Memetic Warfare Weekly: Veni, Vidi, Vigi(num)
Welcome to Memetic Warfare Weekly.
My name is Ari Ben Am, and I’m the founder of Telemetry Data Labs - a Telegram search engine and analytics platform available at Telemetryapp.io. I also do training, consulting and research so if you have any specific needs - feel free to reach out on LinkedIn.
This week’s post will be dedicated to Viginum’s most impactful report of date on a network of Russian news “portals” dedicated to promoting pro-Russia content across Europe.
Portal Kombat
Wow, what a refreshing change of pace for me to not have to come up with a clever section title! Viginum did it for me this time with their new report on a sprawling Russian operation, and I truly hope that others up their naming game in response.
In short, this is a large, domain-centric Russian network that reposts content from other domains, promoting pro-Russia content and targeting European audiences and so on.
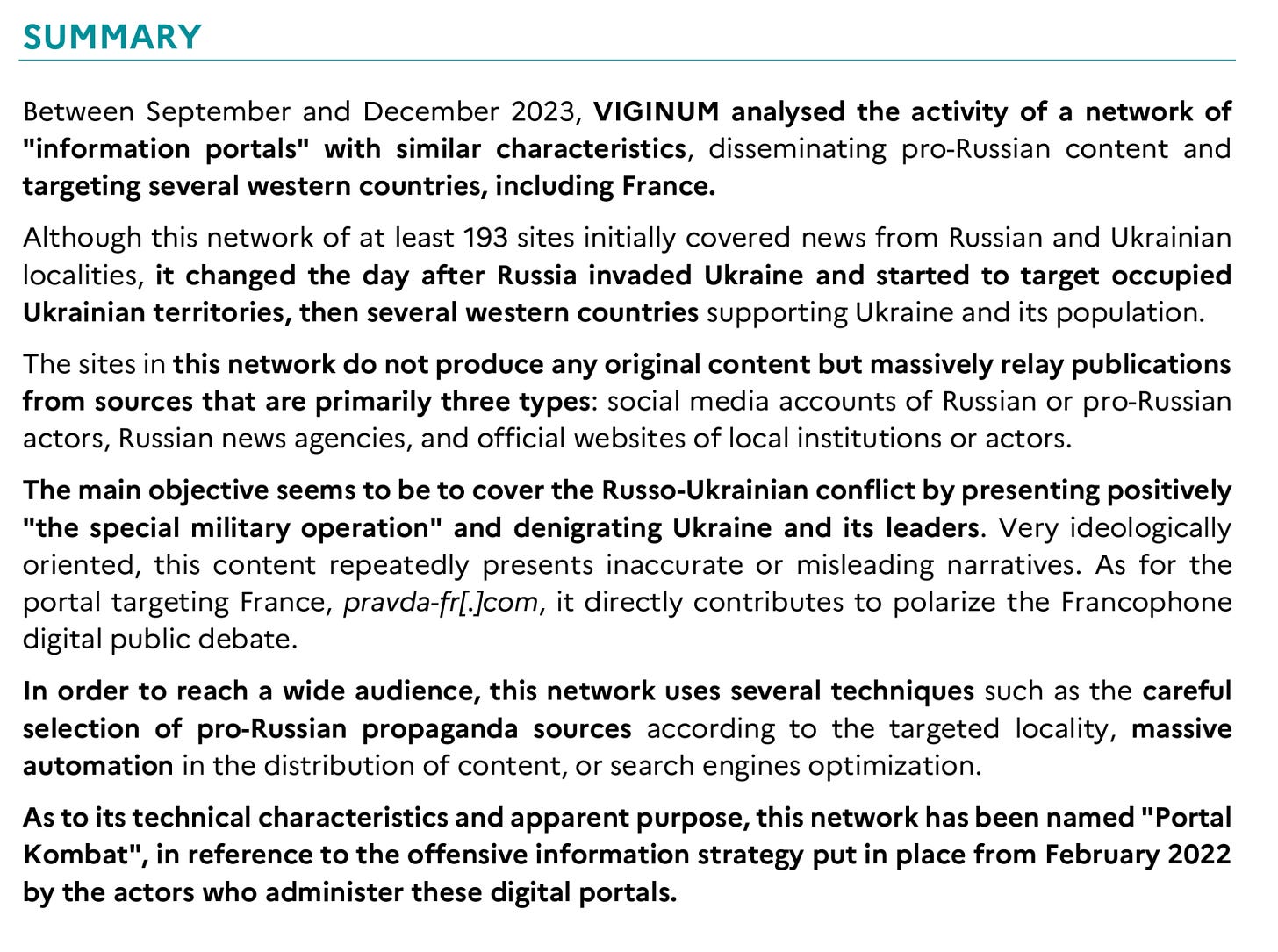
Nothing necessarily groundbreaking there, but I’ll put the executive summary below for convenience.
Also, while Viginum did a great job here (and we’ll discuss soon more of that in-depth), please invest in getting some English editing and proofreading done! It’s not the end of the world but I can’t help but be a stickler.
Before getting into the details, I’ll explain why I’m taking the time to go through this report in-depth and add commentary:
It’s a report from a new government agency on IO, which is a welcome development and I want to promote it as such.
The report is a fantastic place for those who are interested to learn basic to advanced domain analysis, as this is a domain-centric network and Viginum does a good job of explaining how they analyzed the various domains.
On that note, let’s begin.
