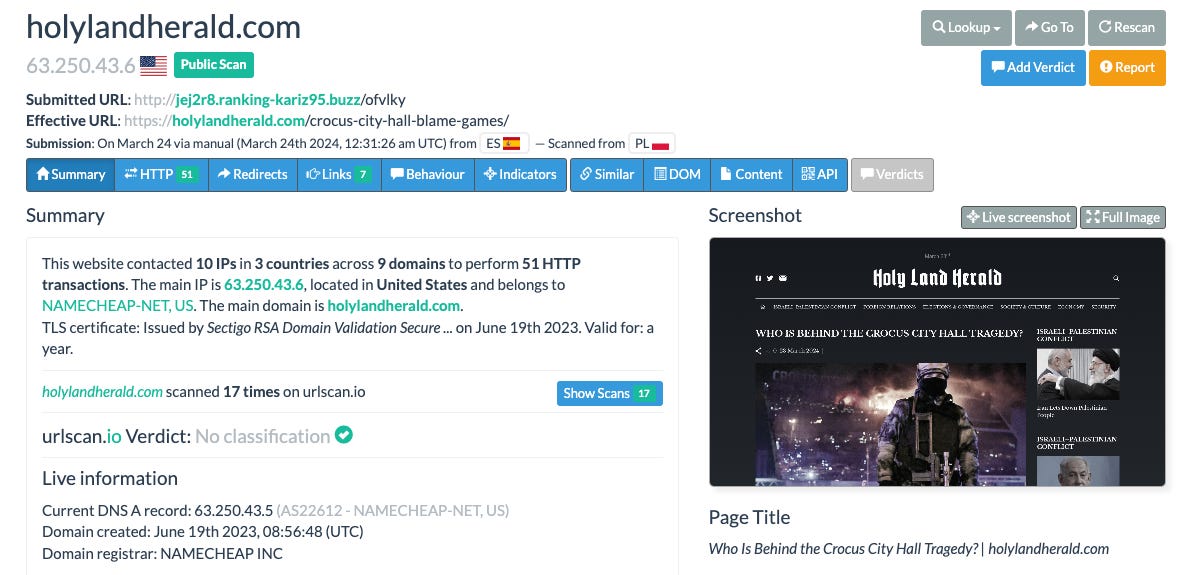
There are of course multiple more, but the especially eagle-eyed among you may have noticed that:
They all have similar page titles and headlines, focusing on the recent terror attack in Moscow.
One of them, Electionwatch, was outed by RF in their past Doppelganger report.
There are other unaffiliated pages as well, but this is only a small section of the sample - we can now safely begin to say that this activity is all Doppelganger-related. Holy Land Herald and 50 States of Lie were also mentioned in Meta’s Q3 adversarial threat report, although Noticias Bravas may be new.
So we now have an indication that these all talk to the ASN, let’s see how they actually do it.
Let’s go alllll the way back to the original host IP of the subdomain we first identified. We’ll now use one of URLScan’s best features: the ability to look up IP addresses that contact domains (as shown in recent RF research on Doppelganger that we’ve discussed in this blog)
There are a few interesting things to note. Firstly, we see the xsph domain recur with multiple captchas, potentially impersonating an investment domain with a fake login page. We can see a sample of some of the other domains that we’ve come across in the ASN as well as new ones - for example, “interventionist(.)us”.
Additionally, regarding the il-corrispondente domain, we can reach it by inputting one of the various subdomains belonging to a highly similar domain to our origin domain - see below. The same could be done by just opening the domain in URLScan and seeing what redirects to it.
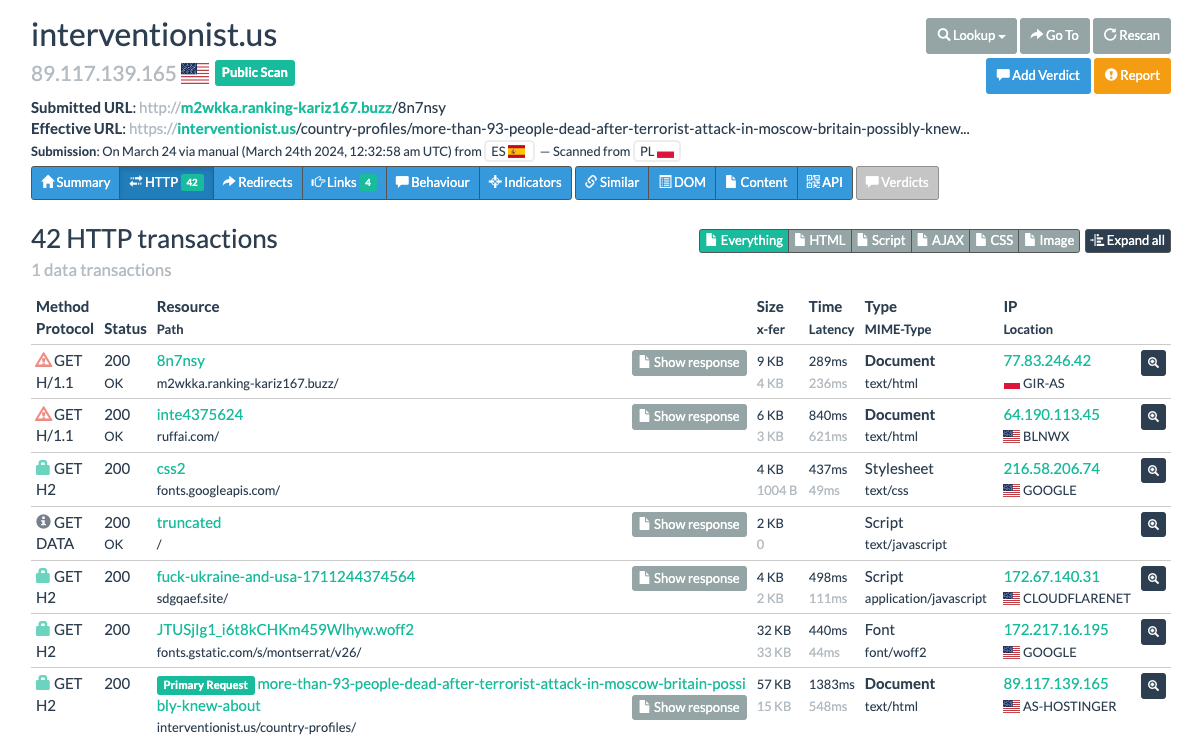
Going back to the results, let’s look at the Intervenionist domain results to see exactly how and why it contacts that IP:
So here we see that it contacts that IP by sending a GET request to the first domain we have there in the domain results. We have some other pearls worth looking at, such as the “fuck-ukraine-and-usa-1711244374564” script. Let’s start looking at some of the HTTP responses:
The first response includes content hosted on telegra.ph as reported by RF in their past research - so points in that direction.
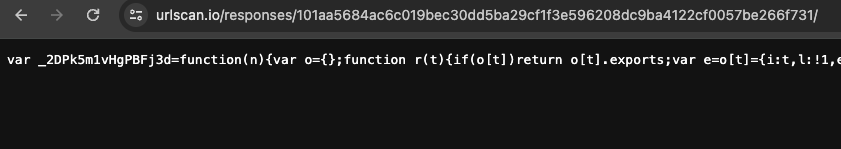
Let’s look at the other responses, and take a special look at the Ukraine/USA script. By the way, the domain it’s hosted on has been flagged by SentinelOne as a loader for Keitaro in the Doppelganger network.
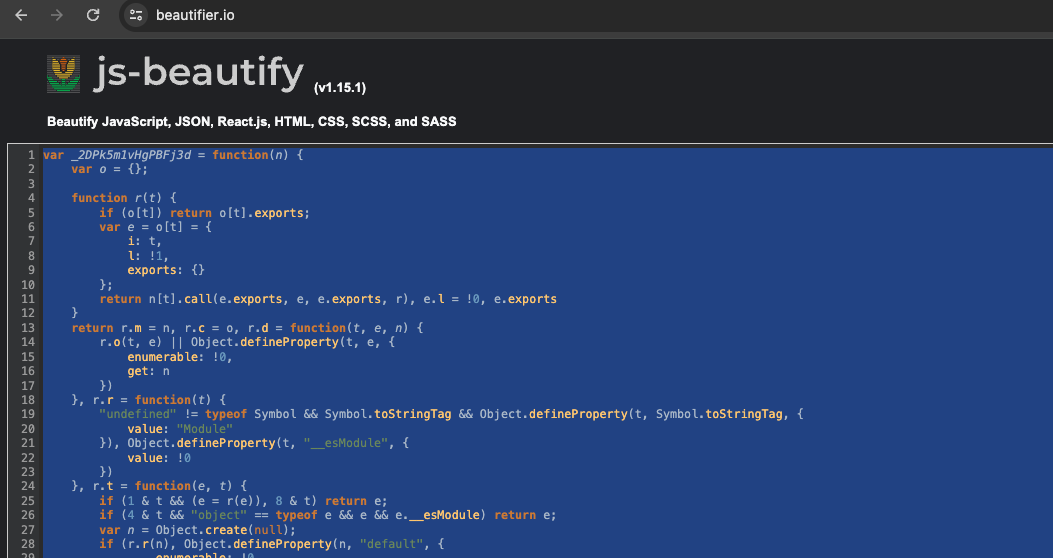
It’s long and cumbersome, and written in Javascript, which we know either by recognizing JavaScript, asking ChatGPT or noticing that it was listed as JS on the URLScan page.
From here, let’s beautify it:
Then, we can ask ChatGPT to tell us what it does:
This explanation jives with RF’s findings on how Doppelganger domains work.
We can now safely say that we have some Doppelganger shenanigans at foot here - from the shared TTPs, content similarities and infrastructure overlap. We can conclude here that the Doppelganger network will only continue to become fully unraveled over time.
From here we have multiple options:
Check for affiliated social media activity to see who/what is amplifying these domains
Further investigate each domain for OpSec slipups and further infra mapping
Take a break and revisit in the future (what I’ll do myself)
Hopefully this thought experiment showed how some of these tools can be used to comparatively easily (and without a very strong background in networking) carry out technical investigation of online infrastructure.
That’s it for this week then!