Veni, Vidi, Viginum
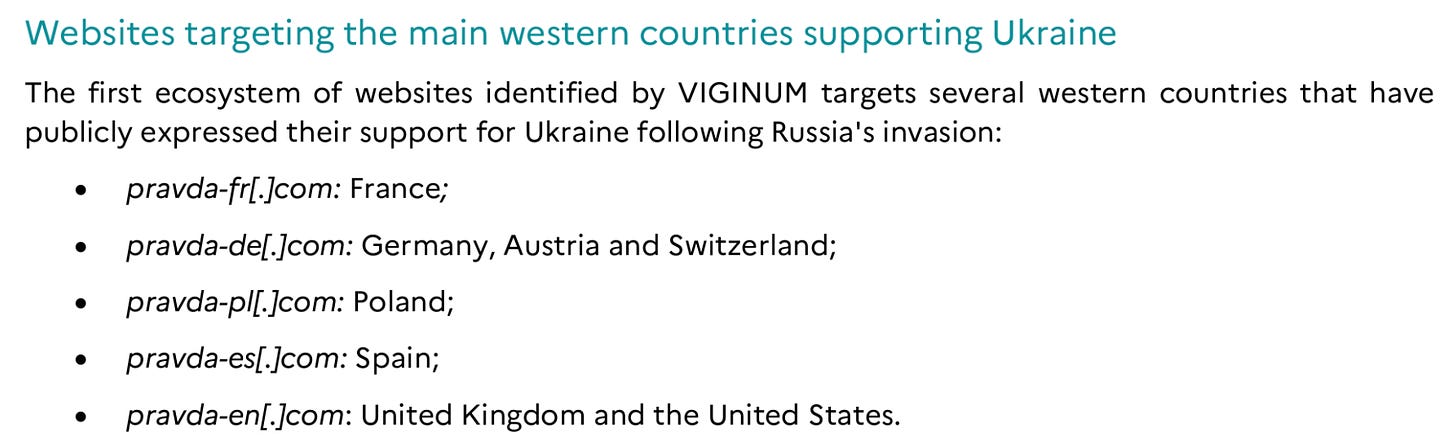
The report starts off by showing the initial cluster of domains identified by Viginum:
Unsurprisingly, they all share the well-known keyword “Pravda”. This would be a great example of how one could use domain registration monitoring tools, such as DNSLytics (a tool that I have no business ties with but am a big fan of, at least prior to them ruining their OG interface) to monitor a select set of keywords to come across leads.
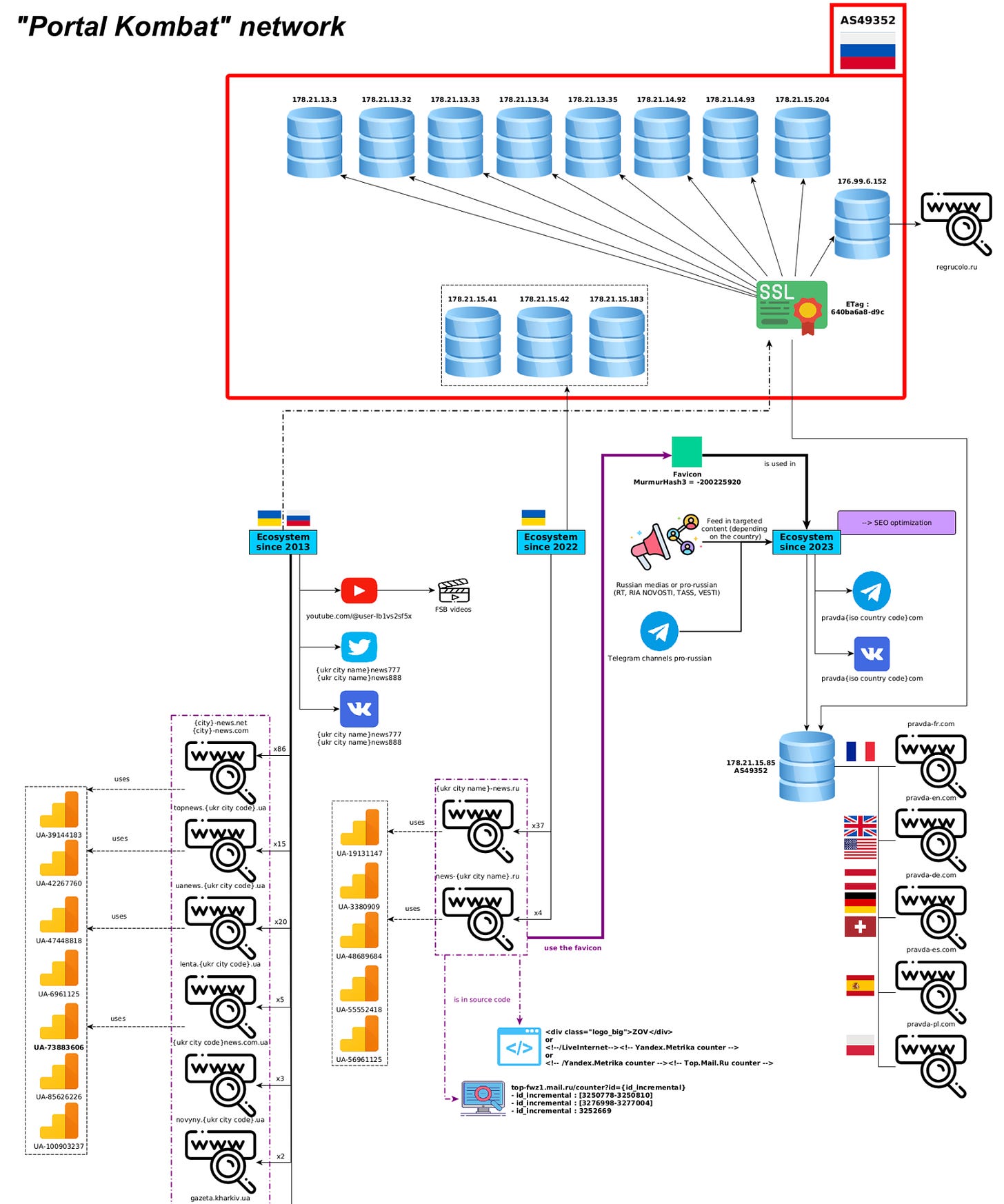
From there the indicators of coordination are obvious; all of them have similar names, were registered on the same day, are hosted on the same Russian server, have the same HTML architecture and style, links and more - the list goes on.
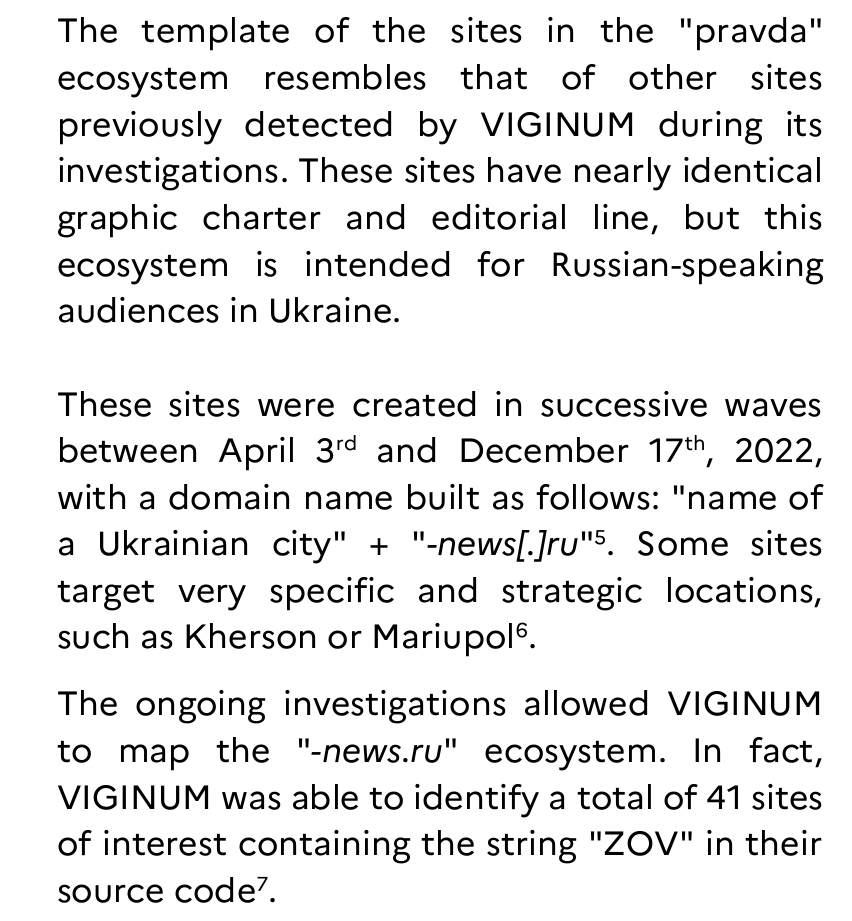
Viginum also came across another cluster, interestingly utilizing the same naming convention:
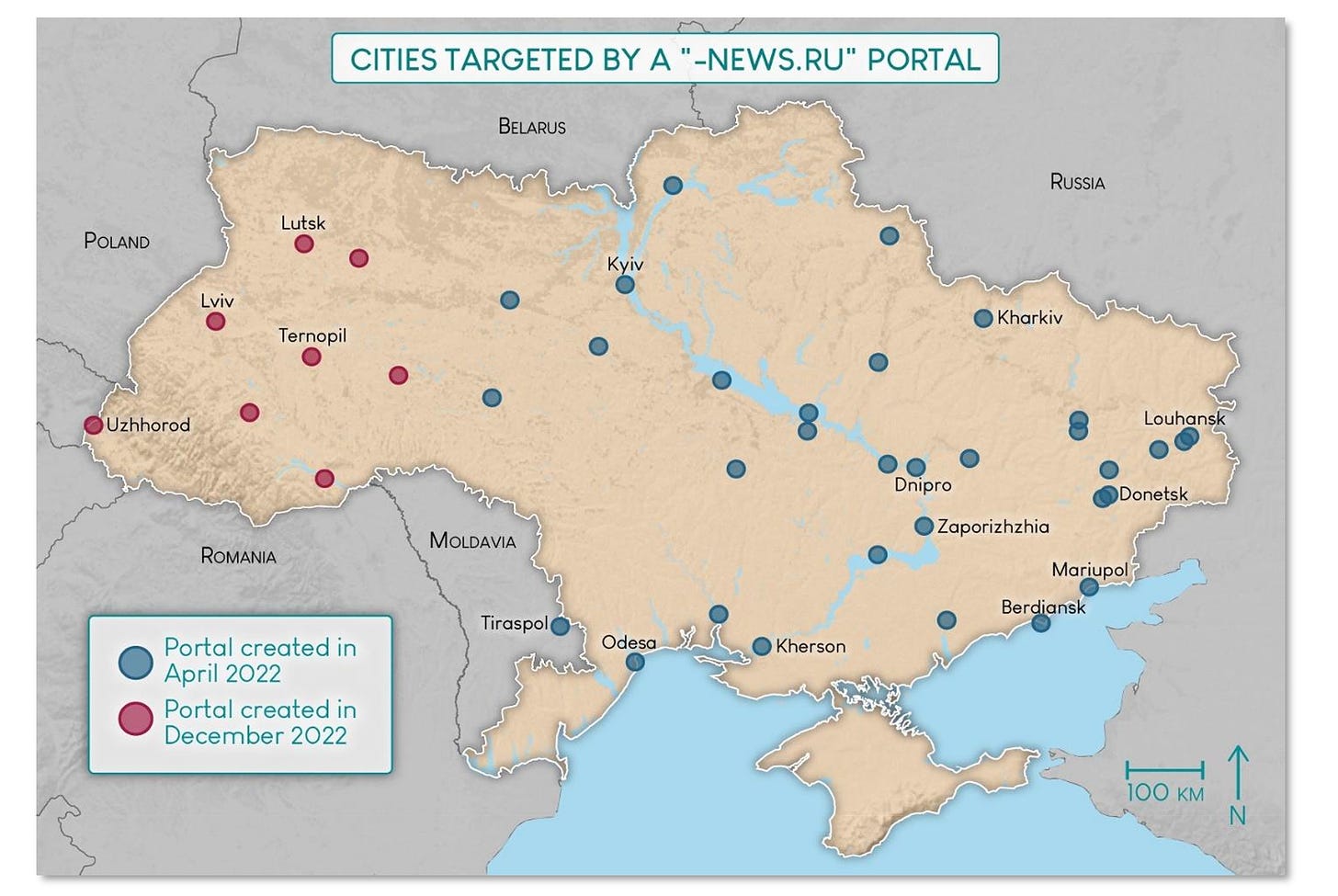
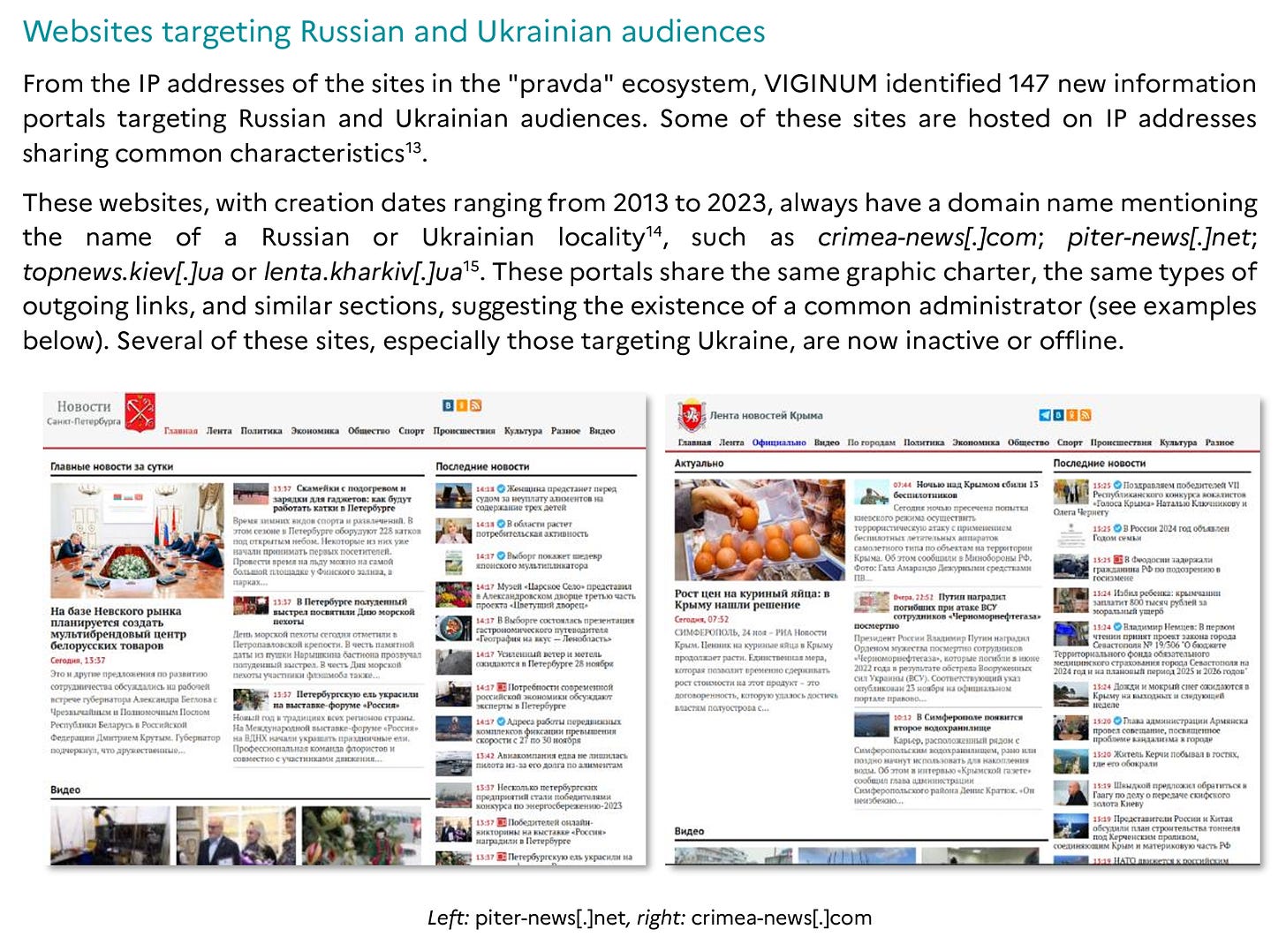
The network also focused on Ukrainian cities and regions:
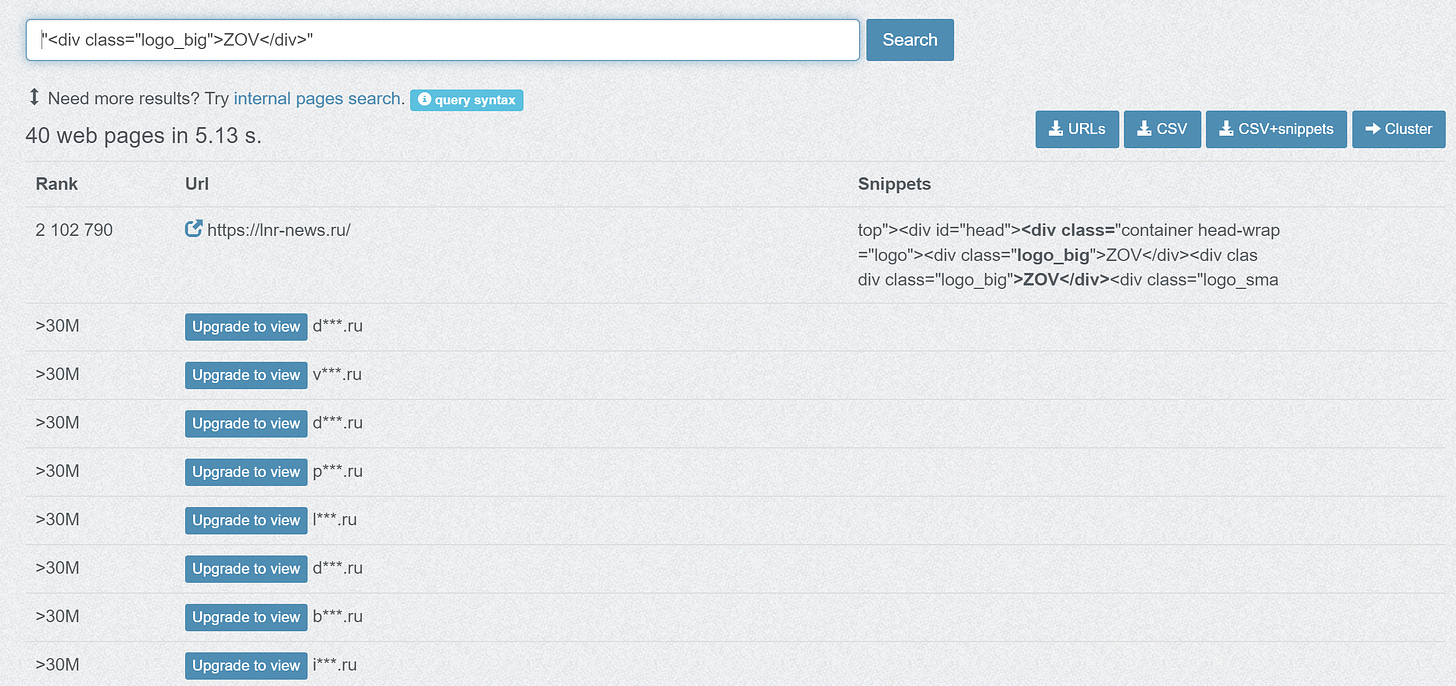
Searching the source code snippet in footnote number 7, “<div class="logo_big">ZOV</div>”, retrieves 40 web pages on PublicWWW, which may have been how Viginum retrieved their number of domains, as they have a similar number of domains identified when compared to the PublicWWW results.
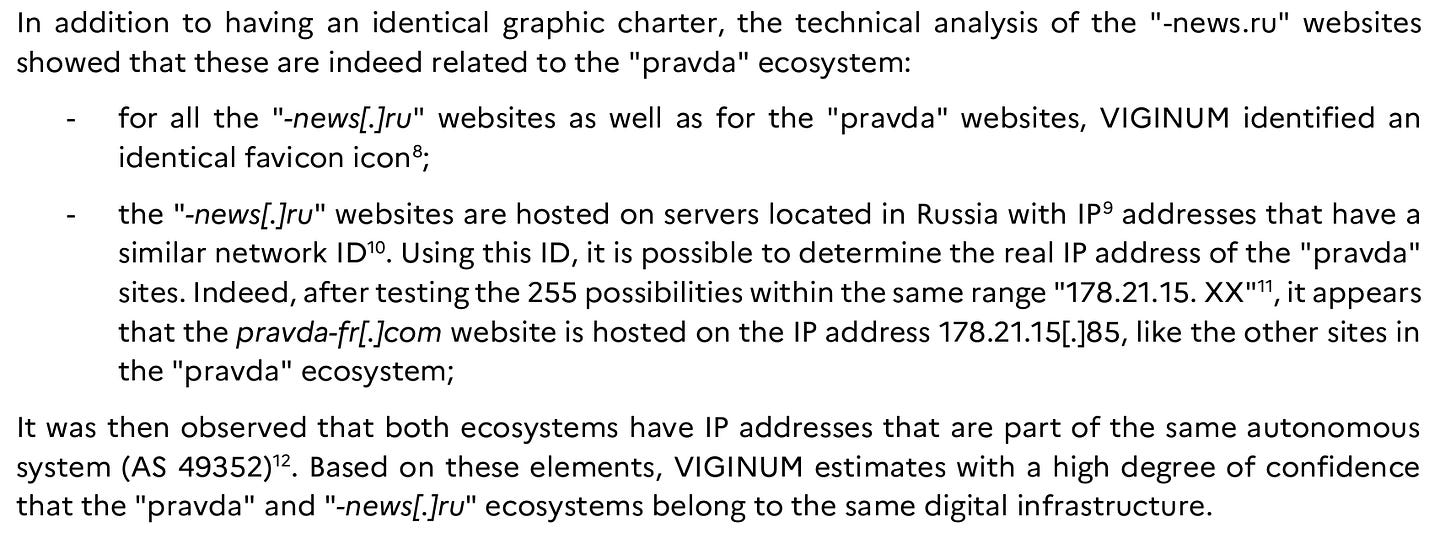
The fun doesn’t stop there though. Viginum takes it a step further and does a favicon hash search (one of my favorites), showing that all of the domains have identical favicons (a favicon being the little icon that you have in the browser tab for the sites you currently have open in your browser). Notably also, Viginum took the time to check the entire range of IP addresses available on the specific host servers looked at.
These hosts are all active IPs in the same ASN, leading Viginum to very reasonably conclude that these networks are run on the same infrastructure. The upside of identifying these given servers as being key, and most importantly proprietary, infrastructure for these networks is that you can then sequentially check each address hosted on the same server and find more network domains, which Viginum did:
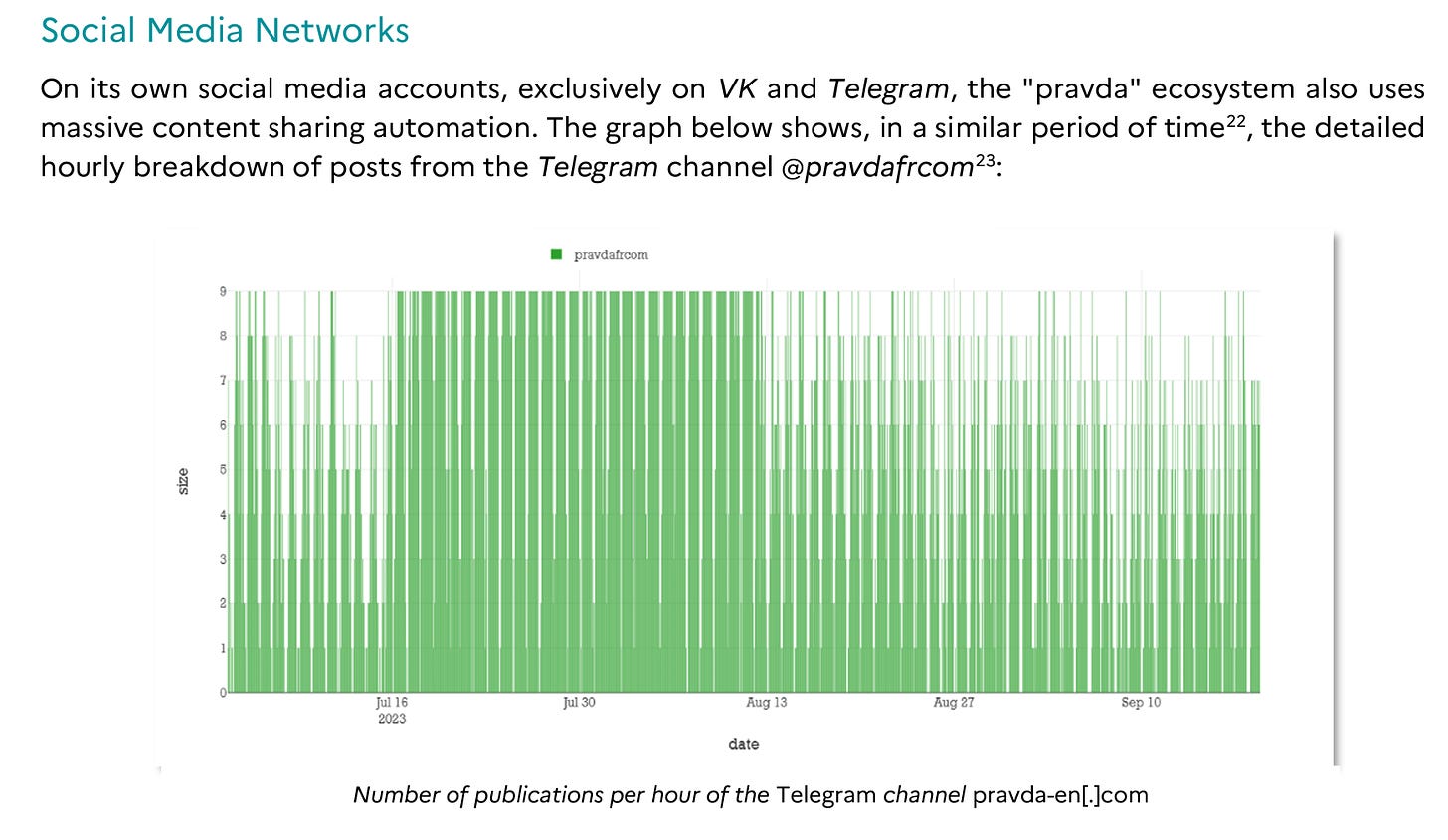
The network of course amplifies its content via Telegram and other social media platforms:
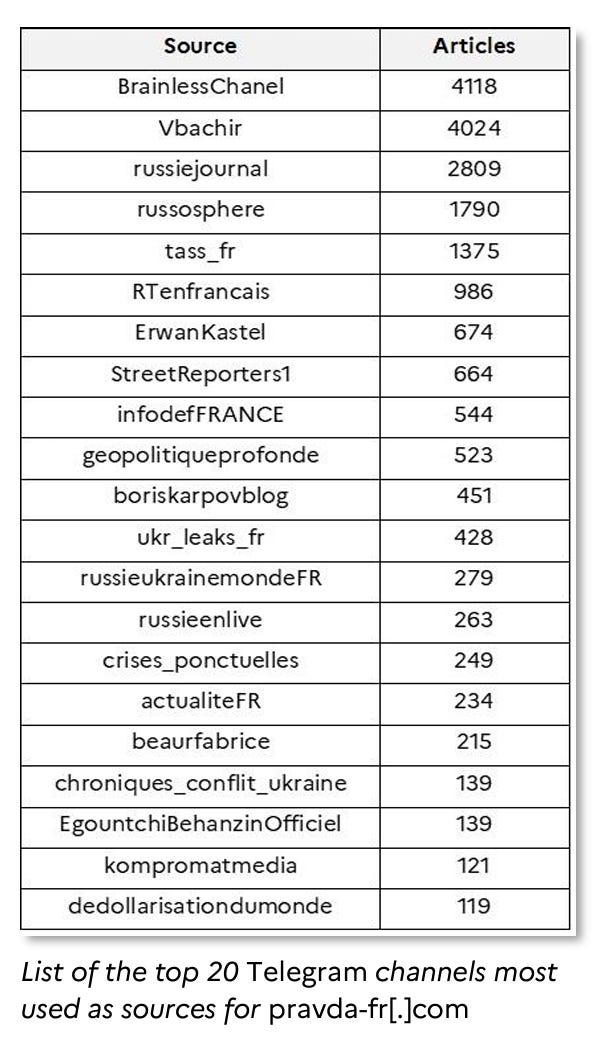
Telegram channels also served as a key source of content to repost and republish:
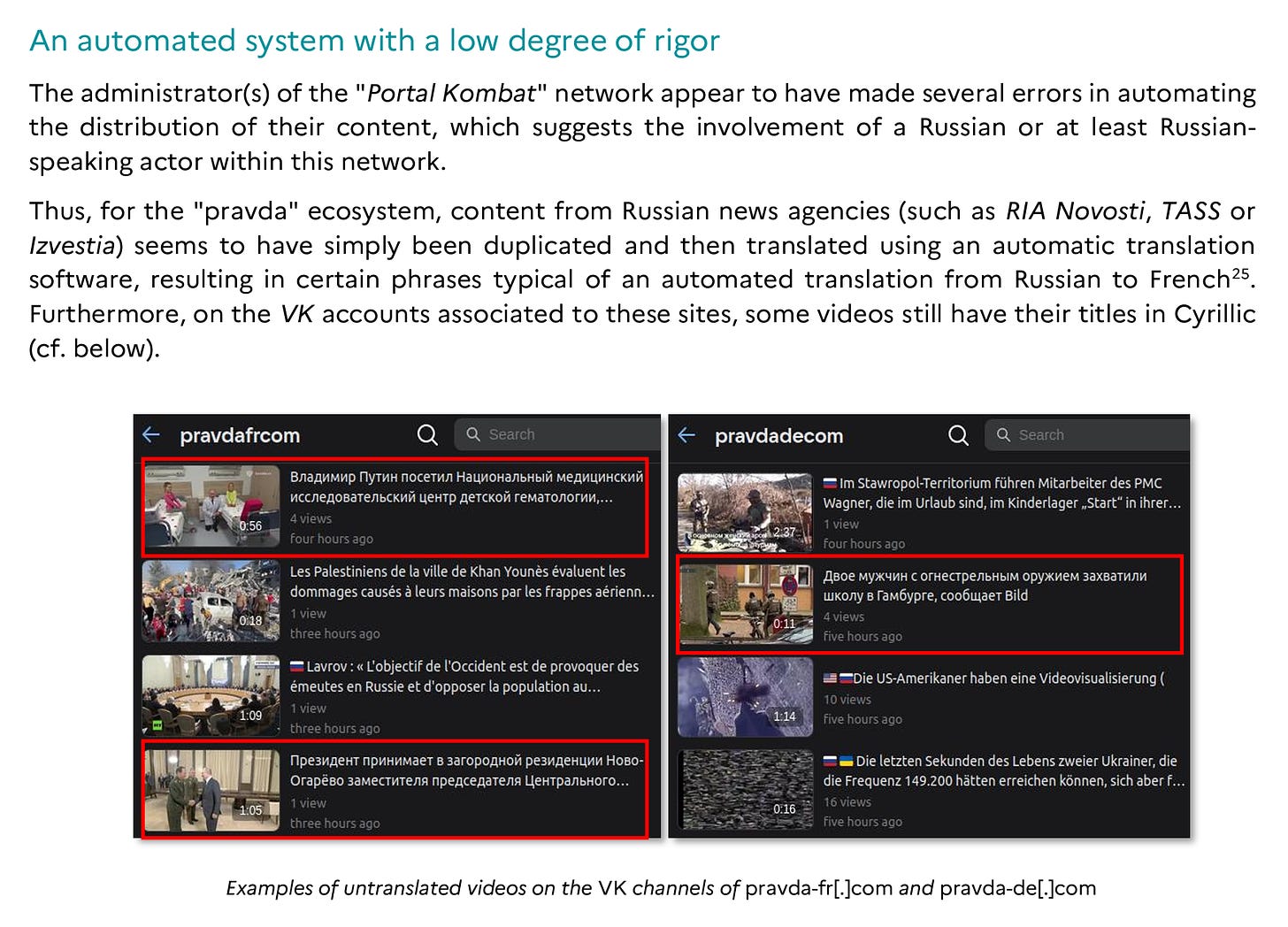
Shockingly, the network operators seem to not really care about OpSec or even doing a good job in translation. I don’t really understand why people still insist on believing that Russia is somehow a more advanced actor than say, China, when Russians have always and will continue to fumble the ball so frequently.
Wikipedia also makes a guest appearance:
This then takes us to the pièce de résistance of this report: the network graph. I’m not always a huge fan of network graphs, but if you’re going to make one, this is the way to do it: clearly delineated, with clear added value. No low-effort Gephi stuff please.
This graph is also a great learning resource for those want to dip their toes into domain analysis. We can review the below chart and even come across specific investigative techniques that weren’t explicitly mentioned in the report:
Complete the word: E-"(fill in here)”. The first thing to have come to mind may have been E-Girl, E-Cigarette, E-Mail or anything else really, but we’ll focus on a more niche E-entity, E-Tags.
Twitter user SttyK came up with a way to query unique E-Tags, part of a given host’s HTTP response, in tools such as Censys and Shodan. Here we see Viginum use the same technique, as pointed out by SttyK as well. Always great to see newer techniques implemented alongside older methods.
Beyond that - we really get to see all of the stops pulled out. Investigating and pivoting via Yandex Metrika and Google Analytics tags, source code searching, favicon searching and beyond. 10/10 stuff.
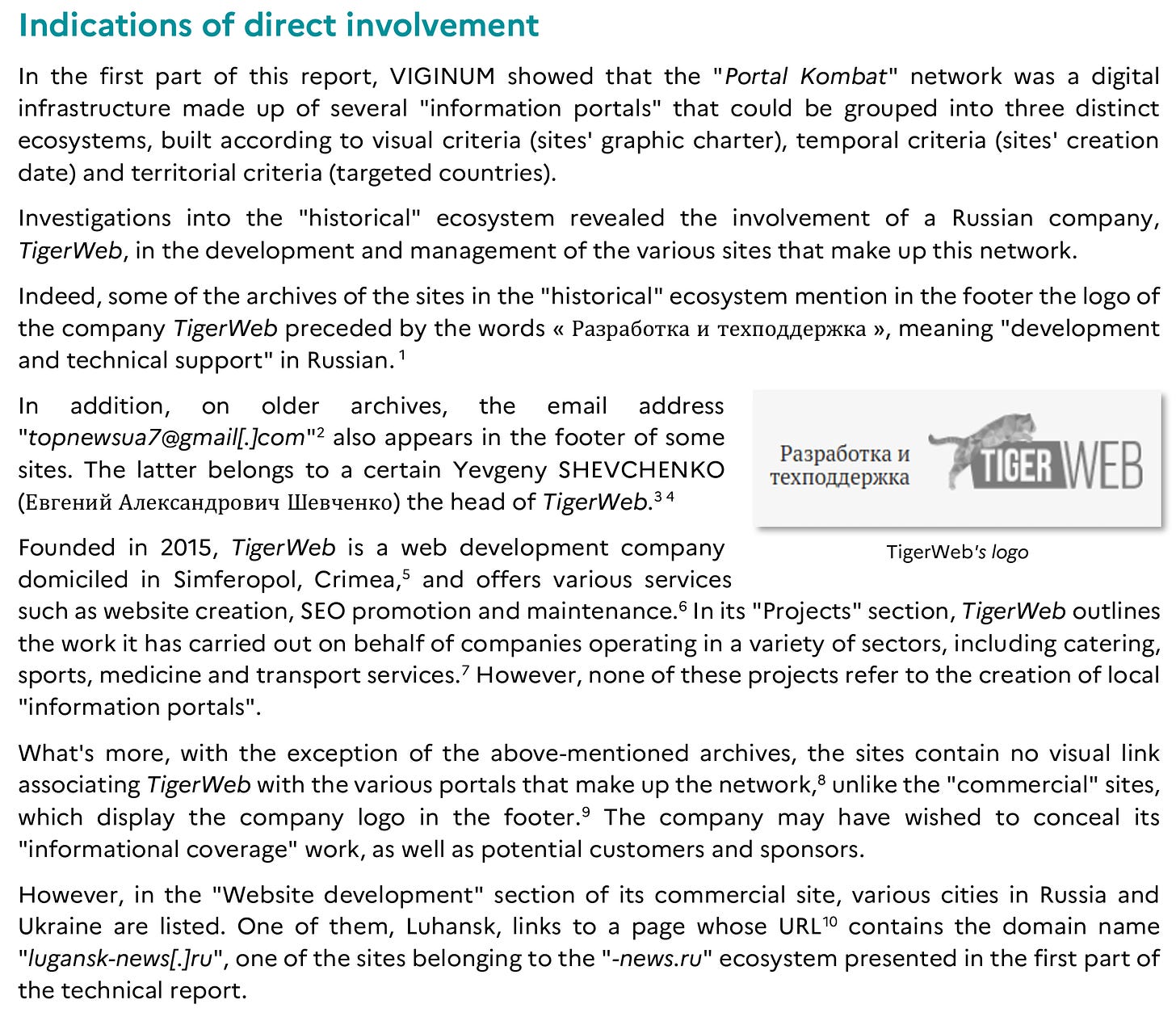
Viginum also was able to attribute the network to a Russian company via basic OpSec slipups found in the archived instances of network domains.
There’s more to the report, but we’re already past the usual length for our posts here, and I’d like to keep some content for those who take the time to investigate.
That’s it for this week!